The Starbucks leak uncovered in November 2025 has revealed exposed corporate emails circulating through dark web credential databases. Cyber intelligence analysts identified a series of Starbucks employee accounts included in massive data dumps compiled from unrelated third-party breaches.
While there is no evidence that Starbucks systems were directly breached, the incident highlights how leaked Starbucks credentials can still pose serious risks for global corporations. These leaked accounts provide attackers with potential entry points for phishing, impersonation, and credential stuffing attacks that could eventually target Starbucks networks, partners, and employees.
How the Starbucks Leak Was Discovered
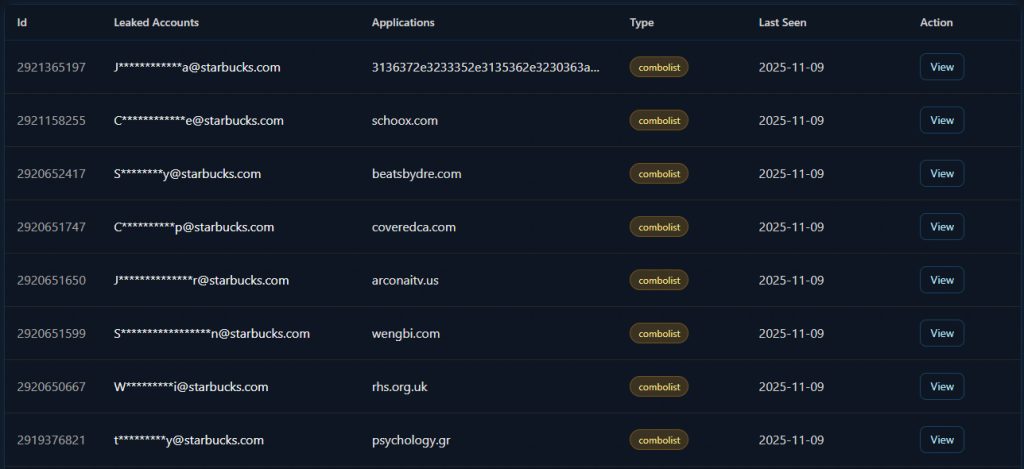
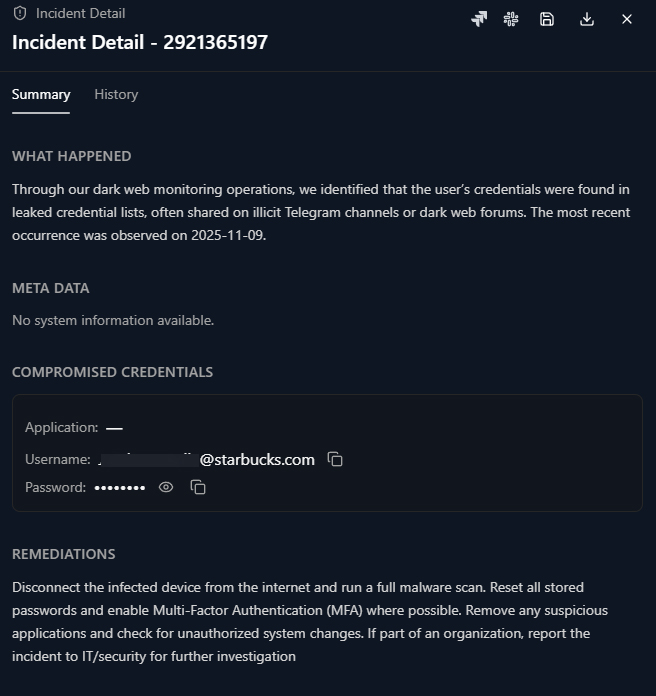
Cyber threat analysts using the WhiteIntel dark web monitoring platform discovered the Starbucks leak on November 9, 2025. During a standard monitoring cycle, the system flagged multiple new entries tied to the starbucks.com domain across various dark web combolists.
