Adobe is dealing with a major breach after an intrusion tied to Mr. Raccoon exposed 13 million support records, employee files, HackerOne submissions, internal documents, and other material tied to the company’s support environment. Readers following recent data breaches will recognize the scale immediately, but the structure of this breach is just as important as the number. Material reviewed in connection with the incident points to Adobe-linked support systems, Adobe cloud resources, and support-side data that appears to have been reachable through an outsourced access chain. Adobe’s main site is available at adobe.com.
The exposed data places this breach well beyond a minor helpdesk problem. Support platforms often accumulate years of customer interactions, billing issues, attachments, internal notes, escalations, and identity-related information. When access to that environment is lost at scale, the result is a real data breach with direct risk to customers, employees, researchers, and partners. That is the story here. This was not framed as a vague dark web boast or a recycled database listing with no substance behind it. The material circulating around the intrusion points to a live operational environment, real support-side access, and a large amount of sensitive data.
The path into the environment appears to have started with a compromised employee at an outsourced BPO operation tied to Adobe support workflows. From there, access was expanded by phishing the employee’s manager, opening a route into support-side systems. That sequence matters because it shows how a major company can suffer a breach without a dramatic break-in against its core network. The weak point appears to have been operational access, human compromise, and the amount of trust placed in connected support roles.
What Was Exposed
The Adobe data breach has been described as exposing 13 million support records. That figure alone makes this one of the larger support-side exposures tied to a major technology company in recent memory, but the makeup of the exposed material is what gives the breach its real weight.
The records tied to the breach have been described as including:
- 13 million support records or support tickets
- Roughly 15,000 employee records
- HackerOne submissions
- Internal documents
- Additional files tied to support operations and connected workflows
Support records are not trivial data. A single support ticket can contain names, email addresses, product details, subscription issues, billing problems, screenshots, attachments, account identifiers, internal case notes, and escalation histories. Across millions of records, that can produce a deep view of customer behavior, support processes, account disputes, internal workflows, and technical issues. Even when a support record does not contain full payment data or a formal government identifier, it can still be highly useful for phishing, impersonation, fraud, or extortion.
The employee data described in connection with the breach raises a separate set of risks. Employee records can support credential attacks, targeted phishing, internal impersonation, and social engineering against support staff or adjacent teams. In a breach like this, staff data matters not only because of employee privacy, but because internal records can make the next intrusion easier. If threat actors obtain enough context about staff roles, reporting lines, tool access, or internal communication patterns, the breach can become a staging ground for follow-on activity.
The inclusion of HackerOne submissions is especially serious. Bug bounty and vulnerability disclosure systems can contain security findings, proof-of-concept material, reproduction steps, internal triage notes, severity discussions, and information on vulnerabilities that may not yet be fully remediated. Exposure of that material can create risk for both the company and the researchers who submitted reports in good faith. It can also complicate disclosure timelines, internal remediation work, and coordination across security teams.
How Access Appears to Have Been Gained
The intrusion tied to the Adobe data breach appears to have started with a remote access tool delivered to a BPO employee through email. Once the employee’s system was compromised, access expanded through the phishing of that employee’s manager. That progression is familiar to anyone who tracks modern breach activity. Threat actors do not always need to break through hardened perimeter defenses if they can ride legitimate operational trust, harvest access from people, and move through connected business systems that were never designed to withstand hostile use.
This is one reason outsourced support relationships remain a recurring breach vector. A large company may have mature internal controls in some parts of its environment while still relying on third-party workflows, vendor-side identities, browser-based tools, and managerial approvals that carry broad operational reach. The attack path does not have to look dramatic to be effective. If one person can be reached through email and another can be phished into approving or exposing the next step, the rest can unfold quickly.
There is also a more specific problem in the Adobe breach narrative. The actor tied to the breach said the support environment allowed all tickets to be exported in a single request from an agent account. If that description is accurate, it points to an access model that deserves serious scrutiny. A support system holding millions of records should not be casually exportable at that scale from a low-friction operational position. Even where broad access exists for business reasons, strong auditing, export controls, segmentation, rate limits, and anomaly detection should make that kind of activity difficult to perform quietly or at all.
A mass export issue inside a support platform is not just an access-control problem. It is a visibility problem, a governance problem, and a data-minimization problem. If the account model inside the platform made it easy to pull large datasets, then the breach was not only about how the attacker got in. It was also about what the environment allowed once access existed.
