The Washington Post data breach was publicly revealed when the newspaper appeared on the Clop ransomware group’s leak site, following a widespread cyberattack exploiting vulnerabilities in Oracle’s E-Business Suite platform. The listing identified The Washington Post as a confirmed victim of the same global campaign that has compromised over 100 organizations worldwide. Security analysts discovered the entry on Clop’s dark web portal, which included business details and a message accusing the company of ignoring cybersecurity protections. The inclusion of the newspaper on this leak site represents a major escalation in cyber threats targeting the media and publishing industry.
Background
The Washington Post confirmed the breach on November 6, 2025, stating that it “was among the victims impacted by the breach of the Oracle E-Business Suite platform.” The Oracle system, used by major corporations to manage critical functions such as finance, logistics, and human resources, was recently targeted in a sophisticated global exploit. According to cybersecurity experts, this campaign leveraged a previously unknown vulnerability to gain unauthorized access to connected systems and exfiltrate large amounts of data.
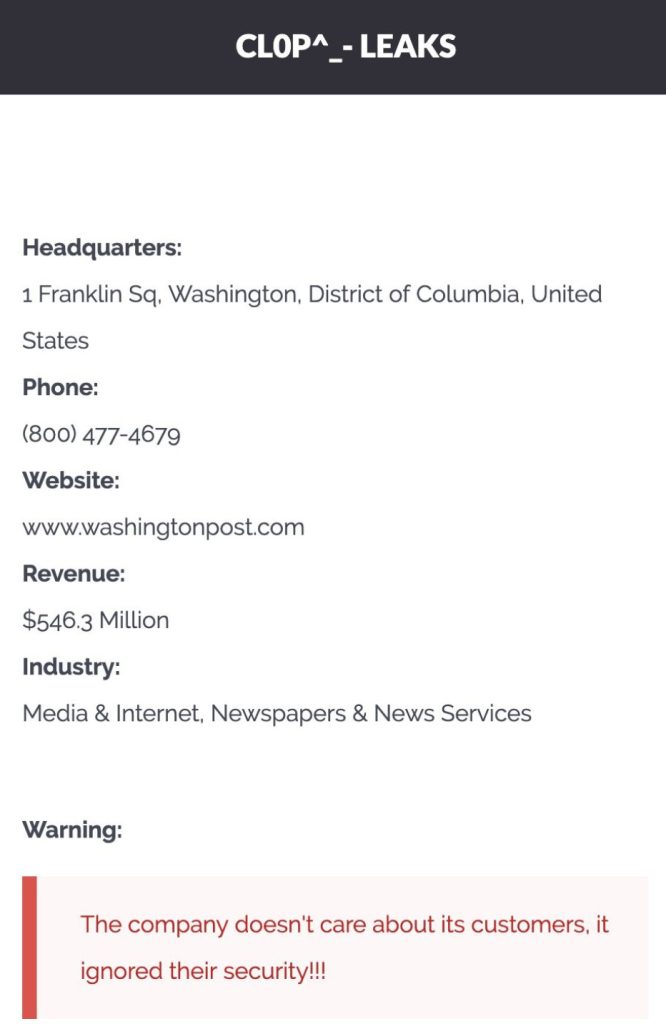
In its dark web post, Clop claimed responsibility for the Washington Post data breach, naming the organization among its expanding list of victims. The group’s post included metadata and financial details about The Washington Post, as well as a standard warning implying that the company’s data would be released if a ransom was not paid. This tactic is consistent with Clop’s approach in earlier attacks, where it uses public exposure as leverage to pressure victims into compliance.
Who Is the Clop Ransomware Group?
Clop (Cl0p) is a financially motivated ransomware and extortion operation that has been active since at least 2019. The group is believed to be part of a larger cybercrime ecosystem operating primarily from Eastern Europe. Clop’s activities surged to global attention in 2023 following its exploitation of the MOVEit Transfer software, which led to one of the largest data breach waves in history, affecting hundreds of companies and government agencies.
Unlike traditional ransomware that encrypts files and demands payment for decryption keys, Clop’s modern campaigns focus on data theft. The group infiltrates systems, exfiltrates sensitive information, and then threatens to publish it on its public leak site if the ransom is not paid. This “double extortion” model allows Clop to inflict reputational damage even when victims restore their systems without paying. The Washington Post data breach follows this same pattern, reinforcing Clop’s ongoing strategy of targeting high-profile organizations to generate attention and credibility within the cybercriminal community.
How the Oracle Exploit Works
Oracle’s E-Business Suite is a complex enterprise resource planning (ERP) system used by thousands of large organizations to manage essential business processes. In this campaign, attackers appear to have exploited a zero-day vulnerability or misconfigured access controls within the Oracle environment. Once inside, the attackers moved laterally through connected networks to extract sensitive operational and financial data. Because Oracle’s software is used to handle both internal and customer-facing operations, the impact of such a breach can be widespread and difficult to contain.
