Reports this week said unauthorized users were accessing Claude Mythos from launch day through a third-party vendor environment rather than Anthropic’s core systems. Anthropic said it was investigating and had not found evidence that its own systems were affected. That still leaves a serious access failure around a model the company had already decided was too sensitive for a normal release.
Mythos was not launched like an ordinary model update. Anthropic rolled it out under Project Glasswing as a tightly controlled preview for selected companies and other organizations tied to critical software infrastructure. The company said Mythos could identify and exploit zero-day vulnerabilities across every major operating system and major web browser when directed to do so. Mozilla later said Firefox 150 included fixes for 271 vulnerabilities identified during early work with Mythos. Restricted access was not some marketing flourish here. It was part of the product.
The reported path into Mythos did not sound exotic. Outside reporting said the group got there through a contractor-linked environment, using information exposed in the Mercor breach, a worker’s valid credentials, and other online sleuthing. That points to a vendor and identity problem around a high-risk system, not some breakthrough attack against the model itself. That is bad enough on its own.
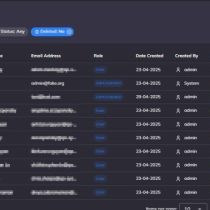
The newer screenshots pushed the situation further. Posts circulating under the ShinyHunters name claimed access to internal systems linked to Mythos and backed that up with images that look like more than a simple chat interface. One appears to show a user management panel with usernames, display names, email addresses, roles, account status, and creation dates. Another looks like a system overview screen with uptime, blocked threats, recent activity, and security alerts. Another looks like a model analytics page showing request volume, latency, token counts, usage, and cost. A fourth image looks like a broader reporting or operations dashboard with charts, department metrics, and internal targets.
Those images need to be treated carefully. They look specific, but they are still unverified. A convincing dashboard is not proof on its own. It can be real. It can also be staged, borrowed, or rebuilt from something unrelated. The cleaner way to read this is to keep the two layers separate. One is the reported unauthorized use of Mythos through a vendor environment. The other is the online claim that people also reached internal systems around it. The first has outside reporting and an Anthropic response behind it. The second does not.
That does not make the screenshot claims harmless. If they are real, the problem broadens quickly. Then the issue is no longer only that outsiders reached Mythos through a contractor-linked path. Then it becomes a question of whether user administration, experiments, model telemetry, and cost analytics were visible too. If the screenshots are fake, the launch-day Mythos access report is still there, and it still raises hard questions about how a restricted cyber model was being handled.
Anthropic spent the Mythos rollout telling the public this was the careful version of an AI release. That is what makes the access report land so badly. A model held back because of what it could do was reportedly in outside hands from day one anyway. The screenshots may end up real or they may end up being noise layered on top of the main incident. Either way, the central problem does not go away. Claude Mythos was supposed to be locked down from the start. Reports say unauthorized users had it anyway.
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- Manus AI Review: The Worst AI Agent I Have Ever Used
- How Claude Deleted the PocketOS Database in 9 Seconds
- Google Commits Up to $40 Billion to Anthropic While It Still Tries to Sell Gemini
- Claude Code Backlash Shows Why AI’s Gatekeeper Era Is Dying
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.