What is the ykcol virus?
ykcol virus is ransomware in the Locky family of malware that encrypts files using RSA-2048 and AES-128 cryptography ciphers, appends the .ykcol file extension to the end of the file name, changes the file type to YKCOL File, and downloads a ransom note named ykcol.txt and ykcol.html (or other) on Windows Desktop and in every folder it encrypted files in. The ransomware will also download an image of the ransom note named ykcol.bmp and change Windows Desktop background to the image and display the image in a new window.
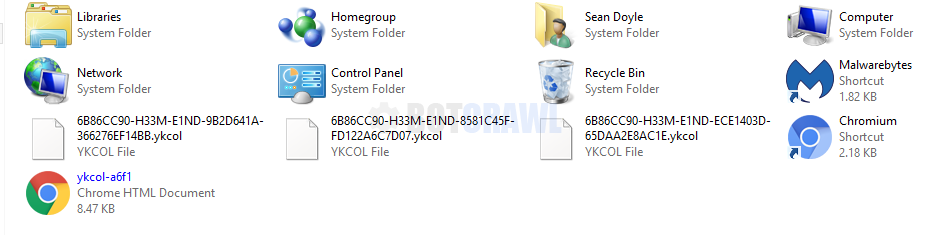
Once the ykcol virus has encrypted files it will download the ransom note and an image of the ransom note on Windows desktop and in folders it encrypted files in. The ykcol virus uses the ransom note to explain to victims of the virus what happened to their files and how to purcahse a decryption key and special tool to decrypt files the way that the malware authors want them to. In this case, the malware author suggest to send him an email.
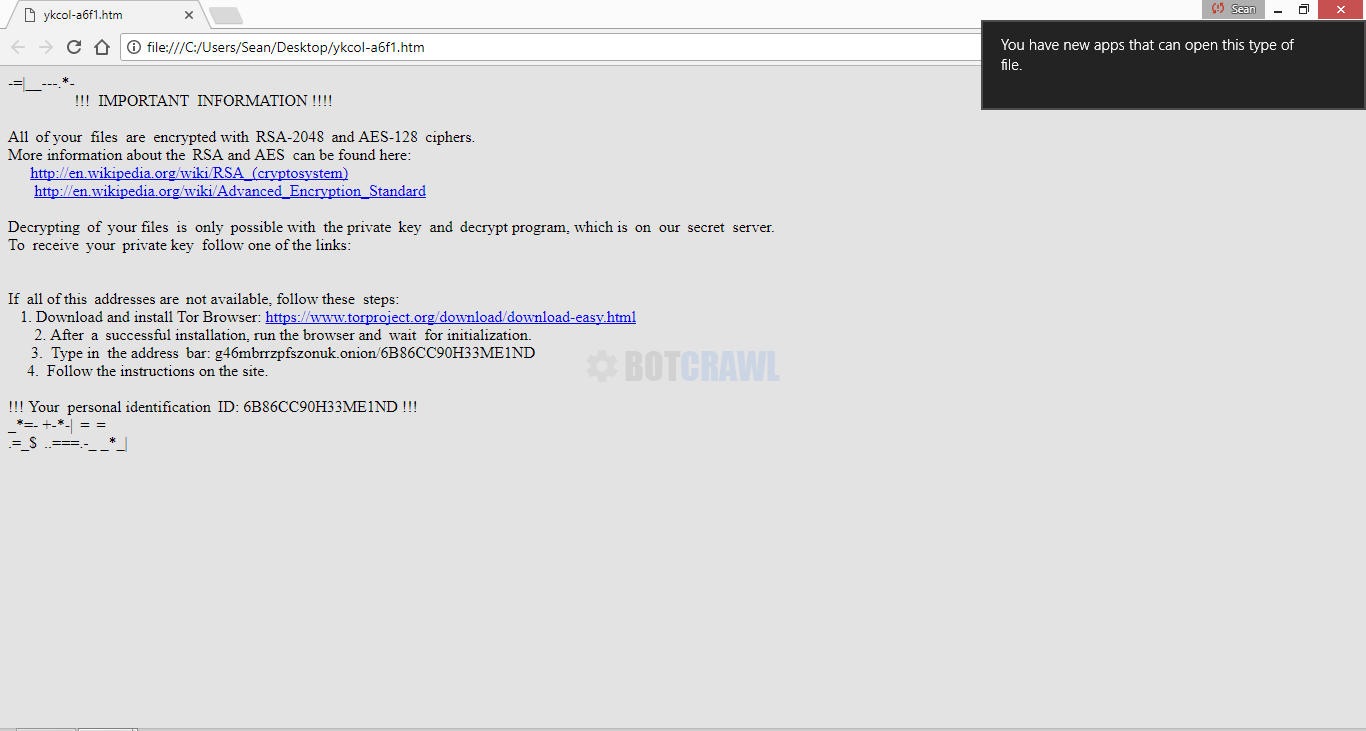
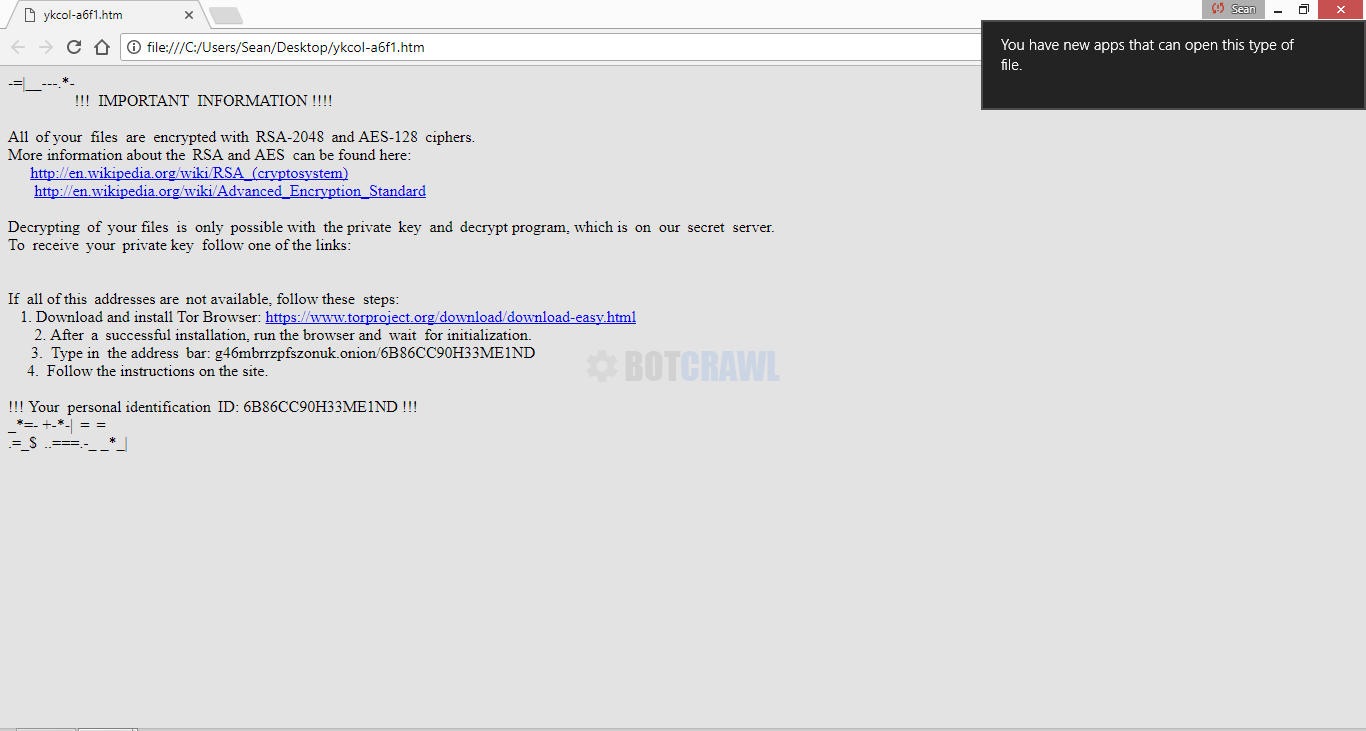
Here’s an example of one of the ransom notes used by ykcol ransomware:
-=|__—.*-
!!! IMPORTANT INFORMATION !!!!All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about the RSA and AES can be found here:
{links removed}
Decryption of your files is only possible with the private key and decrypt programs, which is on our secret server.
To receive your private key follow one of the links:
{no links provided}
If all of this addresses are not available, follow these steps:
1. Download and install Tor Browser: {link removed}
2. After a successful installation, run the tor browser and wait for initialization.
3. Type in the address bar: {link removed}
4. Follow the instructions on the site.
!!! Your personal identification ID: {ID removed} !!!
_*=- erqzdxfuz+-*-|c=aznofojysd=crnxqzkk
.=_$a..===.-_ _*_|b
Like most ransomware infections, the ykcol virus is typically spread by email spam messages that contain malicious .zip or .rar email attachments. Once the attachment is downloaded and executed it will spread the malware across the machine and begin its encryption process.
