The Vercel data breach traces back to a Context.ai employee compromise that gave attackers a route through a Vercel employee’s Google Workspace account and into parts of Vercel’s internal environment. Vercel and Context.ai have both now confirmed that basic chain. Once the route in is laid out plainly, the breach looks much less like some difficult mystery inside Vercel and much more like a weak employee-side compromise at a smaller AI company that ended up carrying far more trust and access than it ever should have.
Vercel says the incident began with a compromise of Context.ai, a third-party AI tool used by a Vercel employee. The attacker then used that access to take over the employee’s Vercel Google Workspace account and move into some Vercel environments and environment variables that were not marked sensitive. Context.ai later confirmed that OAuth tokens from its deprecated AI Office Suite were compromised and that one of those tokens was used to access Vercel’s Google Workspace. Context.ai also said the Vercel employee had signed up for the product using a Vercel Google Workspace account, which meant the stolen token carried the scope that corporate account already had.
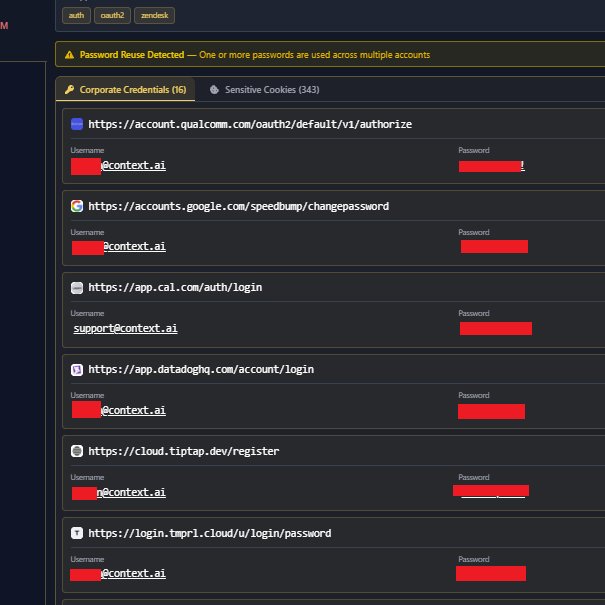
The employee side gets much worse once Hudson Rock’s findings are added. Hudson Rock says the Context.ai side traces back to a February 2026 Lumma infostealer infection on a Context.ai employee machine. Its report says the stolen set included Google Workspace credentials and other corporate access tied to services like Supabase, Datadog, and Authkit, and it points to support@context.ai as a sensitive account inside the haul. The screenshot showing “Password Reuse Detected” and a stack of Context.ai corporate credentials fits that picture cleanly. Vercel did not get dragged into this because of some abstract cloud gremlin. It got dragged into it because one employee-side compromise at Context.ai was allowed to sit close enough to real corporate access to matter.
The screenshots circulating around that machine make the employee trail even uglier. International Cyber Digest published a post tying the compromise to porn and anime site logins, a “lecoonjames” handle, and the same profile image staying in place even after the username was changed. That is the material people are now using when they describe the employee as a racist gooner. Those details do not come from Vercel’s own bulletin, but they are part of the public record around the compromise and they change the way the whole chain reads. The machine behind this breach path does not look like a careful corporate endpoint sitting inside a disciplined environment. It looks filthy, reckless, and unserious.
This means the breach path was not limited to one embarrassing account. Hudson Rock says the stolen records included support@context.ai along with the employee-side credentials and other linked corporate access. Once an infected machine is carrying Google Workspace access, a support account, and multiple other business logins inside the same stolen set, the problem stops being one employee making an ass of himself. A Context.ai machine should never have held this much meaningful access in a state loose enough for an infostealer to pull it all into one place.
Vercel’s own later guidance shows how much weight that compromise ended up carrying. The company told customers to review and rotate environment variables that were not marked sensitive, review logs, inspect deployments, and rotate Deployment Protection tokens. It also changed product defaults so new environment variables are now sensitive by default and improved team-wide secret management. Companies do not make that kind of change after a breach because everything was already fine. They make it because the incident exposed a path that was too weak for the level of trust and access sitting on top of it.
Context.ai’s explanation does not rescue the picture either. It says the affected product was an old consumer-focused Office Suite rather than its current enterprise platform and that the relevant environment and OAuth app were shut down. That does not change what happened. A weaker AI product sat close enough to a Vercel employee’s real corporate identity that a compromise on the smaller side helped turn into a breach on the larger side. Calling the product deprecated does not make that chain look cleaner.
The breach also says a lot about the current AI-company environment. Context.ai is exactly the kind of smaller AI business that gets built fast, wired into real work quickly, and trusted long before it has earned that trust. A company like Vercel should not have been one compromised employee at one weak AI vendor away from this kind of incident. Yet that is where the route leads. Context.ai, a compromised Office Suite token, a Lumma infection, a password reuse warning, support@context.ai in the stolen set, and an employee-side trail dirty enough to strip the polish off everyone involved.
Anyone trying to understand why Vercel customers ended up rotating secrets needs to start there. The path into the breach runs through Context.ai, through a compromised employee machine, through stolen corporate access, and through an identity chain weak enough to let all of it travel. That is not what serious infrastructure is supposed to look like, and it is not what serious companies are supposed to trust.
- GitHub Data Breach Confirmed After Poisoned VS Code Extension Exfiltrates Internal Repositories
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Rheem Manufacturing Data Breach Claim Follows Reported INC Ransom Listing
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













