The Rockstar Games data breach has been confirmed after the company acknowledged that a limited amount of non-material company information was accessed in connection with a third-party data breach, adding a new high-profile incident to the growing list of major data breaches linked to cloud integrations and external service providers. The threat actor ShinyHunters claimed the intrusion involved Rockstar data stored in Snowflake and said the access path came through Anodot, a business analytics and cloud monitoring platform. Public reporting and leaked file listings point to a large dataset centered on internal analytics, KPI reporting, support-ticket metrics, fraud-related references, and operational business intelligence rather than player-facing game assets or consumer account data.
That distinction is important, but it should not be confused with irrelevance. Rockstar characterized the exposed information as non-material and said the incident had no impact on its organization or players. Even so, an intrusion that reportedly exposed tens of millions of internal records still raises serious questions about third-party risk, access boundaries inside cloud analytics ecosystems, and how companies decide what is important enough to disclose with urgency. Data does not need to contain gameplay footage, passwords, or source code to matter. Internal performance metrics, support analytics, fraud-model references, and business reporting can still reveal valuable operational insights, internal structures, monetization patterns, and security priorities.
The Rockstar Games data breach also highlights a broader problem that keeps repeating across large organizations. A company can invest heavily in protecting its own environment and still face exposure through a connected analytics provider, cloud integration, or token-based trust relationship that attackers are able to exploit indirectly. That is one reason this incident deserves attention even if the leaked material appears underwhelming to players hoping for GTA 6 details or sensational internal secrets. From a cybersecurity standpoint, the more important story is how a major game publisher was pulled into a third-party data theft chain and then publicly downplayed the impact after the data began circulating.
Background on the Rockstar Games Data Breach
Rockstar Games is one of the most recognizable names in the video game industry, with franchises such as Grand Theft Auto and Red Dead Redemption carrying enormous commercial value and cultural reach. Any breach involving Rockstar will naturally draw attention because of the company’s history, the anticipation surrounding Grand Theft Auto VI, and the obvious market interest in unreleased content. That background can also distort how the public reads an incident. When players hear about a Rockstar breach, many assume the only meaningful possibilities are source code theft, gameplay leaks, or customer account exposure. This case appears different.
The available evidence indicates that the Rockstar Games data breach was tied to a third-party analytics path rather than a direct compromise of Rockstar’s primary game-development systems. Public reporting attributes the incident to ShinyHunters, which claimed access to Rockstar-linked Snowflake data through Anodot. Rockstar later confirmed that some company information had been accessed as part of a third-party data breach and said the exposed information was limited and non-material.
That phrasing matters because it reflects a very specific type of corporate response. The company did not deny the breach. It acknowledged the event while narrowing the perceived impact. In practice, that means the incident was real enough to confirm, but the company wants to make clear that the exposed material did not disrupt operations, endanger players, or rise to the level of a crisis affecting core business continuity. Whether that framing fully satisfies public scrutiny is a separate question.
The Rockstar Games data breach comes with added context because Rockstar is not new to security incidents. The company dealt with a major breach in 2022 that resulted in the leak of Grand Theft Auto VI development footage. That earlier incident was highly visible, highly embarrassing, and directly tied to unreleased game material. The current case appears narrower and more administrative, but it still underscores how valuable gaming companies remain to extortion groups and intrusion crews, especially when third-party infrastructure offers indirect access to business data.
Scope and Composition of the Exposed Data
The most important thing to get right about the Rockstar Games data breach is the nature of the leaked information. Based on the reported file listings and analysis of the circulating material, this does not appear to be a consumer account dump, a GTA 6 asset leak, or a catastrophic exposure of player credentials. Instead, the data appears to center on internal analytics and business reporting.
