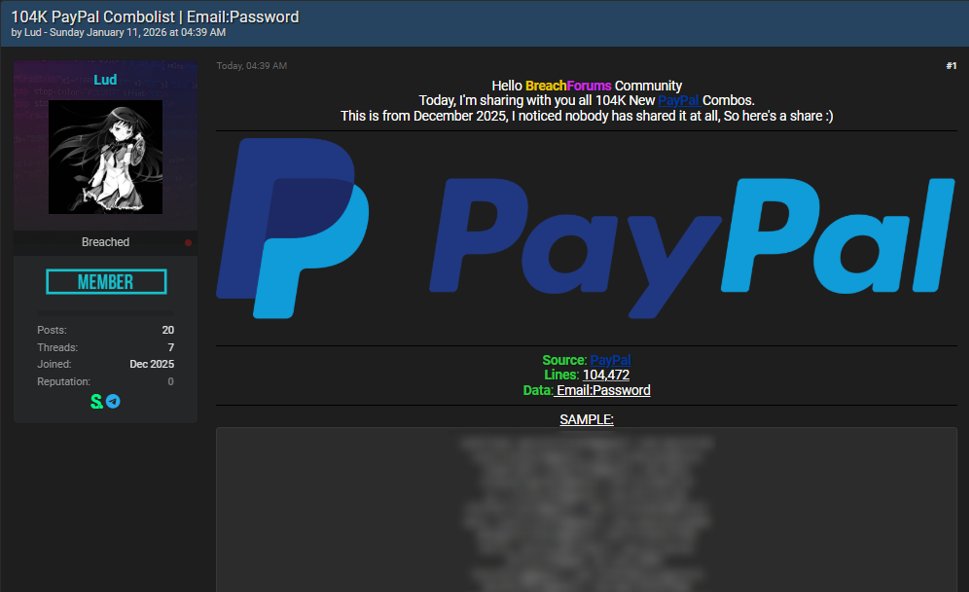
The PayPal credential leak refers to an alleged exposure of account login credentials associated with PayPal users, following the appearance of a large email and password dataset advertised on underground forums. The dataset was shared on January 11, 2026, by a threat actor using the alias “Lud,” who claimed to be releasing a newly compiled PayPal-related combolist. This incident is being monitored alongside other significant data breaches due to the financial risk posed by credential reuse and the widespread reliance on PayPal as a global payment platform.
PayPal operates as one of the world’s largest digital payment processors, supporting consumer payments, business transactions, subscriptions, and peer-to-peer transfers across hundreds of markets. Because PayPal accounts are frequently linked to bank accounts, credit cards, and identity verification data, exposed credentials present a high risk of financial abuse even in the absence of direct system compromise.
According to the threat actor’s post, the dataset contains 104,472 lines formatted as email and password pairs. The data is described as a combolist, a term commonly used to describe aggregated credentials collected from multiple unrelated sources rather than a single breach event. At the time of writing, PayPal has not confirmed any unauthorized access to its internal systems, and no regulatory disclosures or breach notifications have been issued. The exposure therefore represents a credential leak scenario rather than a confirmed PayPal system breach.
Background on PayPal
PayPal is a global financial technology company providing online payment services for individuals, merchants, and enterprises. Its platform supports online purchases, invoicing, subscriptions, international transfers, and integration with countless third-party services. PayPal accounts often serve as a central financial hub for users, storing transaction histories, linked funding sources, and personal identity details required for regulatory compliance.
To support these services, PayPal relies on robust authentication systems, fraud detection mechanisms, and account recovery workflows. While the company invests heavily in security controls, the safety of individual accounts also depends on user password hygiene and resistance to credential reuse across multiple platforms.
Because PayPal credentials can unlock direct access to funds, they are frequently targeted by cybercriminals using automated account takeover techniques. This makes PayPal-related credential leaks particularly attractive within underground markets.
Nature of the PayPal Credential Leak
The PayPal credential leak centers on the distribution of a combolist rather than evidence of intrusion into PayPal infrastructure. Combolists are typically assembled by aggregating credentials harvested from past breaches of unrelated websites, malware infections, phishing campaigns, and credential stuffing tools.
The threat actor claims the dataset was compiled in December 2025 and includes credentials believed to be valid for PayPal accounts due to password reuse. The post does not include claims of database access, internal PayPal fields, transaction records, or proprietary system information. Instead, the dataset is limited to login pairs intended for testing against PayPal’s authentication systems.
