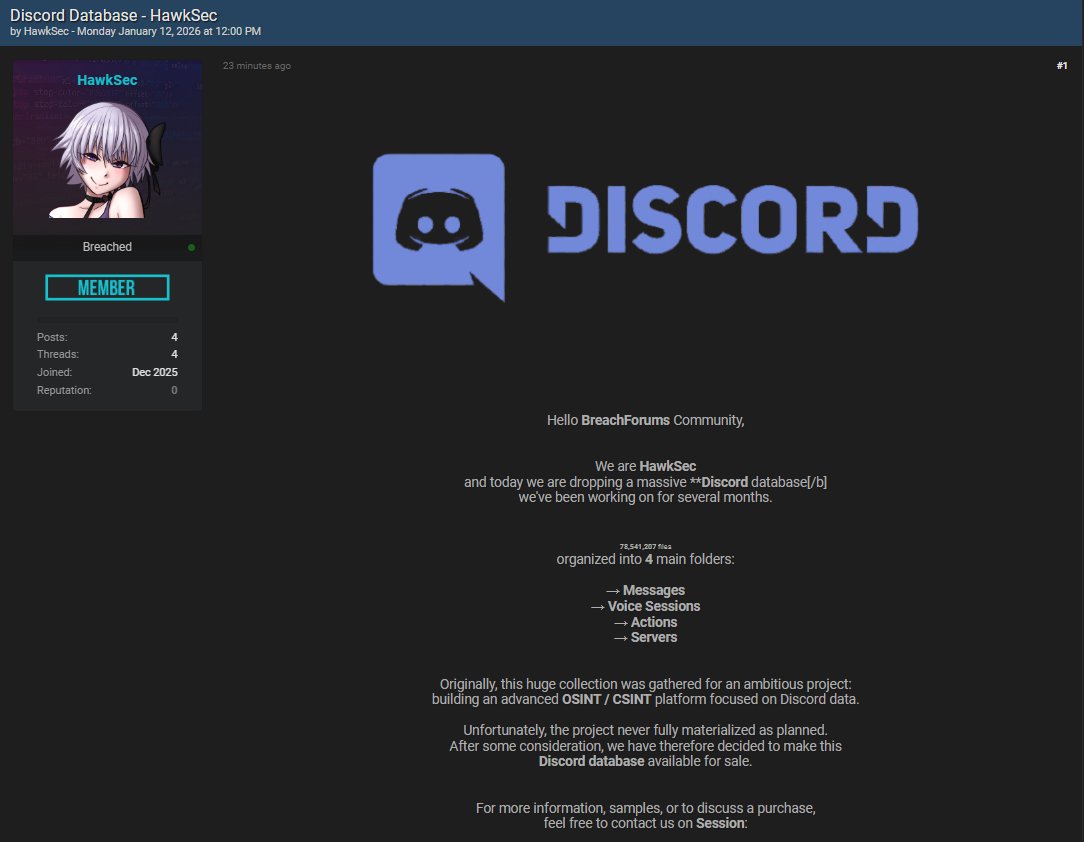
The Discord data leak claim refers to an alleged large scale exposure of Discord related data following assertions made by a threat actor using the alias HawkSec. The claim surfaced on January 12, 2026, when the actor advertised a dataset attributed to Discord activity and offered it for sale. The incident is being monitored alongside other significant data breaches due to the scale of the dataset and Discord’s role as a major global social networking platform.
According to the claim, the dataset contains approximately 78,541,207 files organized into multiple structured directories, including messages, voice sessions, actions, and server related data. The threat actor states that the data was collected over several months and was originally intended for use in an OSINT and CSINT research project that was later abandoned. The dataset is now allegedly being sold to interested buyers. At the time of writing, Discord has not publicly confirmed any security incident associated with this claim, and no regulatory disclosures or official breach notifications have been identified.
The Discord data leak claim is notable not because of confirmed intrusion into Discord infrastructure, but because it highlights the growing risks associated with large scale data aggregation, scraping, and long term collection of user generated content from social platforms. Even without evidence of direct system compromise, datasets of this size can present meaningful privacy, security, and trust concerns.
Background on Discord
Discord is a global social communication platform that supports text messaging, voice communication, video calls, and community based servers. The service is widely used by individuals, gaming communities, educational groups, businesses, and public organizations. Discord accounts are tied to unique user identifiers and often linked to email addresses, usernames, server memberships, and interaction histories.
To support real time communication at scale, Discord processes and stores significant volumes of user generated content. This includes messages, voice metadata, server configurations, moderation logs, and interaction records. While Discord enforces access controls and privacy settings, much of the platform’s value lies in community interaction, which can create opportunities for large scale data collection through legitimate or borderline methods.
Social networking platforms such as Discord represent high value targets for cybercriminals due to the trust relationships between users, the persistence of conversations, and the ability to leverage compromised or exposed data for scams, impersonation, or secondary attacks.
Details of the Discord Data Leak Claim
The Discord data leak claim originates from a forum post attributed to HawkSec, who claims to be in possession of a large Discord related dataset. The actor describes the dataset as consisting of more than 78 million individual files, grouped into four primary categories:
- Messages
- Voice sessions
- Actions
- Servers
The threat actor states that the data was collected over several months and was intended for an intelligence gathering project focused on Discord ecosystems. The project was allegedly abandoned, after which the dataset was offered for sale. The actor has provided a high level description of the data structure but has not publicly released comprehensive samples sufficient to independently verify the contents.