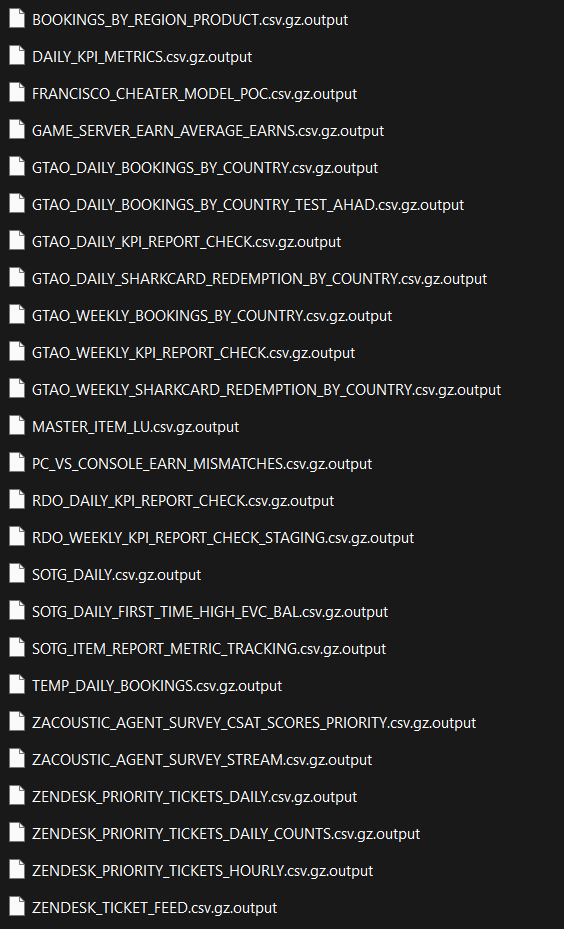
The leaked file names shown publicly point in that direction very clearly. They include references to KPI metrics, bookings by region and country, weekly and daily reports, item lookup datasets, earning averages, support-ticket reporting, customer satisfaction survey streams, and fraud or anti-cheat related model testing. There are also references to Zendesk priority ticket data and internal reporting tied to Grand Theft Auto Online and Red Dead Online. In plain terms, the exposed material looks much closer to business intelligence and service analytics than to the kind of content most fans associate with a Rockstar breach.
Internal analytics can expose how a company monitors live services, how it measures customer behavior, how it tracks monetization, where support pressure is highest, which regions produce certain types of bookings or engagement, and what kinds of fraud or cheating patterns are important enough to model and measure. Support datasets can also reveal operational workflows, escalation patterns, performance targets, and issue categories that attackers or competitors may find useful. Even if the data lacks direct player credentials or development assets, it can still provide a revealing map of how the company operates.
Another important point is scale. Public reporting has tied the breach claim to roughly 78.6 million records. That number should be treated carefully because it reflects the claimed scope of the exposed data rather than a confirmed count of affected people. In analytics environments, a record count can refer to entries, logs, events, aggregates, or operational rows that do not map neatly to unique individuals. Still, the volume suggests the incident was not trivial. Even a dataset that is mostly administrative can become consequential when it is broad enough to reveal internal structures and service patterns at scale.
Why Rockstar Appears to Be Downplaying the Incident
Rockstar’s public position is easy to understand from a corporate communications standpoint. If the exposed data is truly limited to non-material company information and does not include player credentials, financial account access, or unreleased core assets, the company has every incentive to prevent the story from escalating into a perceived crisis. Publicly emphasizing that there is no impact on players is a way of containing panic and separating this breach from the far more dramatic 2022 incident.
At the same time, downplaying a breach does not eliminate the significance of the underlying event. It only narrows the company’s own framing of what matters. Companies often reserve stronger language for incidents involving customer data, business interruption, payment risk, or protected intellectual property. That means a large exposure of internal analytics may be treated as operationally manageable even if it still reveals sensitive information about support systems, fraud detection, revenue patterns, or internal reporting practices.
This is where the Rockstar Games data breach becomes more interesting from a security perspective than from a fan perspective. The public reaction on social platforms has largely fallen into two camps. One side treats the breach as proof of another serious compromise at Rockstar. The other side dismisses it as boring because the leaked files do not appear to contain the kind of dramatic content people were hoping to see. Both readings miss the more useful middle ground. The data may be underwhelming as spectacle while still being meaningful as evidence of a real cloud-linked exposure affecting a major publisher.