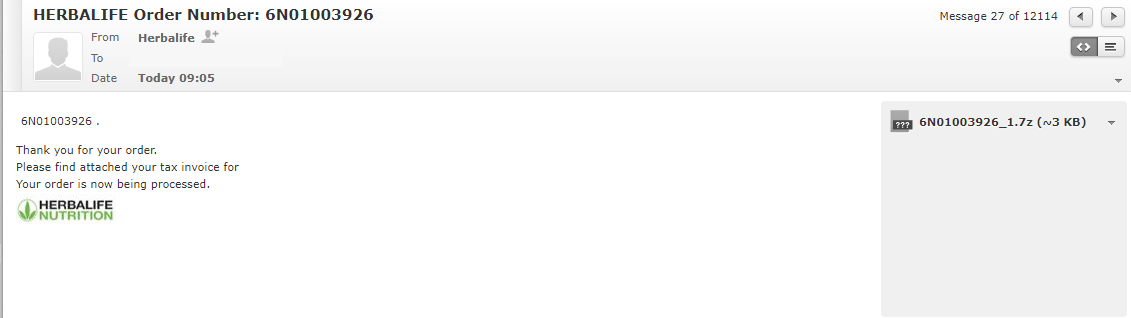
The particular email we found the sample in was a fake Herbalife email message that said “Thank you for your order” and “Please find attached your tax invoice.” The attached .zip extracted a .vbs file. When the .vbs file was executed the malware spread across the machine.
HERBALIFE Order Number: 6N01003926 From Herbalife 6N01003926_1.7z (~3 KB) 6N01003926 . Thank you for your order. Please find attached your tax invoice for Your order is now being processed.
The instructions on this page explain how to remove ykcol virus, ransomware, malware, and decrypt files encrypted with the .ykcol file extension. Follow each step below to remove this infection and secure your computer from malicious threats. On the bottom of this guide you will also find recovery and decryption software for various ransomware infections.
1. Remove ykcol with Malwarebytes
BUY NOW FREE TRIAL FREE DOWNLOAD
- Open your browser window and download Malwarebytes 3.0 Premium or Malwarebytes Anti-Malware Free.
- Open the executable file (mb3-setup.exe) to begin installing Malwarebytes.
- Select your language, click Next, then select “I accept the agreement,” click the Next button several times, and then click the Install button to install Malwarebytes. Click Finish once the install process is complete.
- Open Malwarebytes and click the Scan Now button on the Dashboard to begin scanning your computer.
- Click the Quarantine Selected button once the scan is finished.
- If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
2. Remove trace files with HitmanPro
- Open your browser window and download HitmanPro.
- Open the executable file (hitmanpro_x64.exe or hitmanpro_x32.exe) to begin installing HitmanPro.
- Click the Next button, check “I accept the terms of the license agreement,” and click the Next button again.
- On the Setup page select “Yes, create a copy of HitmanPro so I can regularly scan this computer (recommended)” and add your email address to the registration fields to begin the free trial.
- Click Next to begin scanning your computer.
- Once the Scan results are displayed click the Next button and click the Next button again on the Removal results page.
3. Clean up and repair issues with CCleaner
BUY NOW FREE TRIAL FREE DOWNLOAD
- Open your browser window and download CCleaner Professional or CCleaner Free.
- Open the executable file (ccsetup.exe or other) to begin installing CCleaner.
- Click the Install button to begin stalling the program.
- Click Run CCleaner to open the program when installation is complete.
- Select the Cleaner tab and click the Analyze button.
- When the Analyze process is complete click the Run Cleaner button to clean all files.
- Next, select the Registry tab and click the Scan for Issues button to scan for issues in your registry.
- When the scan is complete click the Fix selected Issues button and Fix All Selected Issues button to fix the issues.
- Next, select the Tools tab and click Startup. Examine each area, search for suspicious entries, and delete any suspicious startup entries by selecting the entry and clicking the Delete button.
- Next, click Browser Plugins and search each internet browser for unwanted browser add-ons and extensions. Click the extension you want to delete and click the Delete button to remove it.
File Recovery Software
| NAME | DESCRIPTION | DOWNLOAD |
|---|---|---|
| Shadow Explorer | Restores lost or damaged files from Shadow Copies | Download (Free) |
| Photorec | Recovers lost files | Download (Free) |
| Recuva | Recovers lost files | Download (Free) | Buy |
Troubleshoot
Alternative methods are suggested if there are issues removing ykcol ransomware from an infected computer.
How to Restore your computer
If a restore point has previously been established on your machine you will be able to perform a system restore in order to restore your machine to a date and time before it was infected. You will lose files on your computer that were obtained prior to the restore point.
There are several options to restore your computer. Most computers have their own restore software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default restore program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
How to Recover your computer to factory settings
A system recovery (or reset) will recover your computer to factory settings. You will lose the current programs and files on your computer.
There are several options to recover your computer to factory settings. Most computers have their own recovery software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default recovery program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
- Shai-Hulud Malware Clone Powers New Npm Infostealer and DDoS Campaign
- FBI Seeks Info in Steam Malware Investigation
- GhostPoster Browser Extensions Reached 840,000 Installs Before Removal From Stores
- Kimwolf Android Botnet Exploits Residential Proxies to Breach Internal Networks
- ClickFix Attack Uses Fake Windows BSOD Screens to Deploy Malware
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.