A combolist is a large compiled database that merges credentials from multiple breaches into a single archive. These lists are commonly distributed among hackers and cybercriminal communities for credential stuffing attacks. In this case, Starbucks corporate email accounts appeared within combolists sourced from several external sites, showing that Starbucks employees had used their company emails to register on third-party platforms that were later compromised.
Sample Entries Linked to Starbucks Credentials
Researchers identified several Starbucks corporate emails within the leaked datasets. Each entry included an employee’s company address paired with a password hash or partial credential string. All were last observed active in the WhiteIntel database on November 9, 2025.
A sample of the exposed Starbucks credentials includes:
- J************a@starbucks.com – linked to bamboozled.net
- C************e@starbucks.com – linked to schoox.com
- S********y@starbucks.com – linked to beatsbydre.com
- C**********p@starbucks.com – linked to coveredca.com
- J************r@starbucks.com – linked to arconaitv.us
- S*****************n@starbucks.com – linked to wengbi.com
- W*********i@starbucks.com – linked to rhs.org.uk
- T*********y@starbucks.com – linked to psychology.gr
Each record was marked as part of a combolist aggregation rather than a targeted corporate breach. However, the widespread exposure of Starbucks credentials raises serious concerns about password reuse and long-term network safety.
Why the Starbucks Leak Matters
Although the Starbucks leak does not indicate an internal compromise of Starbucks servers, it reveals an underlying security issue that affects nearly every modern enterprise. Employees frequently use their work emails to sign up for non-work services. When these unrelated platforms suffer breaches, the corporate email addresses are leaked alongside personal data.
Attackers then harvest and compile these leaks into searchable databases. Once corporate domains like starbucks.com appear in such archives, criminals can use the data to attempt login attacks, spear-phishing, or identity fraud. Even outdated credentials hold value because they expose employee identities, job roles, and internal communication patterns.
The Role of Credential Reuse
Credential reuse remains one of the most persistent cybersecurity threats. Many employees reuse the same or similar passwords across multiple services. If a Starbucks employee used their company password to register on a consumer site that was later breached, that same password might still unlock internal accounts.
In large organizations like Starbucks, even one reused password can open the door to significant compromise. Cybercriminals use automated tools to test stolen credentials against corporate VPNs, email systems, and cloud services. This tactic, known as credential stuffing, has been responsible for countless security incidents across global enterprises.
Starbucks’ Potential Exposure and Risks
The Starbucks leak may seem minor on the surface, but its implications extend far beyond the initial discovery. Even a handful of exposed corporate accounts can lead to large-scale social engineering campaigns or targeted attacks.
Potential risks include:
- Phishing campaigns: Cybercriminals can craft convincing fake Starbucks communications targeting employees or partners.
- Supply chain exploitation: Vendors and contractors could be deceived by forged messages sent from exposed Starbucks addresses.
- Internal reconnaissance: Exposed naming conventions allow attackers to predict valid email structures for further attacks.
- Reputation damage: Public exposure of Starbucks credentials can erode trust among customers and business partners.
These risks persist even when the affected passwords are changed, because the data itself continues circulating indefinitely on the dark web.
Third-Party Sources Linked to the Starbucks Leak
The domains listed in the WhiteIntel report point to several unrelated websites and applications. One of the more notable ones is schoox.com, a corporate training platform that Starbucks has previously used for employee learning management. While there is no confirmed breach of Schoox at this time, employee registrations on third-party sites often expose corporate credentials when those services experience their own data incidents.
Other connected domains such as beatsbydre.com and coveredca.com likely indicate that Starbucks employees used their work emails for personal registrations, which later became part of unrelated consumer data leaks.
This pattern is consistent with broader industry trends where employee activity outside the organization indirectly contributes to corporate risk. Attackers rarely need to breach a company’s internal systems directly when they can find valid credentials in public or underground datasets.
Impact on the Starbucks Brand
For a company as large and globally recognized as Starbucks, the discovery of exposed corporate credentials poses both security and reputational challenges. Consumers and partners expect major brands to maintain strong cybersecurity standards. Even when the data originates elsewhere, public association with a leak can damage confidence and attract unwanted media attention.
