What is VPNTop Miner?
VPNTop Miner (also called Shadowsocks) is a Trojan that uses CPU processing power to mine digital CryptoCurrency. When VPNTop Miner has infected a computer it will create a scheduled task that executes a miner called Websock.exe. The miner then connects to a server and attempts to mine for coins by using all of the resources of your computer’s processor. VPNTop Miner will use all of the available CPU power of the computer it is installed on to mine for coins.
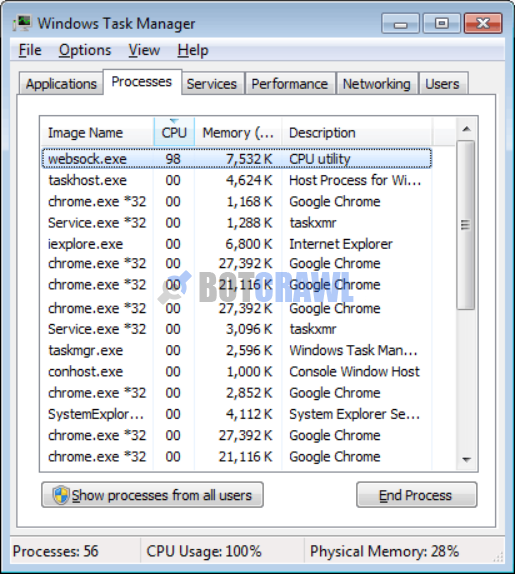
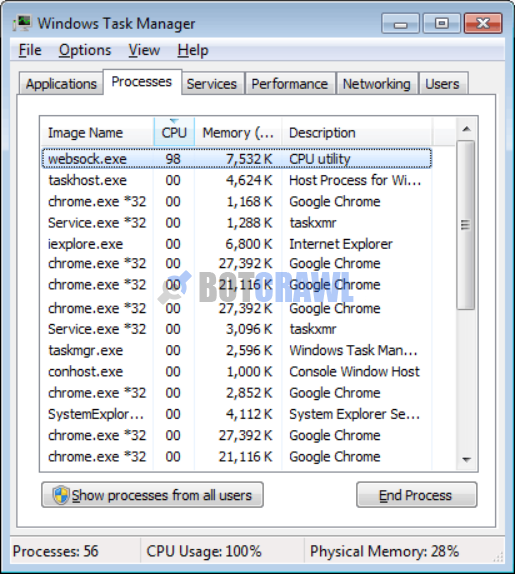
Once the VPNTop Miner miner is installed you will notice a process named Websock.exe with a description that says CPU Utility running in the task manager. You will also see a process called Service.exe running in the task manager that has a description that says taskxmr.
Since the VPNTop Miner miner will use a large amount of CPU power it can cause your CPU to run at very hot temperatures for extended periods of time. This can shorten the life of the CPU and cause your computer to become slow and crash.
Like most Trojans and malware, VPNTop Miner is known to install without consent and bundle with other potentially unwanted programs, adware, spyware, malware, and dangerous computer viruses.
How was VPNTop Miner installed?
The VPNTop Miner program is known to download and install without user consent. This is usually performed by a third-party download manager or Trojan downloader that has initially infected the computer.
The VPNTop Miner program is also offered as a custom installation by freeware and other content such as codecs, media players, and updates; However, the installation process typically does not allow the user to reject VPNTop Miner from installing and the program will install anyways.
It is important to avoid installing free programs online that offer this program as an installation because they are not usually safe to download themselves.
How to remove VPNTop Miner (Removal Steps)
The VPNTop Miner removal steps on this page will remove VPNTop Miner, viruses, malware, and other threats completely from your computer.
1. Open your browser window and download Malwarebytes 3.0 Premium or Malwarebytes Anti-Malware Free.
BUY NOW FREE TRIAL FREE DOWNLOAD
2. Open the executable file (mb3-setup.exe) to begin installing Malwarebytes.
3. Select your language, click Next, then select “I accept the agreement,” click the Next button several times, and then click the Install button to install Malwarebytes. Click Finish once the install process is complete.
4. Open Malwarebytes and click the Scan Now button on the Dashboard to begin scanning your computer.
5. Click the Quarantine Selected button once the scan is finished.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Open your browser window and download HitmanPro.
8. Open the executable file (hitmanpro_x64.exe or hitmanpro_x32.exe) to begin installing HitmanPro.
9. Click the Next button, check “I accept the terms of the license agreement,” and click the Next button again.
10. On the Setup page select “Yes, create a copy of HitmanPro so I can regularly scan this computer (recommended)” and add your email address to the registration fields to begin the free trial.
11. Click Next to begin scanning your computer.
12. Once the Scan results are displayed click the Next button and click the Next button again on the Removal results page.
13. Open your browser window and download CCleaner Professional or CCleaner Free.
BUY NOW FREE TRIAL FREE DOWNLOAD
14. Open the executable file (ccsetup.exe or other) to begin installing CCleaner.
15. Click the Install button to begin stalling the program.
16. Click Run CCleaner to open the program when installation is complete.
17. Select the Cleaner tab and click the Analyze button.
18. When the Analyze process is complete click the Run Cleaner button to clean all files.
19. Next, select the Registry tab and click the Scan for Issues button to scan for issues in your registry.
20. When the scan is complete click the Fix selected Issues button and Fix All Selected Issues button to fix the issues.
21. Next, select the Tools tab and click Startup. Examine each area, search for suspicious entries, and delete any suspicious startup entries by selecting the entry and clicking the Delete button.
22. Next, click Browser Plugins and search each internet browser for unwanted browser add-ons and extensions. Click the extension you want to delete and click the Delete button to remove it.
Your computer should now be free of potentially unwanted programs, malware, and other threats. If you have any issues please leave a comment in the comment section below.
- Shai-Hulud Malware Clone Powers New Npm Infostealer and DDoS Campaign
- FBI Seeks Info in Steam Malware Investigation
- GhostPoster Browser Extensions Reached 840,000 Installs Before Removal From Stores
- Kimwolf Android Botnet Exploits Residential Proxies to Breach Internal Networks
- ClickFix Attack Uses Fake Windows BSOD Screens to Deploy Malware
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.