A new Integra Credit data breach claim has surfaced on a dark web forum, where the user ResPublica, also behind the Radius Global Solutions data breach, alleges they obtained 134,000 borrower records connected to Integra Credit and its parent company, Deinde Financial.
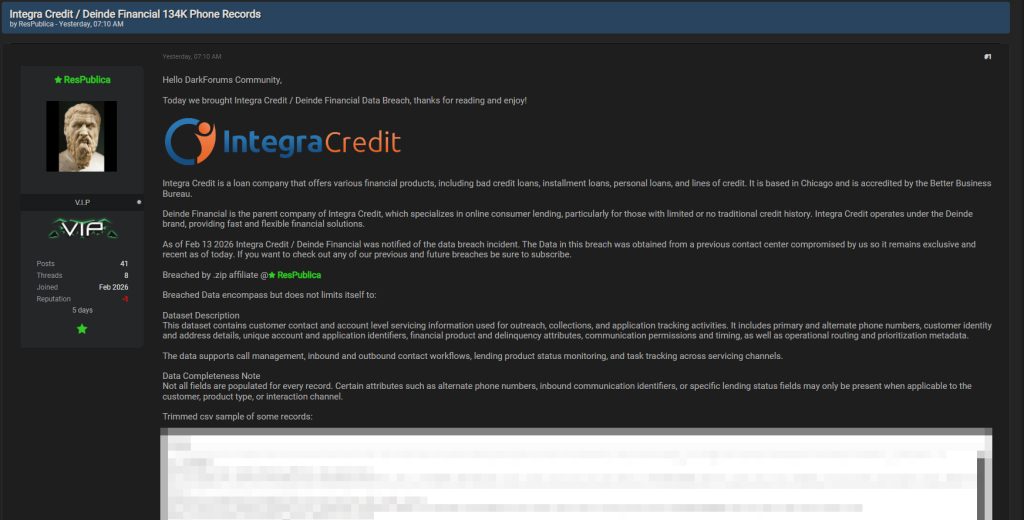
ResPublica says Integra Credit and Deinde Financial were notified on February 13, 2026. The post claims the dataset was pulled from a contact center environment previously compromised by the same source. A trimmed CSV sample is included in the thread alongside a written description of the fields that are allegedly present.
There is no public confirmation from Integra Credit or Deinde Financial at the time of writing.
What The CSV Sample Shows
The sample rows include primary phone numbers and multiple alternate phone fields, paired with first and last names and full mailing addresses. The excerpt also contains internal identifiers that resemble servicing and workflow keys, including customer_account_id, application_id, and financial_product_id.
Several entries show lending_product_status values such as issued, declined, provisioned, started, withdrawn, past_due, closed_sold, and closed_settlement. Some rows include past_due_amount figures and days_past_due_up_to values. The excerpt also shows can_contact_now and time_to_contact fields, along with customer_source values such as lending_exchange, organic, direct_mail, and lead_provider. The final columns contain routing or prioritization indicators that appear tied to outreach and queue handling.
Even in trimmed form, the structure reads like a servicing export built for call operations and account follow-up rather than a generic contact list.
What ResPublica Claims The Dataset Contains
The thread describes the data as contact and account-level servicing information used for outreach, collections, and application tracking. ResPublica claims the records include phone numbers, borrower identity and address fields, unique account and application identifiers, delinquency and product attributes, communication timing and permissions, and operational metadata tied to routing and prioritization.
The post also notes that not every field is populated for every record and frames missing values as normal for certain borrower types or interaction channels.
How This Kind Of Data Gets Abused
If the dataset is authentic, it gives scammers more than a way to reach someone. It gives them a script. A caller who already knows a borrower’s name, address, and a status flag like past_due can sound like they are reading from a real account screen. That is how collections-themed scams get traction. The caller does not need to guess. They can lead.
Status markers like provisioned, issued, or declined can also be used to tailor the pitch. Some scams lean on urgency and “final notice” language. Others play the opposite angle and claim a borrower has been approved for a new product or needs to “verify” details to finish an application. The more realistic the details are, the faster people comply.
Because the thread focuses heavily on phone fields, the most likely follow-on risk is vishing and SMS outreach. Borrowers should be skeptical of unexpected calls or texts that demand immediate payment, request personal verification details, or attempt to push links to “confirm” loan information.
