Malware Defender 2015 (Malware Defender 2015 virus, MalwareDefender2015) is a malicious and fake Microsoft Windows security program that is known to manufacture non-existent computer security threats in order to scare unsuspecting victims into purchasing fraudulent software.
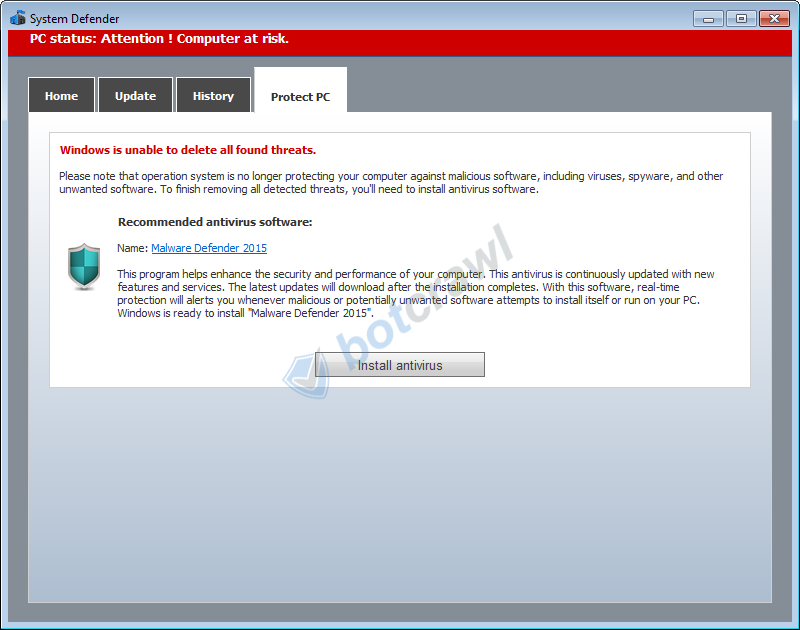
Malware Defender 2015 malware is distributed through various means. It can be contracted through advertisements and downloadable content, but is also promoted via other malicious and fake Windows security programs, including System Defender.
When a computer becomes infected with the Malware Defender 2015 virus, the malicious program will begin to perform a bogus computer scan that will result in numerous non-existent threats. This is a scare tactic used by Malware Defender 2015 malware to “scare” computer users into activating and purchasing the fraudulent product. This is why this type of software is also known as scareware.
Furthermore, the Malware Defender 2015 virus may be contracted alongside other unwanted programs, additional malware, and other malicious threats that can cause different issues and will need to be removed to stop all unwanted activities.
How to remove Malware Defender 2015
Step 1: Scan your computer for Malware Defender 2015 malware
1. We highly recommend that you write down the toll free number below in case you run into any issues or problems while removing Malware Defender 2015 and other malicious threats. Our techs will kindly assist you with any problems.
if you need help give us a call
2. Install the free or full version of Malwarebytes Anti-Malware. The full version enables real-time protection to block malware and unwanted programs from infecting your computer, while the free version is just a free scan and removal tool.
3. Run Malwarebytes Anti-Malware after install. Malwarebytes may automatically begin to update and scan your computer at this point.

4. Click the large Scan Now button or visit the “Scan” tab to manually perform a scan once the Anti-Malware program has opened. Before the scan is started Malwarebytes may ask to update the software, make sure to do so if prompted to.
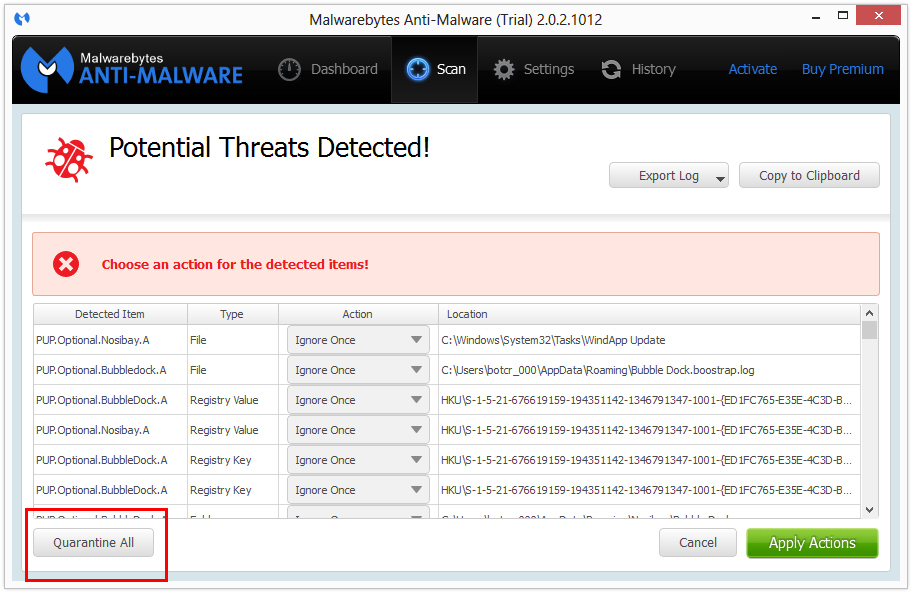
5. When the malware scan is complete, click the Quarantine All button to isolate and remove the detected files. You may be asked to reboot your computer after removal to completely remove detected files.
6. You can additionally chose to visit the History tab and click Delete All to remove these files from the Quarantine log, although these files no longer provide a threat.
Step 2: Cleanup and repair settings
CCleaner can be used to automatically repair internet browser settings that have been changed during this infection. It can also fix system startup up settings, Windows Registry, and help uninstall unwanted software.
1. Install the free or full version of CCleaner by Piriform.

2. Once installed, open the program and navigate to Cleaner > Windows/Applications and click the Analyze button. Afterwards, click the Run Cleaner button on the bottom right of the program interface.

3. Next, navigate to Tools > Startup and search through each tab starting from windows, internet explorer, etc., all the way to Content Menu, for additional suspicious entries and click Disable and Delete once anything is found.
Helpful links
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.