The StateFarm Fire Safety Kit scam is a growing phishing campaign that impersonates State Farm and claims recipients have been selected to receive a free Fire Safety Kit. The message appears urgent, congratulates the recipient, and pushes them to click a confirmation button before supposedly limited supplies run out. Once clicked, victims are redirected through a chain of recently registered phishing domains that imitate surveys, loyalty rewards, and checkout pages. These sites request personal details, home addresses, phone numbers, and payment information under the false promise of a low cost processing fee. None of the emails or websites associated with this scam belong to State Farm.

The emails themselves vary widely. Scammers rotate through a large set of sender addresses to avoid detection and to appear more legitimate. Some of the addresses observed include:
info@q6qiusi.en7tpq3snsyjgakfyf7.uzm98g8hjxtizfmagqgenj.a50hmkaxvk4dg7bhjugwtotowja1hyktq7mx7b2wj6.dodrngtlufjb.malatyaeditor.com info@ap21yd.yhy13mspnap21yd.8igzjcvpom.com via sjmflex.com.my info@zyx9gthj6.gyn8k2tu.9pml2xllg.cbo3cn1oxpctcjm1kezcqd5u2ttc1udfx57rjh.p5fb0pl0vvce2gkzlxkog.citygate.co
These emails are not sent from a single server. Instead scammers make use of domain generation tools, anonymized hosting, compromised email relays, and foreign servers. The extreme length and randomness of the sending domains indicate an automated approach rather than a targeted one. Messages often include unsubscribe links and a United States mailing address to imitate legitimate marketing practices, but these details are generic and do not confirm authenticity.
How the Scam Operates
Clicking any confirmation button in the email redirects the victim to a fake survey page. In this campaign, one of the primary survey hosts is purelynx.win. The page displays simple multiple choice questions that appear unrelated to the alleged safety kit. None of the answers matter. The purpose of the survey is psychological rather than functional. Victims are more likely to trust the process after clicking through a few steps, and they become more invested in receiving the advertised reward.

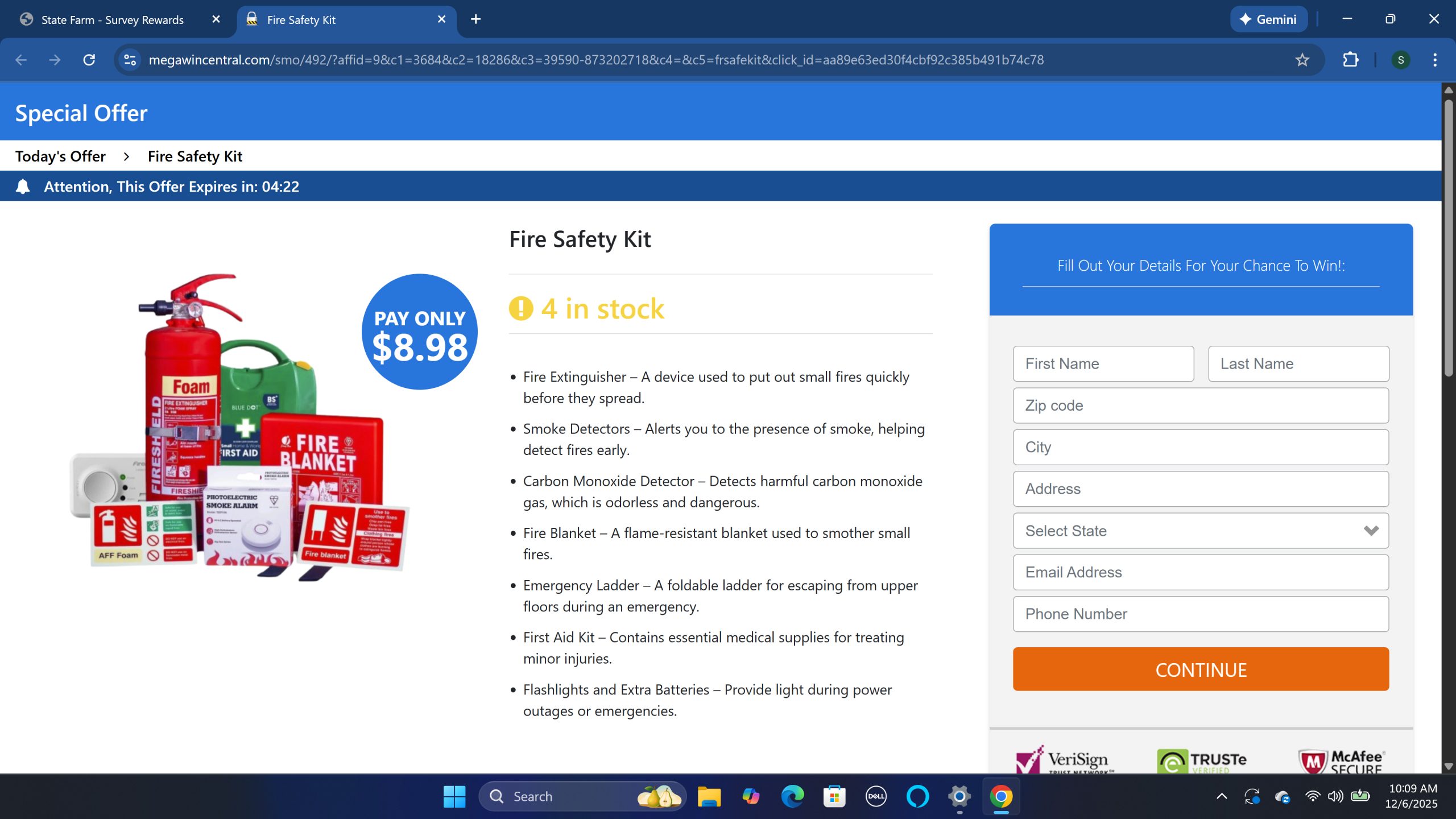
Once the survey is completed, the victim is shown a reward page stating they now qualify for a Fire Emergency Kit. The kit is presented with stock images of extinguishers, blankets, smoke detectors, and first aid supplies. The page claims the kit normally has a retail value and that it is being offered for free except for a small handling fee. Timers, scarcity warnings, and highlighted buttons reinforce urgency and reduce the likelihood of second thoughts.