Experts believe that Clop’s campaign may have compromised data from a wide range of industries, including media, manufacturing, healthcare, and logistics. The attackers are known for timing their leaks strategically, posting new victims gradually to maintain public attention and increase ransom pressure. The appearance of The Washington Post on Clop’s site indicates that the attackers view it as a valuable target both for ransom potential and for the publicity associated with breaching a globally recognized news outlet.
Potential Data Exposed
The Washington Post has not disclosed the nature of the compromised data. However, based on similar incidents involving Oracle E-Business Suite breaches and Clop’s established patterns, the exposed information may include:
- Employee records such as names, emails, and department roles
- Vendor or business partner information linked to Oracle systems
- Financial and operational data stored within enterprise databases
- Subscriber or payment records tied to account management
- Internal communications or editorial workflow data
If sensitive data related to journalists, sources, or editorial investigations was accessed, this could create additional risks beyond financial or regulatory concerns. Cyberattacks on news organizations can pose a serious threat to press freedom and the safety of reporters, especially when confidential materials are involved. Even partial leaks of internal data could be used to undermine trust, target employees, or disrupt ongoing investigations.
Key Cybersecurity Insights
The Washington Post data breach highlights several urgent cybersecurity lessons relevant to organizations of all sizes:
- Third-party vulnerability risk: Even the most security-conscious organizations can be compromised through third-party software providers such as Oracle.
- Ransomware without encryption: Clop’s approach of focusing on extortion through data theft rather than encryption makes traditional backup recovery strategies insufficient.
- Reputation as a weapon: High-profile companies like The Washington Post are targeted not only for financial gain but also for the public exposure that amplifies pressure to pay.
- Supply chain security: The Oracle exploit has once again demonstrated the fragility of global software supply chains and the need for proactive risk monitoring.
Regulatory and Legal Implications
As a U.S.-based company operating globally, The Washington Post is required to comply with multiple data protection and privacy laws, including state-level breach notification requirements and potentially international frameworks such as the General Data Protection Regulation (GDPR). If personal or subscriber data was compromised, the company may be obligated to report the incident to affected individuals and regulators. Failure to comply with these obligations could result in significant financial penalties and legal challenges.
The breach also underscores broader concerns about cybersecurity in the media sector. News organizations often hold sensitive personal and political information that, if leaked, could have far-reaching implications. In response, cybersecurity experts recommend that media outlets strengthen access controls, increase employee security awareness, and continuously audit third-party systems for vulnerabilities.
Mitigation Strategies
For The Washington Post
- Engage a digital forensics and incident response (DFIR) firm to perform a full-scale investigation of Oracle-integrated systems and confirm the extent of data exposure.
- Work with Oracle and law enforcement agencies to verify and patch vulnerabilities in the E-Business Suite environment.
- Temporarily restrict administrative access to affected systems until a full security review is complete.
- Implement continuous monitoring for signs of intrusion or data exfiltration.
- Communicate transparently with employees, partners, and subscribers regarding potential risks and ongoing security measures.
For Affected Individuals
- Be cautious of any communications claiming to represent The Washington Post or Oracle that request personal information or payments.
- Change any reused passwords associated with your Washington Post or Oracle-related accounts.
- Enable multi-factor authentication on all critical accounts to prevent unauthorized access.
- Use a trusted cybersecurity solution such as Malwarebytes to scan for malware and protect against phishing threats.
- Monitor bank statements and credit reports for unusual activity and consider enrolling in an identity theft protection service.
Global Implications and Ongoing Investigation
The Washington Post data breach is part of a much larger campaign by Clop that continues to unfold across multiple sectors. Security researchers are still analyzing the Oracle E-Business Suite vulnerability that made the intrusion possible. Meanwhile, law enforcement agencies in the United States and Europe are collaborating to trace the infrastructure used by the attackers.
For the media industry, the incident serves as a critical reminder that journalism is no longer insulated from large-scale cyber threats. The combination of high public visibility, sensitive data, and reliance on third-party systems makes news organizations increasingly attractive targets for ransomware and espionage campaigns.
The Washington Post has stated that it continues to investigate the situation and will take appropriate steps to strengthen security moving forward. Until further information is released, the scope and impact of the breach remain under review. For ongoing updates and detailed cybersecurity coverage, visit Botcrawl’s data breaches and cybersecurity categories.
- ServiceNow Data Breach Exposes Customer Tenants to Unrestricted API Access
- GitHub Data Breach Confirmed After Poisoned VS Code Extension Exfiltrates Internal Repositories
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













