The Santa Email Scam is a holiday themed phishing scheme that impersonates personalized Santa letter services and claims the recipient has been selected to receive a customized Christmas package. These emails appear legitimate at first glance and often contain festive imagery, limited time offers, free gift claims, and emotional messaging designed to appeal to parents. The goal is to lure victims into entering personal information and payment card details on fraudulent checkout pages that have no connection to any real holiday service.
This scam uses sender names such as “santas certified letter” but the emails originate from unrelated domains like jpnseotCXI@dibbert.biffalojp.com. The email includes a promotional image designed to look like a holiday offer and contains a clickable link redirecting users to an IP based landing page. From there, victims are pushed into a multi step funnel that collects names, addresses, children’s information, and full payment card data under the guise of ordering a personalized Santa letter.
These scams are widespread during the holiday season when threat actors rely on urgency, emotion, and seasonal expectations to increase conversion rates. None of the messages, offers, forms, or checkout pages used in this campaign are affiliated with any legitimate Santa letter service.
The Scam Email
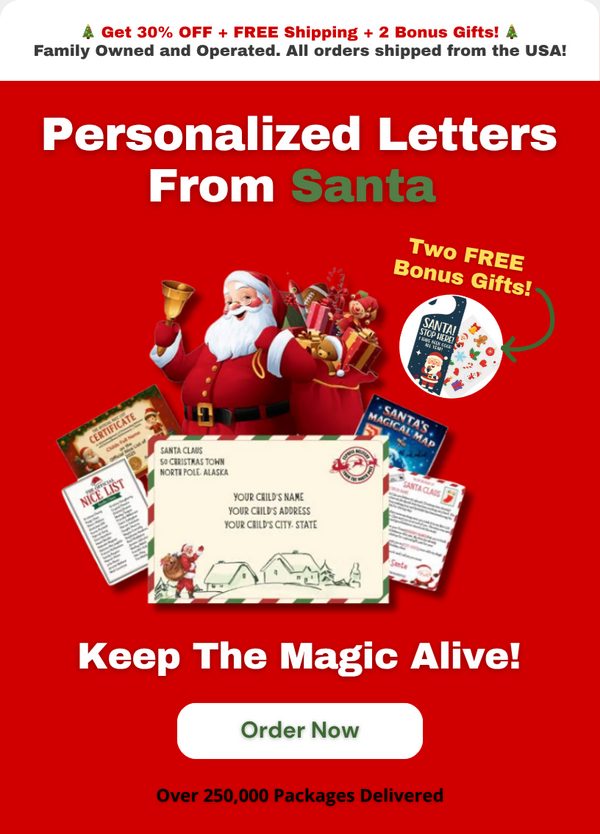
The scam begins with a brightly colored promotional email that claims the user has received an exclusive holiday offer involving personalized letters from Santa. The subject lines vary but follow the same theme, encouraging recipients to act quickly to keep the “magic alive.” The sender field impersonates a legitimate business, but the underlying domain is unrelated to any real company and is commonly used in phishing operations.
The message contains a large image that acts as the primary call to action. Clicking the image redirects users to an IP based URL hosted on a compromised or misused server:
http://syn-104-156-063-213.biz.spectrum.com/sdfqsdfqdfgssdfh.html
IP redirect links allow scammers to bypass filters that check for newly registered domains and are often used to rotate infrastructure quickly to avoid takedowns.
The Fake Santa Letter Offer Page
After clicking the email link, users are taken to a promotional offer page designed to resemble a legitimate holiday storefront. The page advertises personalized Santa letters, certificates, maps, stickers, and other themed items. It includes professionally styled graphics and claims to offer seasonal discounts, free shipping, and “two free bonus gifts.” The design is polished, but the purpose is to create trust and encourage victims to continue the process.
The page showcases example letters with customizable fields such as the child’s name, city, and additional personalized details. These elements strengthen the illusion that the site is legitimate. None of this content verifies authenticity. Instead, it serves as a psychological hook to initiate emotional buy in.