Rockstar’s response also suggests the company believes the practical risk is bounded. If the organization thought the incident materially affected players, core operations, or critical internal secrets, the tone and urgency of its statement would likely be very different. That does not mean the company is hiding a larger disaster. It means the breach appears to fall into a category that organizations often classify as limited but still regrettable: real unauthorized access, embarrassing public exposure, but no immediate operational or consumer crisis.
Third-Party Risk and the Anodot Connection
The most important structural lesson from the Rockstar Games data breach is that third-party analytics and cloud integrations can create serious exposure paths even when the primary target is not directly breached in the traditional sense. Public reporting on this incident indicates that attackers leveraged a compromise tied to Anodot, an analytics and cloud monitoring platform, to access connected Rockstar-linked data in Snowflake.
That kind of access path is exactly why third-party risk remains one of the hardest problems in enterprise security. Companies do not operate in isolation. They connect cloud data warehouses, analytics platforms, support tools, telemetry systems, anomaly detection services, dashboards, data pipelines, and storage environments across a dense web of vendors and integrations. Every connection creates convenience, visibility, and business value. It can also create inherited trust that attackers may exploit.
When an external service holds authentication tokens, integration permissions, or privileged access to cloud data, the compromise of that service can become a compromise multiplier. Attackers do not need to defeat every target one by one if they can instead abuse the relationships that already exist between platforms. That is what makes incidents like this so important. The weak point may not be the publisher itself. It may be a service in the analytics chain that has enough access to expose meaningful data once it is abused.
For gaming companies, this is especially relevant because modern live-service operations generate enormous volumes of telemetry and depend on equally large analytics ecosystems. Game publishers track player behavior, monetization, support trends, fraud indicators, event performance, churn signals, regional activity, and numerous other business metrics in near real time. The more that infrastructure is integrated with third-party analytics layers, the more critical token security, role scoping, service isolation, and vendor governance become.
Risks to Rockstar, Partners, and the Public
The immediate public risk from the Rockstar Games data breach appears limited compared with incidents involving passwords, payment cards, or direct consumer identity data. Rockstar has said there is no impact on players, and the reported nature of the leaked data supports the idea that this was mainly a business-data exposure. That said, the absence of direct player harm does not mean there is no downstream risk at all.
For Rockstar, the main risks include reputational damage, unwanted visibility into internal business operations, exposure of support and service structures, and the possibility that fraud-related references or reporting models could provide useful context to abusers. Internal metrics can also aid future social engineering if attackers learn how the company names reports, routes support issues, or measures internal categories. Seemingly dry administrative data can become more valuable when combined with other leaks, other breaches, or employee-targeted phishing.
For partners, there may be concern about what kinds of contracts, reporting views, or service relationships were indirectly exposed through analytics environments. Even where partner-specific details are not obvious in the leaked data, a breach tied to shared cloud systems can trigger questions about where other data lives, who can access it, and how safely it is segmented.
For the public, the biggest issue is less about direct harm and more about precedent. A major publisher can suffer unauthorized access to a large internal dataset through a third-party analytics path and still tell the public that the incident is non-material. That may be true in the narrow sense of immediate player impact, but it also shows how normalized cloud-linked exposures have become. The practical lesson is that not every serious breach looks dramatic. Sometimes the most important part of the story is the path of access, not the splashiness of the leaked content.
Possible Initial Access and Attack Pattern
Based on current reporting, the Rockstar Games data breach appears to fit a pattern in which attackers abused trust relationships inside a cloud analytics ecosystem rather than breaking directly into Rockstar’s own infrastructure in a simple standalone hack. The reported chain points to Anodot, with the attackers allegedly using compromised authentication material to access connected Snowflake data.
That matters because it reflects a modern enterprise intrusion model. Instead of targeting the victim’s perimeter directly, attackers increasingly look for connected services that can provide equivalent value with less friction. Access tokens, API permissions, service accounts, and cross-platform integrations can all become shortcuts into data environments that are otherwise well protected.
