Vercel has confirmed that attackers got unauthorized access to certain internal systems after a third-party AI tool’s Google Workspace OAuth app was compromised. Even with the company saying only a limited subset of customers was affected and services remained operational, this still left customers reviewing activity logs, inspecting deployments, rotating Deployment Protection tokens, and treating non-sensitive environment variables containing secrets as potentially exposed. For anyone running production apps on Vercel, those are not casual recommendations. They are the kind of steps people take after a platform underneath them has already been breached.
The first hours of the Vercel breach were messy in a way that did the company no favors. Vercel published its bulletin, but users were also trying to understand what happened through X posts, screenshots, secondhand summaries, and chatter about stolen data while the story was still moving. Some users were plainly irritated that something this serious still felt unclear so early on, especially once it became obvious that the public discussion was running ahead of whatever certainty the company had managed to communicate. Infrastructure companies do not only sell uptime. They sell trust, and trust gets weaker when customers feel like they are piecing together a breach from fragments.
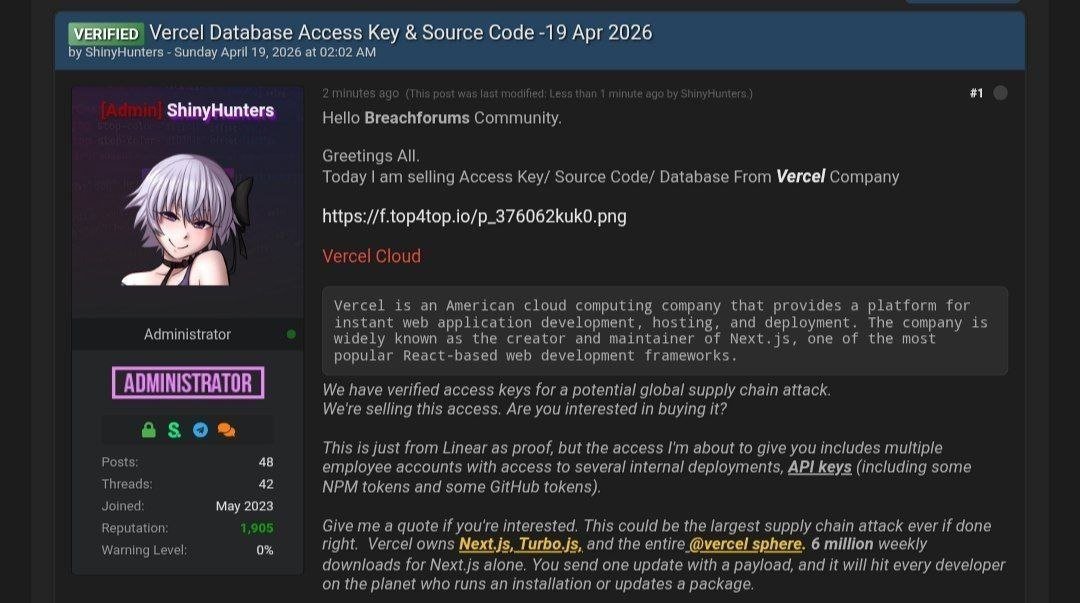
The noise got louder once claims started circulating under the ShinyHunters name, along with screenshots and dramatic descriptions of what was supposedly up for sale. Vercel did not name ShinyHunters in its own bulletin, and the attribution around those posts has already been challenged, so that part of the story is still muddy. The cleaner line is the one Vercel itself has already forced customers to take seriously: internal systems were reached, the incident was real, some customers were affected, and the response included rotating secrets and rechecking deployments. That is already bad enough without pretending every louder claim around the incident has been settled.
One of the more useful updates came from Guillermo Rauch himself. According to Rauch, a Vercel employee was compromised through the breach of Context.ai, an AI platform that employee was using, and the attacker then escalated from that compromised Google Workspace account into Vercel environments. He also said Vercel stores customer environment variables fully encrypted at rest by default, but that the company has a non-sensitive designation for some variables, and those became part of the problem once the attacker got far enough to enumerate them. That explanation matters because it turns the incident from vague security language into something much more concrete. An employee account was compromised. The compromise moved deeper. Customers were left responding to the fallout.