The Fake Customization Form
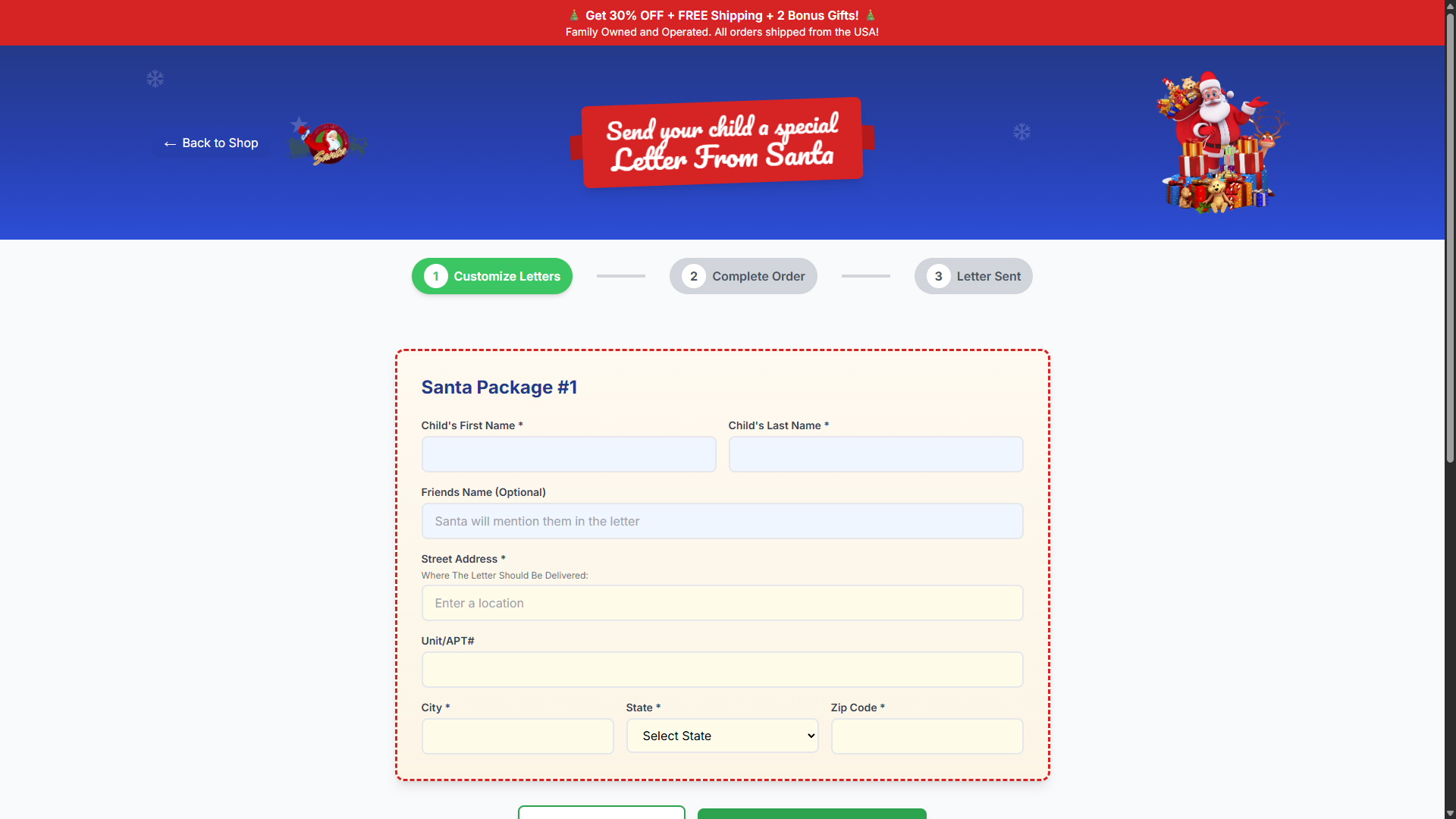
Clicking deeper into the site leads to a detailed form asking for a child’s first and last name, friends’ names, the child’s address, the parent’s address, and additional details. These fields are presented as customization options for the Santa letter package, but they function as data harvesting inputs. Scammers capture all information entered into these forms.