Mitigation Steps For Integra Credit And Deinde Financial
If the Integra Credit data breach claim is accurate, response must move quickly from validation to containment. Contact center environments are high volume and process driven, which means even a short window of unauthorized access can generate large structured exports. The focus should be on verifying scope, restricting export pathways, and reducing the usefulness of any data that may already be in circulation.
Begin by identifying the precise system or workflow that generated the dataset described by ResPublica. Compare internal reporting schemas against the published column structure. Servicing platforms, dialer integrations, and application tracking tools often leave identifiable naming patterns. Narrowing this down reduces speculation and allows investigators to determine whether access occurred in a core production system, a vendor-managed contact center instance, or a reporting mirror.
Immediately restrict all bulk export permissions tied to customer contact and account servicing data. Export capability should be limited to a small number of supervised administrative roles. Add logging thresholds for large data pulls and require step-up authentication for report generation. Review historical export logs for anomalies, especially during nonstandard operating hours.
Conduct a comprehensive credential and access review across:
- Contact center VPN and remote desktop gateways
- Single sign-on platforms and identity providers
- CRM and collections management systems
- Third-party dialer and workforce management platforms
- Shared cloud storage or internal file repositories
Force password resets for privileged and supervisory roles. Enforce phishing-resistant multi-factor authentication for all staff with export capability. Remove dormant vendor accounts and confirm that former employees do not retain residual access.
Hunt for staging activity. Large CSV files are often compressed before exfiltration. Review endpoint telemetry for archive creation tools, unusual compression behavior, outbound transfers to unknown destinations, and abnormal data access patterns. If the environment includes endpoint detection tooling, prioritize historical review rather than waiting for live alerts.
Finally, prepare notification plans in parallel with technical containment. If borrower contact details were exposed, transparency reduces harm. Customers who know their phone numbers and servicing status may be circulating are less likely to fall for impersonation attempts.
Mitigation Steps For Lending Partners And Servicing Clients
Any bank, credit union, or funding partner referenced in servicing records should treat this as a vendor risk event until proven otherwise. Even if internal systems were not directly accessed, contact center data can be used to impersonate legitimate servicing programs.
Review all shared access pathways between your organization and Integra Credit or Deinde Financial. Confirm that vendor accounts follow least privilege principles and that no persistent administrative tokens remain active beyond operational necessity.
Increase monitoring for:
- Unusual access attempts referencing servicing queues or application IDs
- Emails or calls impersonating collections departments
- Password reset or account verification attempts tied to known borrower data
Reinforce call authentication procedures. Servicing operations often rely on knowledge-based verification. If names, phone numbers, and application statuses are circulating, knowledge-based checks become weaker. Introduce layered verification where feasible and require out-of-band confirmation for sensitive account changes.
Coordinate directly with Integra Credit to confirm whether any shared integrations, API keys, or data feeds require rotation. If your systems consume data from their servicing platform, verify integrity and confirm no unauthorized changes occurred.
Mitigation Steps For Individuals
If you have applied for or serviced a loan through Integra Credit, remain alert to impersonation attempts. The primary risk from a dataset like this is social engineering rather than direct system compromise.
Be cautious of unsolicited calls or texts referencing loan applications, declined applications, past-due amounts, or “account verification.” Fraudulent callers often create urgency. Do not provide one-time passcodes or full identity details to anyone who initiates contact.
Use official contact information from the company’s website or your existing account documentation if you need to verify a request. Never rely on callback numbers provided during a live call.
Strengthen your own account security posture:
- Use unique passwords for financial accounts and your primary email account
- Enable multi-factor authentication wherever available
- Monitor bank and credit activity for unexpected changes
- Consider placing a fraud alert if you suspect identity misuse
If you clicked a suspicious loan-related link or opened an unexpected attachment, scan your device for malware using a reputable security tool such as Malwarebytes.
Contact center breaches often lead to waves of follow-up scams that reuse accurate personal details. Awareness is a powerful defense. If the Integra Credit data breach claim is confirmed, the most effective response across all groups will be layered access control, reduced export capability, and consistent verification discipline.
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Rheem Manufacturing Data Breach Claim Follows Reported INC Ransom Listing
- Polycorp Data Breach Exposes 400GB of Internal Manufacturing Data
WordPress Bot Protection
Bot Blocker for WordPress
Monitor bot traffic, review live activity, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress dashboard.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







