The Signal messaging platform has confirmed a targeted phishing campaign that resulted in account takeovers affecting some users, including journalists and government officials. The incident did not involve a data breach of Signal’s encryption or infrastructure. Instead, attackers relied on social engineering techniques to trick victims into handing over sensitive authentication information. The event highlights a recurring reality in cybersecurity: even the strongest encryption cannot protect accounts if attackers successfully manipulate users into giving up their login credentials.
We are aware of recent reports regarding targeted phishing attacks that have resulted in account takeovers of some Signal users, including government officials and journalists. We take this very seriously.
To be clear: Signal’s encryption and infrastructure have not been…
— Signal (@signalapp) March 9, 2026
The incident has drawn significant attention because Signal is widely considered one of the most secure messaging platforms available. The app uses end-to-end encryption based on the Signal Protocol, a system that has been extensively studied by security researchers and adopted by other major messaging services. In this case, however, the attackers did not attempt to break encryption. They focused instead on the human layer of security.
How the Signal Phishing Attack Worked
The signal phishing attack relied on impersonation and deception rather than technical exploits. Attackers reportedly contacted users while pretending to be trusted contacts or official services. In several cases, victims were approached by accounts claiming to be something similar to a “Signal Support Bot” as shown in the image below.
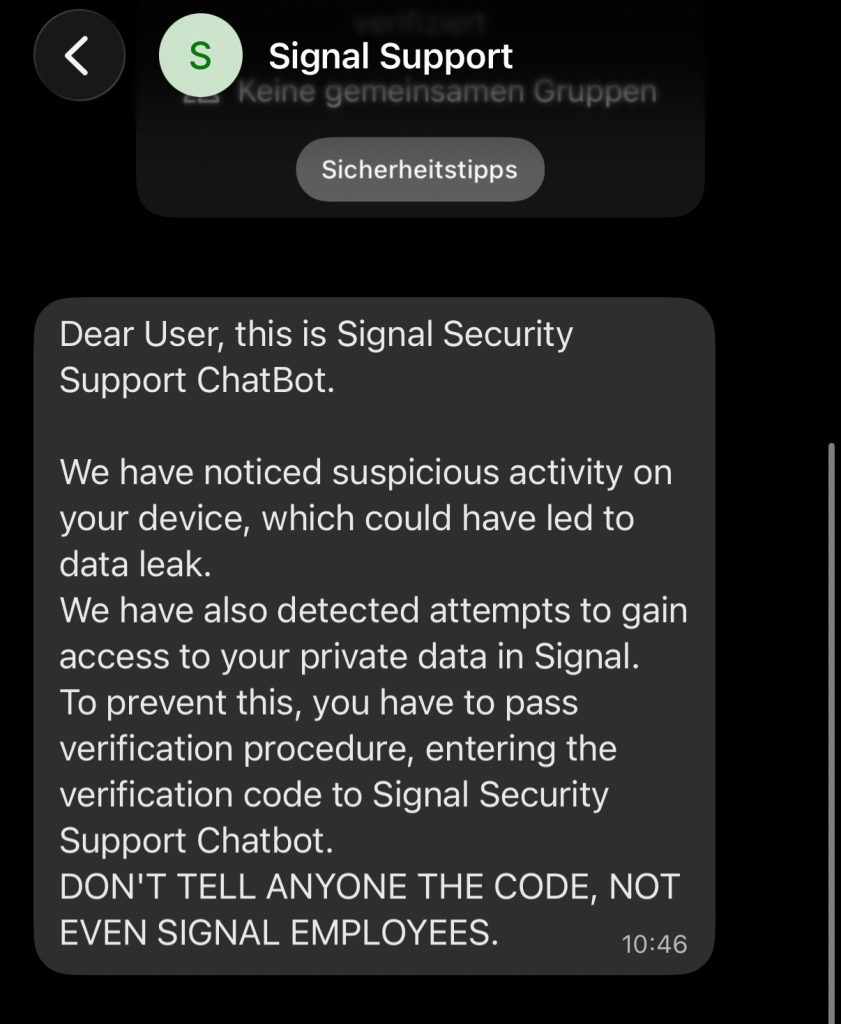
The attackers then attempted to convince victims that there was a problem with their account that required verification. During this process they asked the victim to share their Signal verification code, PIN, or other authentication information.
Once the victim shared the code, the attacker could register the account on a new device. Because Signal accounts are tied to phone numbers, the verification code effectively acts as the key that authorizes a new device to access the account.
With that code in hand, the attacker could take control of the account without ever needing to compromise Signal’s servers or encryption.
Encryption and Infrastructure Remain Intact
Signal emphasized that the phishing campaign did not involve any breach of its encryption systems. The company stated that its infrastructure was not compromised and that the Signal Protocol remains secure.
This distinction is important. End-to-end encryption protects messages while they travel between devices. It ensures that only the sender and intended recipient can read the contents of a conversation.
However, encryption does not prevent attackers from gaining access to an account if the user voluntarily provides login credentials. In phishing attacks, the attacker bypasses the technology by manipulating the victim directly.
This is why security professionals often say that the human element is one of the most difficult aspects of cybersecurity to defend.
Who Was Targeted
Signal confirmed that the phishing campaign targeted specific individuals rather than the general public. Among the victims were journalists and government officials. These types of users are commonly targeted in phishing campaigns because their communications may contain sensitive information or provide access to valuable networks.