Victims are guided through a three step interface labeled “Customize Letters,” “Complete Order,” and “Letter Sent.” The first step gathers sensitive personal information that can be reused in identity theft, targeted scams, and data resale markets.
The Fraudulent Checkout Page
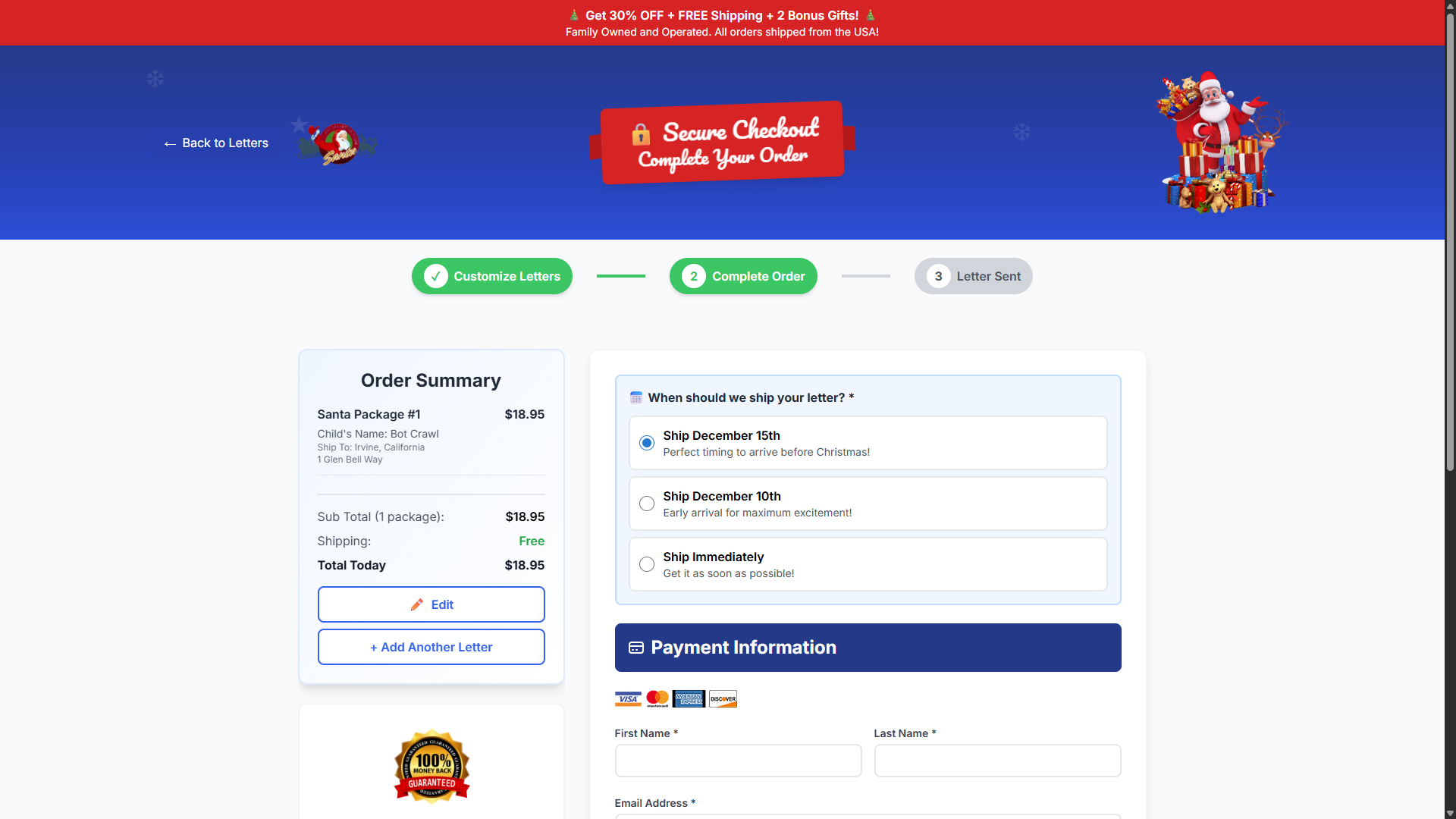
Once the user completes the customization form, the site redirects to a fake checkout page. This page appears professional, displaying order summaries, shipping dates, package descriptions, free shipping claims, and seasonal urgency language designed to push the victim into completing a purchase.