What the Screenshots Suggest About Scope
Images circulated with the breach provide context that goes beyond a bare claim of access. The screenshots appear to show Adobe-branded cloud resources, including an Adobe SharePoint or OneDrive environment under an adobe-my.sharepoint.com domain. That is relevant because it suggests the intrusion touched active business resources tied to Adobe branding and workflow rather than a disconnected throwaway panel with little real value.
Other images appear to show an authenticated HackerOne session reached through single sign-on. That matters for obvious reasons. A signed-in vulnerability disclosure environment is not the kind of artifact that appears in a fake breach package assembled for attention. It points to access that intersects with real security operations, researcher submissions, and internal review channels.
The breach material has also been described as including webcam access to the compromised employee’s device, along with private conversations pulled from WhatsApp. That detail is ugly, but it fits the access path that has been described. Once a worker’s system is compromised through a remote access tool, the breach is no longer limited to tickets and dashboards. Endpoint compromise can expose local conversations, live sessions, stored files, and visual confirmation that the attacker is inside a real working environment.
Taken together, the screenshots and described materials present a coherent picture. This looks like a support-side breach rooted in human compromise, then expanded through workflow access and connected systems. It does not read like a blunt-force smash against Adobe’s core network. It reads like a practical intrusion into the support layer of a major company, which in many cases is more than enough to produce a damaging breach.
Why Support Records Can Be So Sensitive
People often hear the word support and assume low-value administrative data. That assumption does not hold up in large enterprise environments. Support systems can be among the most revealing repositories in a company because they sit at the point where customers disclose problems, staff document exceptions, attachments get uploaded, and internal notes are added over time.
A support record may include:
- Customer names and contact details
- Subscription and billing issues
- Refund or charge dispute information
- Product usage details
- Error screenshots and uploaded files
- Internal notes and case histories
- Escalation paths and approvals
- Technical diagnostics and account identifiers
Across millions of records, that can build an unusually rich target set. Attackers do not need full credit card numbers to exploit breach data. A believable billing reference, a real support case number, an authentic-looking screenshot, or a known product issue can make phishing emails and scams far more convincing. A user who has actually opened Adobe tickets in the past may be more likely to trust a message that references a real support context, even if the new message is fraudulent.
The same logic applies to employees and researchers. Staff who work inside support chains can be targeted with follow-up phishing, fake internal requests, impersonation attempts, or malicious document delivery. Researchers who submitted vulnerability reports could also become targets if their names, email addresses, or report content were exposed. In other words, the breach does not end with the first export. The first export creates new attack material.
Mr. Raccoon and the Operational Pattern Behind the Breach
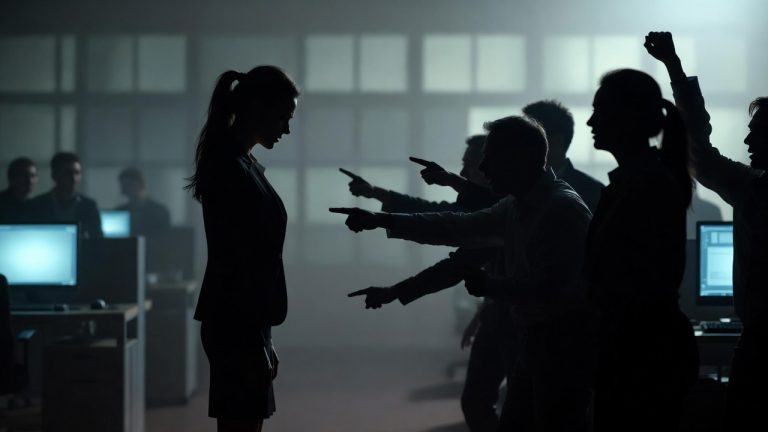
Mr. Raccoon has been tied to the Adobe data breach at a time when threat activity built around support operations, business process outsourcing, and human compromise continues to show how effective simple intrusion paths can be. Not every serious breach begins with a zero-day or a technically elegant exploit. In many cases, the breach begins with an employee receiving the wrong email, opening the wrong attachment, clicking the wrong prompt, or trusting the wrong request at the wrong moment.
That is one reason this Adobe breach is likely to draw attention well beyond Adobe itself. It reflects a pattern that other companies will recognize immediately. Large firms outsource operational work, connect support staff to internal systems, permit browser-based access to business tools, and rely on managers or adjacent roles to move cases forward. Those decisions may be efficient for business, but they also create chains of trust that attackers can test one person at a time.