The final step redirects the victim to megawincentral.com, a fraudulent checkout site where they are asked for their personal information and payment card number. Although the fee is small, the value of the stolen information is high. Contact information allows scammers to target victims again in the future, while payment card numbers may be sold or used immediately.
The Domains Behind the Scam and What WHOIS Reveals
The domains used in this scam provide significant evidence of its fraudulent nature. The first domain, purelynx.win, was registered on October 29, 2025 and expires exactly one year later. Its WHOIS information is fully hidden by a privacy service, and its status fields show clientTransferProhibited and serverTransferProhibited, which is standard for newly registered domains. The short registration window, recent creation date, and use of WHOIS privacy strongly suggest temporary use in a phishing operation. Legitimate organizations rarely rely on one year disposable domains for customer programs.
The second domain, megawincentral.com, was registered on June 2, 2025. It uses a registrar that is commonly associated with anonymous hosting and includes full WHOIS privacy. Although older than purelynx.win, its combination of privacy masking and minimal historical footprint matches patterns seen in reward based phishing networks. The site performs no legitimate commercial activity and exists solely as a data capture endpoint.
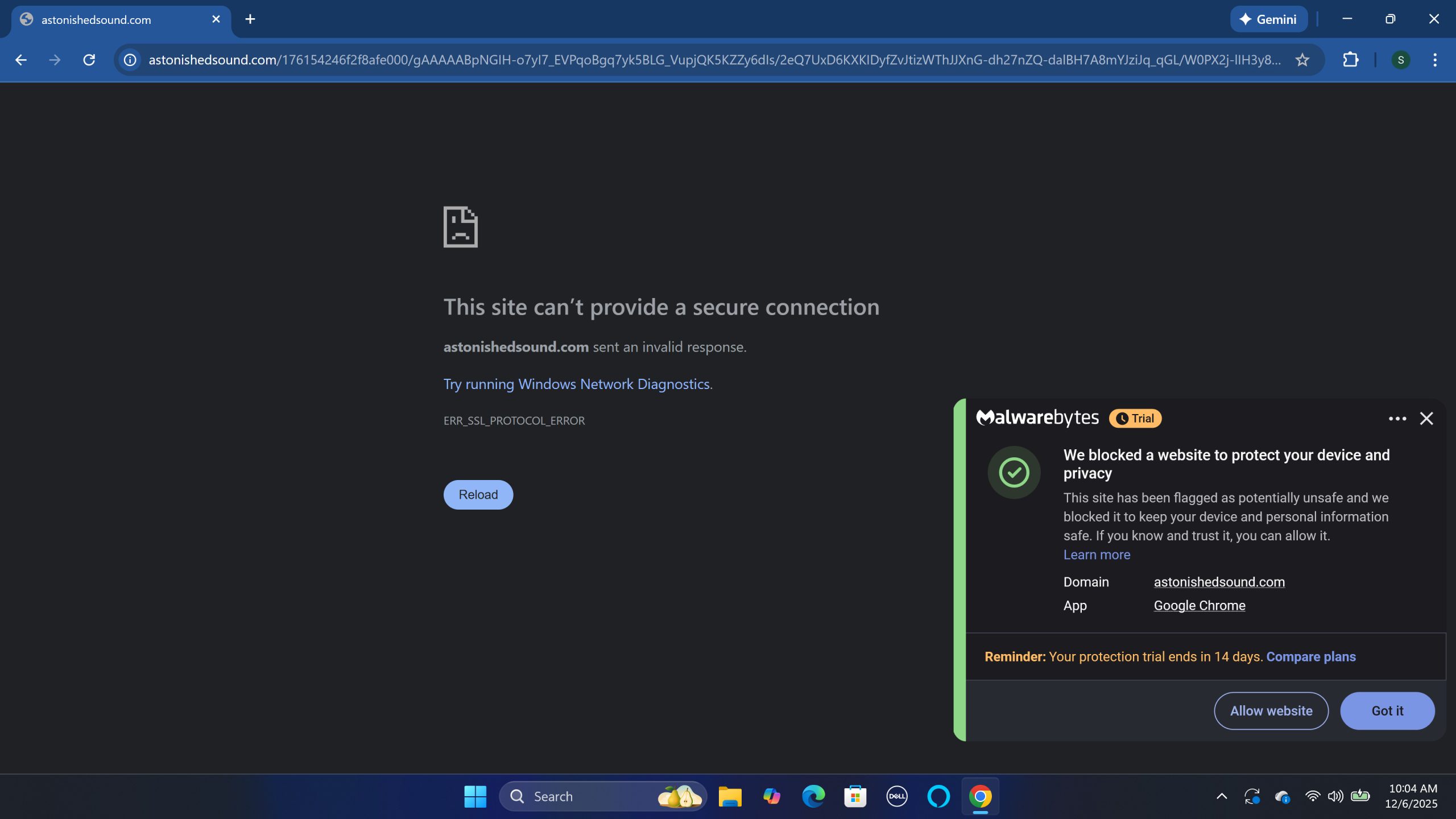
The redirect domain astonishedsound.com has been online since 2021, but longevity does not mean legitimacy. Malwarebytes real time protection blocks this domain, identifying it as unsafe. Older domains are sometimes purchased on secondary markets or reused by scam groups because they appear more trustworthy than recently registered domains. The fact that security software flags it provides additional confirmation that the infrastructure behind this scam is unsafe.
Taken together, the WHOIS records show a pattern of rapidly deployed domains, privacy masking, and registration through companies often used by anonymous operators. These traits do not prove criminal activity on their own, but in the context of a fake reward scam, they help illustrate the structure and intent of the operation.
Why Scammers Use This Structure
The multi step process in the StateFarm Fire Safety Kit email scam is intentional. The initial email pulls the victim in with urgency. The survey step increases engagement and gives the illusion of legitimacy. The reward page mixes psychological triggers like scarcity and time pressure. The checkout page uses a small fee to lower suspicion while capturing valuable financial information. This layered approach is designed to reduce friction and make the victim feel committed to completing the process.