Crucially, the claim does not assert that Discord internal systems were breached or that administrative access was obtained. The framing of the dataset as an OSINT or CSINT collection suggests that the data may have been aggregated through public servers, automated collection tools, bots, compromised accounts, or other indirect means rather than direct unauthorized access to Discord backend infrastructure.
Scope and Composition of the Allegedly Exposed Data
Based on the threat actor’s description, the Discord data leak appears to consist of structured records related to Discord activity rather than traditional account databases. The data may include:
- Text message content from servers or channels
- Metadata related to voice sessions
- User interaction logs or action records
- Server identifiers, names, or configuration details
There is no indication that the dataset includes Discord passwords, payment information, or internal authentication secrets. However, large scale aggregation of messages and activity data can still pose privacy risks, particularly when conversations were assumed by participants to be transient or limited to specific communities.
Even when data is sourced from publicly accessible or semi public environments, aggregation at scale changes the risk profile. What may be low risk in isolation can become highly sensitive when consolidated into searchable datasets.
Risks to Users and Communities
The Discord data leak claim presents several potential risks to users and server communities, even in the absence of confirmed system compromise.
Potential risks include:
- Targeted phishing or impersonation based on message content
- Exposure of private conversations assumed to be ephemeral
- Mapping of social networks and community relationships
- Harassment or doxxing using contextual message data
- Reputation damage for individuals or organizations discussed in messages
Voice session metadata may also reveal patterns of activity, participation, or coordination that could be misused. In some contexts, such information can be leveraged for surveillance, profiling, or intimidation.
Communities that discuss sensitive topics or operate under assumptions of limited visibility may face elevated risk if their communications are aggregated and redistributed.
Risks to Discord and Platform Trust
While the Discord data leak claim does not establish a confirmed breach of Discord infrastructure, it nonetheless raises broader concerns about platform trust and data stewardship. Users often assume that platform controls, moderation, and privacy features limit the persistence and reuse of their communications.
Large scale data aggregation undermines these assumptions and can erode trust even when the platform itself has not failed technically. For Discord, repeated association with large datasets attributed to its ecosystem may prompt questions from users, regulators, and enterprise partners regarding data protection practices and abuse prevention.
Social platforms face ongoing challenges balancing openness with abuse prevention. Automated collection, scraping, and misuse of platform features are persistent risks that require continuous mitigation.
Threat Actor Behavior and Monetization Patterns
HawkSec’s framing of the dataset as an abandoned research project aligns with a broader trend in underground communities where collected data is repurposed for sale when original objectives are no longer pursued. This differs from traditional ransomware or extortion driven incidents and may reflect opportunistic monetization rather than targeted compromise.
Threat actors offering large datasets often emphasize file counts, organization, and scale to attract buyers. The absence of ransom demands or direct pressure on Discord suggests that the actor’s goal is resale rather than coercion.
Such behavior is consistent with actors who specialize in data aggregation, scraping, or secondary distribution rather than direct intrusion operations.
Possible Data Collection Methods
Discord has not released technical details addressing the claim. Based on the information provided, possible data collection methods may include:
- Automated scraping of public Discord servers
- Use of bots to log messages and activity
- Collection from compromised user accounts
- Exploitation of misconfigured integrations or permissions
These scenarios are presented for analytical context only and should not be interpreted as confirmed causes. Each represents a known risk vector within social networking environments.
Regulatory and Legal Considerations
Depending on the nature of the data involved, large scale aggregation of Discord communications may trigger privacy obligations in certain jurisdictions, particularly if personal data of identifiable individuals is included. Even publicly accessible content can be subject to regulatory scrutiny when collected and redistributed at scale.
If the dataset includes users from regions governed by data protection frameworks such as GDPR, affected parties may have rights related to notice, deletion, or redress. However, enforcement in cases involving third party aggregation remains complex.
Platforms may also face pressure to demonstrate reasonable measures to prevent abuse of their services for mass data collection.
Mitigation Steps for Discord
Organizations operating large social platforms can reduce exposure to similar incidents through layered controls. Potential mitigation steps include:
- Strengthening rate limiting and bot detection mechanisms
- Auditing public API usage and access patterns
- Enhancing monitoring for large scale data collection behavior
- Reviewing permissions and integration policies
- Improving user education around server privacy settings
Continuous assessment of abuse vectors is essential in environments where user generated content is central to platform value.
Recommended Actions for Affected Individuals
While no confirmed breach of Discord systems has been established, users should remain cautious in light of large dataset claims.
Recommended precautions include:
- Assuming that messages posted in public servers may be archived
- Being cautious of unsolicited messages referencing past conversations
- Reviewing server privacy and participation choices
- Using unique credentials for Discord accounts
- Scanning personal devices for malware using a trusted tool such as Malwarebytes
Users should rely on official Discord communications for updates and avoid engaging with individuals offering access to leaked datasets.
The Discord data leak claim illustrates how large scale data aggregation can present security and privacy challenges even without confirmed system compromise. As social platforms continue to grow, the boundary between public interaction and private expectation becomes increasingly blurred.
For continued coverage of emerging data breaches and ongoing developments across the cybersecurity landscape, further analysis will be published as verifiable information becomes available.
- ServiceNow Data Breach Exposes Customer Tenants to Unrestricted API Access
- GitHub Data Breach Confirmed After Poisoned VS Code Extension Exfiltrates Internal Repositories
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