If that is what happened here, then the incident is not just about one company’s cloud posture. It is about how enterprise data moves across platforms and how much access analytics vendors are allowed to retain. Security reviews often focus on whether a vendor is reputable or whether encryption and logging are in place. Those controls matter, but they do not resolve the deeper design question of how much trust a connected service should hold in the first place.
In the Rockstar case, the leaked data suggests an environment focused on metrics and reporting rather than core game-development assets. That may mean segmentation worked to some degree, or it may simply reflect what data was reachable through the compromised path. Either way, it reinforces a core principle of cloud security: the value of an attacker’s path depends less on brand name than on access scope.
Mitigation Steps for Rockstar Games
Rockstar should treat the incident as a reminder that third-party analytics access deserves the same level of scrutiny as core internal infrastructure. The most immediate priorities should include forensic validation of exactly what data was reachable, what tokens or accounts were abused, how long access persisted, and whether any related environments were exposed beyond the currently known analytics datasets.
The company should also conduct a rigorous review of every connected service that can reach Snowflake, support reporting, telemetry stores, and operational dashboards. Access paths that are broader than necessary should be reduced. Service account permissions should be reevaluated. Token rotation and credential revocation should be aggressive, not merely procedural. Any vendor integration that can reach high-volume internal reporting data should be audited with the assumption that convenience-based access decisions may have become latent security liabilities.
Clearer disclosure would also help. Rockstar does not need to overstate the incident, but a more precise explanation of what categories of data were affected would reduce unnecessary speculation. In high-profile incidents, silence creates its own risk because the public fills the gaps with guesses about player data, unreleased content, and worst-case compromise scenarios. A narrow breach can remain narrow while still being described more clearly.
Recommended Actions for Employees, Partners, and Players
For Rockstar employees and partners, the most practical response is heightened caution around phishing, credential reuse, and requests that reference internal reporting, support systems, or analytics workflows. When attackers obtain administrative or business data, the next move is often to weaponize context rather than rely only on the original leak.
Useful steps include:
- Reset and rotate credentials tied to analytics, reporting, and support environments where appropriate
- Review third-party integrations and remove any access that is broader than operationally necessary
- Be cautious of emails or messages that reference internal report names, support workflows, or urgent access requests
- Monitor for suspicious activity tied to Zendesk, Snowflake, analytics dashboards, or service accounts
- Escalate unusual vendor-related authentication prompts or permission changes immediately
For players, there is currently no strong public indication that consumer account data was exposed in this incident. Even so, users should remain cautious about fake Rockstar security notices, refund messages, account warnings, or GTA-themed phishing attempts that try to exploit headlines around the breach. Criminals regularly use public breach news as a lure even when the breach itself did not expose the victim’s credentials.
Useful steps for players include:
- Ignore unsolicited messages claiming your Rockstar account was affected unless they can be verified through official channels
- Do not click links in emails or DMs that promise breach details, account recovery, or leaked game content
- Use strong unique passwords and enable added account protections where available
- If you suspect a device has been exposed to malicious files or links, scan it with a trusted security tool such as Malwarebytes
The Rockstar Games data breach is not the kind of incident that appears likely to derail Grand Theft Auto VI or directly endanger players based on what is publicly known so far. But it is still a real breach, a real exposure of internal data, and a real example of how cloud-linked third-party relationships can become entry points into major companies. Rockstar’s decision to frame the incident as limited and non-material may be accurate in the narrowest sense, yet the broader lesson remains significant. Security failures no longer need to look dramatic to matter. In a heavily integrated enterprise environment, even a breach that seems boring on the surface can reveal exactly how much risk has been outsourced to the connections companies trust every day.
For continued coverage of major data breaches and wider cybersecurity threats, this incident is another reminder that the next important compromise may not come through a front door at all. It may come through the vendor dashboard, the analytics token, or the trusted integration nobody expected to become the story.
- GitHub Data Breach Confirmed After Poisoned VS Code Extension Exfiltrates Internal Repositories
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Rheem Manufacturing Data Breach Claim Follows Reported INC Ransom Listing
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