The entry point says a lot about the way modern companies are choosing to build risk into their own environment. This was not some movie-style exploit dropped out of nowhere. It was one more AI tool, one more OAuth grant, one more connection that looked harmless until it opened the wrong door. Companies keep wiring AI tools into inboxes, repos, docs, dashboards, workspaces, support systems, and internal workflows as if every new connection is just another convenience feature. This is what that convenience looks like when it breaks.
Vercel is also not some small company fumbling through a hard lesson for the first time. This is a heavily funded infrastructure company that has spent years selling speed, scale, and security with the confidence of a platform that wants to be treated like serious modern infrastructure. It has the money, the product aura, the investor bench, and the marketing language to make people believe their projects are sitting in safe hands. That is part of what makes the breach so damaging. A company that wants to be seen as secure infrastructure does not come out looking stronger after a third-party AI OAuth compromise reaches internal systems and forces customers to rotate secrets. It comes out looking much thinner than the branding around it suggested.
The security story around Vercel also starts looking weaker the more closely you inspect it. The company sells bot management, firewalling, DDoS mitigation, AI crawler controls, and a public bot directory through bots.fyi, but after actually looking through that directory it is hard to understand how anyone ships it as a finished security product and expects people to pay for the surrounding story without asking harder questions. The public directory only shows 196 results, the entries are thin, and the overall product feels much barer than the language around it suggests. In contrast, even our very basic free Bot Blocker project tracks more than 500 bot listings and gives substantially more useful detail. That is not the breach, and it did not cause the breach, but it does add to the same pattern. Vercel keeps selling depth and seriousness, and the details behind the sales pitch start looking a lot lighter once you spend real time with them.

The company also carried enough baggage before the breach that many people were never going to feel especially sympathetic once something went wrong. Guillermo Rauch publicly posted a smiling photo with Benjamin Netanyahu and wrote warmly about their discussion on AI, literacy, safety, and progress. Nobody has to declare loyalty to any state to understand why that left a sour taste for a lot of people. Gaza is one of the most bitter and radioactive subjects on the internet, and posting that kind of cheerful photo-op as the CEO of a developer infrastructure company was wild and unprofessional. It looked bad then, and it still hangs over the company now.
The investor list does not help either. Brendan Eich is on it, and his anti-gay-marriage record is public, ugly, and old enough that nobody needs it explained twice. Plenty of people do not like homophobic public figures, do not trust them, and do not look at companies attached to them charitably. Seeing Eich on Vercel’s investor page does not explain the breach, but it does make the company much easier to distrust once the breach lands on top of everything else.
Rauch also said Vercel analyzed its supply chain and believes Next.js, Turbopack, and the company’s open-source projects remain safe. Customers needed to hear that, and it is good that Vercel addressed it. It still leaves the same basic facts sitting in plain view. Internal systems were reached. A real employee account was compromised. A third-party AI OAuth path was enough to help attackers get deeper into the environment. Customers still had to react. Supply chain reassurance matters, but it does not make the incident clean.
The customers are the ones who matter most here. They are the ones checking logs, reviewing deployments, regenerating tokens, rotating environment variables, and wondering how much confidence they still have in a platform that just admitted attackers reached internal systems through a third-party AI OAuth compromise. Executives and investors will still have their statements, their branding, and their capital. Customers are the ones left doing the work afterward.
That is why the Vercel breach is more than just another bad headline for a well-funded tech company with too much swagger and too much baggage. It forces a much more practical question onto the people using the platform. If a company this polished, this confident, and this heavily backed can end up here, how much trust is still left. For teams already weighing Cloudflare Pages, Netlify, Render, Railway, or a self-hosted path, the answer may be getting a lot easier to reach.
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