In past incidents, corporations have faced widespread coverage simply because employee emails appeared in leaked data, regardless of whether the organization itself was hacked. The Starbucks leak therefore represents not just a security risk but also a communication and brand management concern.
How Cybercriminals Exploit Leaked Data
When Starbucks credentials appear in dark web repositories, they can be used in multiple ways:
- Credential stuffing: Automated attacks testing usernames and passwords across corporate systems.
- Phishing setup: Impersonation of Starbucks staff to trick partners or customers into sharing sensitive data.
- Social engineering: Fake messages using leaked names and roles to manipulate employees.
- Spam or malware distribution: Using leaked emails for bulk phishing or ransomware delivery campaigns.
Once information like this enters circulation, it can remain accessible for years. Old credentials often resurface in new databases, making continuous monitoring essential.
How Starbucks and Other Companies Can Respond
The most effective defense against incidents like the Starbucks leak is proactive monitoring and credential hygiene enforcement. Starbucks’ internal security teams likely already employ dark web scanning tools and incident response protocols. However, corporate networks can still be indirectly affected if employees ignore password policies or register on insecure platforms.
Recommended actions include:
- Resetting any passwords associated with the affected Starbucks email accounts.
- Conducting a global credential audit to identify reused or weak passwords.
- Mandating multi-factor authentication (MFA) for all company systems.
- Restricting the use of corporate email addresses on third-party services.
- Providing ongoing employee security awareness training.
By implementing these steps, Starbucks and other enterprises can limit the long-term risks of credential leaks and reduce their exposure footprint.
Industry Context and Growing Credential Markets
The Starbucks leak is one of many similar incidents identified in 2025. Analysts have seen a sharp rise in credential-based data circulation, often driven by infostealer malware and large-scale account scraping. Platforms track thousands of new credential appearances every week across all major industries.
These markets thrive because even outdated credentials have resale value. Threat actors use them for identity correlation, spam operations, and phishing. For large corporations, this means continuous exposure to external risks even without internal security failures.
Protecting Starbucks Employees and Systems
Employees should be advised to immediately check whether their credentials appear in known breach databases using trusted services. Passwords that have ever been reused between personal and corporate accounts must be changed.
Additionally, all Starbucks staff should be encouraged to use enterprise password managers and avoid browser password storage. MFA should be mandatory for email, HR, and finance-related logins. These small measures drastically reduce the success rate of credential-based attacks.
Organizations should also scan devices for malware that may harvest stored credentials. Running security software such as Malwarebytes can help detect and remove infostealer threats responsible for many recent leaks.
Why Ongoing Monitoring Is Critical
Dark web exposures like the Starbucks leak often occur months after the original data theft. Because leaked data circulates indefinitely, continuous surveillance is essential. Threat intelligence tools that monitor for domain mentions and credential reappearances allow companies to respond before attackers act.
Starbucks and other corporations benefit from maintaining relationships with cybersecurity vendors who specialize in dark web threat intelligence. Automated alerts ensure rapid detection whenever new credentials tied to a company domain are discovered.
The Bigger Picture
The Starbucks leak demonstrates that the line between personal and corporate cybersecurity continues to blur. Employees routinely blend work and personal activities online, and attackers take advantage of that overlap. The exposure of even a few Starbucks credentials reinforces the need for stricter corporate policies and employee education.
Cyber incidents like this also highlight a growing issue in modern business security: data exposure without direct intrusion. A company does not need to be hacked to become part of a breach cycle. Simply having employee accounts appear in dark web datasets can open the door to future compromise.
Final Notes
The Starbucks leak serves as a clear reminder that cybersecurity begins with human behavior. Even the most advanced systems can be undermined by password reuse, poor digital hygiene, or careless account management.
By reinforcing credential safety, promoting multi-factor authentication, and monitoring the dark web continuously, Starbucks and other major enterprises can reduce exposure from indirect data leaks.
For ongoing coverage of confirmed data breaches and global cybersecurity developments, visit Botcrawl for detailed analysis and verified reports.
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