The final page requests:
- Full name
- Email address
- Billing address
- Shipping address
- City, state, and zip code
- Full payment card information
The checkout interface includes fake trust badges, SSL icons, and money back guarantees. These elements are commonly used in fraudulent ecommerce schemes to reduce suspicion and increase conversion. Submitting this information does not send any letters. Instead, it allows scammers to capture complete identity and payment details for unauthorized transactions and resale.
Domain Information and Registration Patterns
The primary domain associated with the checkout phase of this scam is santascertifiedletter.com. WHOIS data shows it was registered on October 15, 2025, with privacy protection enabled and multiple restriction statuses applied. Newly registered domains created during the holiday season with limited public history are a common indicator of fraudulent intent.
WHOIS Summary:
- Domain: santascertifiedletter.com
- Registrar: Cosmotown, Inc.
- Created: 2025-10-15
- Expires: 2026-10-15
- Status: clientDeleteProhibited, clientRenewProhibited, clientTransferProhibited, clientUpdateProhibited
- Name servers: NDNS1.COSMOTOWN.COM, NDNS2.COSMOTOWN.COM
The restrictive statuses and lack of operational history are typical in short lived phishing operations where domains are used briefly and abandoned after takedown risk increases.
Red Flags in the Santa Email Scam
- Sender addresses do not match any legitimate holiday service provider.
- Emails rely on emotional triggers involving children and holiday excitement.
- Clickable images link to IP based redirects instead of official domain names.
- The offer promises unrealistic discounts and bonus gifts.
- The customization form collects unnecessary personal details.
- Fake trust badges and security icons appear on the checkout page.
- Newly registered domains with no history are used for payment collection.
- No verifiable company information, address, or contact details are provided.
Why This Scam Is Effective
The scam exploits seasonal emotions, parental instincts, and holiday urgency. The design appears professional, the graphics are polished, and the messaging is crafted to appear family friendly. These factors lower suspicion and increase the likelihood that victims will complete each step in the funnel.
How to Protect Yourself
- Do not trust unsolicited holiday themed emails offering free gifts or special discounts.
- Check the sender’s domain for legitimacy.
- Verify offers directly on official websites.
- Never provide child specific information to unverified online services.
- Use caution with any page requesting full payment card information.
- If you clicked the link, scan your device with a reputable tool like Malwarebytes to ensure no hidden threats were installed.
If You Submitted Information
- Contact your bank or card issuer immediately.
- Request a new card and review recent transactions for fraud.
- Change passwords for any related accounts.
- Monitor for suspicious activity involving your identity or your child’s information.
- Run a malware scan on the device used during the incident.
How to Report the Scam
- FTC Report Fraud
- IC3 Internet Crime Complaint Center
- Your local consumer protection agency
- Your email provider’s phishing reporting feature
For more scam alerts and cybersecurity reporting, visit the Botcrawl scams category.
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
- OneDrive Email Scam: How It Works, Warning Signs, and How to Stay Protected
- Women and Children Support Foundation Email Scam Promises Fake $1 Million Donation
- Uphold Scam Uses Fake Data Breach Emails to Steal Accounts
- Prime Video Scam Emails Use Fake Payment Alerts to Steal Personal and Financial Information
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