This distinction is critical. While combolists do not indicate that PayPal systems were breached, they still pose serious risk to users whose credentials remain unchanged across services.
Scope and Composition of the Exposed Data
Based on the information provided by the threat actor, the exposed dataset consists of:
- Email addresses associated with PayPal accounts
- Corresponding plaintext or previously cracked passwords
- Credential pairs formatted for automated testing tools
The dataset does not appear to include PayPal-specific metadata such as account balances, transaction histories, government identification documents, or internal account identifiers. However, possession of valid login credentials alone can be sufficient to compromise accounts if additional security controls are not enabled.
Even a dataset of this size can have outsized impact, as automated tools allow attackers to test thousands of credentials in a short period of time, targeting accounts with weak security configurations.
Risks to PayPal Users
The primary risk associated with the PayPal credential leak is account takeover resulting from credential reuse. Users who have reused passwords across multiple platforms are particularly vulnerable.
Potential risks include:
- Unauthorized access to PayPal accounts
- Fraudulent transactions or fund transfers
- Abuse of linked bank accounts or credit cards
- Changes to account recovery information
- Use of compromised accounts for further fraud or laundering
Once an account is compromised, attackers may attempt to lock out the legitimate owner by changing passwords, enabling new recovery options, or adding additional funding sources. In some cases, compromised PayPal accounts are resold or used to facilitate scams targeting other users.
Threat Actor Behavior and Monetization Patterns
Threat actors distributing combolists typically aim to enable credential stuffing attacks rather than extortion. These datasets are often shared freely or sold at low cost to increase their spread and utility.
The actor known as “Lud” does not appear to claim exclusive access or to demand payment from PayPal. Instead, the dataset is positioned as a shared resource within underground communities. This behavior aligns with common patterns seen in credential trading ecosystems, where reputation is built through distribution rather than direct monetization.
Because combolists can remain effective for extended periods, especially when users fail to change passwords, the long-term risk associated with this leak should not be underestimated.
Possible Sources of the Credentials
There is no indication that the credentials originated from PayPal systems. Instead, likely sources include:
- Previous data breaches at unrelated websites
- Phishing campaigns impersonating trusted services
- Malware infections harvesting saved browser credentials
- Password reuse across compromised platforms
When users reuse the same email and password combination across multiple services, a breach at one platform can cascade into account compromises elsewhere. Financial platforms are frequent downstream targets of this behavior.
Regulatory and Legal Considerations
Because the PayPal credential leak does not involve confirmed exposure of PayPal-controlled data, it does not currently trigger the same regulatory obligations as a verified breach of internal systems. However, PayPal remains obligated to monitor abuse, protect users from fraudulent access, and respond to account compromise incidents.
Financial regulators increasingly expect platforms to implement strong safeguards against credential stuffing, including rate limiting, anomaly detection, and mandatory multi-factor authentication. Widespread account takeover incidents can still attract regulatory scrutiny even without a traditional breach.
Mitigation Steps for PayPal
Platforms targeted by credential stuffing campaigns typically respond through layered defenses. Appropriate mitigation measures include:
- Monitoring for abnormal login patterns and automation
- Forcing password resets on suspected compromised accounts
- Enforcing multi-factor authentication for high-risk logins
- Rate limiting authentication attempts
- Educating users about password reuse risks
These controls are designed to limit the effectiveness of combolists and reduce the window of opportunity for attackers.
Recommended Actions for Affected Individuals
Users who have a PayPal account should take proactive steps to reduce risk associated with credential leaks.
Recommended actions include:
- Change PayPal passwords immediately if reused elsewhere
- Enable multi-factor authentication on PayPal accounts
- Review recent account activity for unauthorized transactions
- Remove unused linked payment methods
- Scan devices for malware using a trusted tool such as Malwarebytes
Users should also remain cautious of phishing emails or messages claiming account issues, as attackers often exploit credential leaks with follow-up social engineering.
Broader Implications for Online Financial Security
The PayPal credential leak highlights the persistent risk posed by password reuse across the internet. Even when major platforms maintain strong internal security, user behavior and third-party breaches continue to undermine account safety.
As financial services increasingly operate online, credential-based attacks remain one of the most effective methods for cybercriminals. This incident reinforces the importance of unique passwords, multi-factor authentication, and continuous monitoring by both platforms and users.
- ServiceNow Data Breach Exposes Customer Tenants to Unrestricted API Access
- GitHub Data Breach Confirmed After Poisoned VS Code Extension Exfiltrates Internal Repositories
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