By separating each stage across different domains, scammers make it harder for email systems and browsers to immediately flag the activity as dangerous. If one domain is blocked or taken offline, others remain active, allowing the campaign to continue.
What To Do If You Interacted With This Scam
Victims who clicked links or provided information should take several steps to protect themselves. First, run a full system scan with reputable security software such as Malwarebytes. While the scam is primarily designed to steal information rather than install malware, some redirect points may expose devices to additional threats. A full scan can identify and remove unwanted software, browser hijackers, or scripts that may have been introduced during the process.
If payment information was submitted, contact your bank or card issuer immediately. Explain that your information may have been exposed and request a new card number. Monitor all recent transactions for unauthorized activity. Many banks can also set temporary fraud alerts or additional verification checks on your account.
If you entered your email, address, or phone number, expect an increase in phishing attempts, spam, and unsolicited calls. Scammers frequently sell or share collected information. You may want to enable spam filtering tools and consider using a separate email account for purchases to reduce exposure.
Change passwords for accounts that share the same email address used during the scam interaction. Even though the scam focused on payment information, stolen contact data may be used for credential stuffing or future phishing attempts.
Finally, delete all related scam emails and empty your trash folder to prevent accidental reengagement. Remaining alert and skeptical of unsolicited reward offers is the strongest long term defense against similar attacks.
The StateFarm Fire Safety Kit email scam demonstrates how common brand impersonation, survey based social engineering, and disposable domains continue to be effective tools for cybercriminals. Consumers should verify offers directly on official company websites and treat reward emails with caution, especially when they request personal or payment information.
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
- OneDrive Email Scam: How It Works, Warning Signs, and How to Stay Protected
- Women and Children Support Foundation Email Scam Promises Fake $1 Million Donation
WordPress Bot Protection
Bot Blocker for WordPress
Monitor bot traffic, review live activity, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress dashboard.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