There is nothing small about a breach just because the first compromised machine belonged to a support worker rather than an internal engineer. In some environments, support-side access is exactly where customer data, internal notes, and cross-system visibility concentrate. A threat actor does not need the most glamorous foothold. They need the foothold that opens the right doors.
Questions Adobe Will Need to Answer
Adobe now faces a set of practical questions that go beyond whether its core internal network was affected. The first is simple. How much of the described data is real, current, and complete? The second is narrower but just as important. How much access did support-side accounts actually have, and what export controls were in place around that access? The third is procedural. When did Adobe first detect suspicious activity, and how quickly was the compromised path closed?
There are also deeper questions around architecture and governance. Why could an operational account reach such a large volume of records? Were support tools segmented by region, role, or case type? Were large exports logged and reviewed? Did the environment use meaningful thresholds, alerts, or approval controls around bulk data access? Did Adobe require stronger access separation between vendor-side workflows and internally sensitive systems tied to employees or security operations?
The exposure of HackerOne material adds another layer. If bug bounty submissions were reachable from the same general access chain, Adobe will likely need to examine how disclosure material was stored, who could view it, how it was segregated, and whether report content could be copied or exported in bulk. Security programs depend on trust. If researchers believe their submissions can be exposed through weak workflow design, that can damage participation and confidence even after the immediate incident is contained.
Recommended Actions for Potentially Affected Individuals
Anyone who has opened Adobe support tickets, submitted attachments to Adobe support, discussed billing issues with Adobe, or filed security reports touching Adobe should treat this breach seriously and stay alert for follow-on abuse.
Useful steps include:
- Watch for phishing emails or messages referencing Adobe support, billing, refunds, subscriptions, or prior tickets
- Be cautious with links or attachments that appear to reference existing Adobe cases
- Review Adobe account activity and related email accounts for suspicious logins or password reset attempts
- Change passwords if the same credentials were reused elsewhere
- Enable stronger multifactor authentication where possible
- Monitor financial accounts for suspicious subscription or billing activity
- Use a trusted security tool such as Malwarebytes if you suspect your device may have been exposed to malicious follow-up content
People who submitted sensitive attachments or vulnerability reports should also pay attention to targeted outreach that appears unusually informed. The most effective scam messages are often the ones that contain just enough true context to feel legitimate. Breach data can provide that context.
Recommended Actions for Adobe
Adobe’s priorities now should be straightforward. First, it needs to determine the full scope of exposed records, affected systems, and exportable data types. Second, it needs to isolate the access path that connected the compromised BPO chain to Adobe-linked support resources. Third, it needs to review every role, permission set, export path, and single sign-on connection that may have widened the breach.
Immediate response measures should include:
- Forensic review of the compromised BPO access path and manager-level phishing chain
- Credential resets and token invalidation for affected accounts
- Audit of support-platform permissions, export functions, and administrative roles
- Review of single sign-on trust relationships tied to support and security workflows
- Assessment of whether HackerOne data, internal documents, or employee records were copied in bulk
- Notification planning for users, staff, and researchers whose data may have been exposed
- Improved segmentation between support systems, internal documentation, and vulnerability management environments
Adobe will also need to examine whether too much sensitive material was concentrated in connected support workflows. In many breaches, the technical compromise gets attention first, but the deeper lesson comes from architecture. A system that lets a support-side compromise grow into a multi-category exposure is a system that needs redesign, not just patching.
What This Breach Says About Third-Party Access
The Adobe data breach tied to Mr. Raccoon is a reminder that major companies do not only lose data through malware detonated across core internal networks. They also lose data through ordinary business structures that were never built with enough distrust. Outsourced support work, single sign-on, managerial approvals, browser-based access, and exportable support records can form a breach path that is quiet, practical, and highly effective.
That pattern matters far beyond Adobe. Many large organizations have spent years hardening public-facing infrastructure while leaving operational trust chains overly broad on the inside. The result is a breach model that does not always look spectacular, but can still expose millions of records and multiple classes of sensitive data in a single incident.
For continued coverage of major data breaches and related developments in cybersecurity, this story is one to follow closely as more detail emerges around the scope of exposed records, the exact systems reached during the intrusion, and Adobe’s eventual response.