Targeted social engineering attacks against high-profile individuals are often more sophisticated than mass phishing campaigns. Attackers may spend time crafting believable messages, impersonating trusted contacts, or studying the victim’s professional environment to make the scam more convincing.
In many cases, attackers attempt to create a sense of urgency by claiming that the victim’s account is at risk or that immediate verification is required.
The Role of Social Engineering
The signal phishing attack illustrates how social engineering continues to be one of the most effective tools used by attackers. Social engineering refers to tactics that manipulate people into revealing information or performing actions that compromise their security.
Rather than exploiting vulnerabilities in software, social engineering attacks exploit trust and human behavior. Phishing emails, fake support messages, impersonation scams, and fraudulent phone calls are all examples of this approach.
In many cases, attackers attempt to impersonate trusted organizations or individuals. When victims believe they are interacting with legitimate support staff or colleagues, they may be more willing to provide sensitive information.
For messaging platforms, verification codes and authentication tokens become attractive targets because they allow attackers to register accounts on their own devices.
Phone Number Authentication and Security Debate
The incident has also renewed debate among security researchers about phone number-based authentication systems. Signal accounts are tied to phone numbers, which simplifies onboarding and makes it easier for people to find contacts already using the app.
However, phone numbers can introduce certain security risks. SMS verification codes can be targeted through phishing attacks, SIM swapping, or other forms of social engineering.
Some privacy-focused messaging platforms have moved away from phone number identities entirely, instead using cryptographic identifiers or decentralized systems that do not rely on telecom infrastructure.
Despite these concerns, many platforms continue to use phone numbers because they provide a familiar and accessible way for users to create accounts.
Signal’s Response and Security Guidance
In response to the phishing campaign, Signal published a thread on X acknowledging reports of targeted phishing attacks that resulted in account takeovers affecting some users, including government officials and journalists. The company said it takes the issue seriously and made clear that its encryption and infrastructure were not compromised.
“We are aware of recent reports regarding targeted phishing attacks that have resulted in account takeovers of some Signal users, including government officials and journalists. We take this very seriously.
To be clear: Signal’s encryption and infrastructure have not been compromised and remain robust. These attacks were executed via sophisticated phishing campaigns, designed to trick users into sharing information – SMS codes and/or Signal PIN – to gain access to users’ accounts.”
Signal said the attacks relied on social engineering rather than any failure in the app’s encryption or backend systems. According to the company, attackers impersonated trusted contacts or services, including a fake “Signal Support Bot,” in order to persuade victims to hand over sensitive account information.
The company also emphasized that a Signal SMS verification code is only needed when a user is first signing up for the app. Outside of that registration flow, any request for a verification code or PIN should be treated as a phishing attempt.
Signal further stated that its support team will never initiate contact through in-app messages, SMS, or social media to ask for a verification code or Signal PIN. If anyone asks for any Signal-related code, the company says it is a scam.
In its guidance to users, Signal urged people to stay alert, avoid sharing SMS verification codes or Signal PINs with anyone, and treat unexpected requests for sensitive information with caution. The company said it will continue working on technical and interface-level safeguards to help reduce the success of phishing attacks.
Protecting Yourself from Phishing Attacks
Although the recent signal phishing attack targeted specific individuals, the techniques used are common across many online services. Understanding how these scams work can help users avoid becoming victims.
- Never share verification codes, passwords, or authentication tokens with anyone.
- Be cautious of messages claiming to be from support staff requesting account information.
- Verify unexpected requests through official websites or trusted contacts.
- Avoid clicking suspicious links that claim to restore or verify accounts.
- Block and report accounts that appear to be impersonating legitimate services.
Security experts often emphasize that verification codes are meant to prove ownership of an account. If someone asks for that code, they are effectively asking for access to the account itself.
Why the Signal Phishing Attack Stands Out
The signal phishing attack did not involve breaking encryption or breaching Signal’s servers. Instead, attackers targeted the people using the platform. By impersonating trusted contacts or fake services such as a “Signal Support Bot,” they convinced victims to voluntarily hand over verification codes or account PINs.
Those codes are meant to verify account ownership during registration. Once an attacker obtains one, they can register the account on another device and gain access without touching Signal’s encryption systems.
This kind of attack is common because it avoids the difficult part of cybersecurity. Breaking modern encryption is extremely hard, but convincing someone to reveal a verification code is often much easier.
Many people assume they would never fall for a social engineering attack, yet these incidents continue to happen across every major platform. Attackers succeed not because users are careless, but because the tactics are designed to exploit trust, urgency, and confusion. Even experienced professionals and high-profile figures fall victim to these schemes.
As digital communication becomes more central to everyday life, there is a growing argument that basic online security awareness should be treated as a core skill. In the future, it would not be surprising to see basic cybersecurity and phishing awareness included in school curricula, much like traditional safety education. Understanding how social engineering works may become just as important as understanding how to use the technology itself.
- CPUID Compromise Served Malware Through Official CPU-Z and HWMonitor Downloads
- FBI and CISA Warn Iran-Affiliated Actors Are Targeting PLCs Across U.S. Critical Infrastructure
- North Korea Hackers Tied to Axios npm Package Supply Chain Attack
- Axios Supply Chain Attack Pushes RAT Malware Through npm Install
- FBI Director Hacked by Iranian Hackers in Personal Gmail Leak
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













