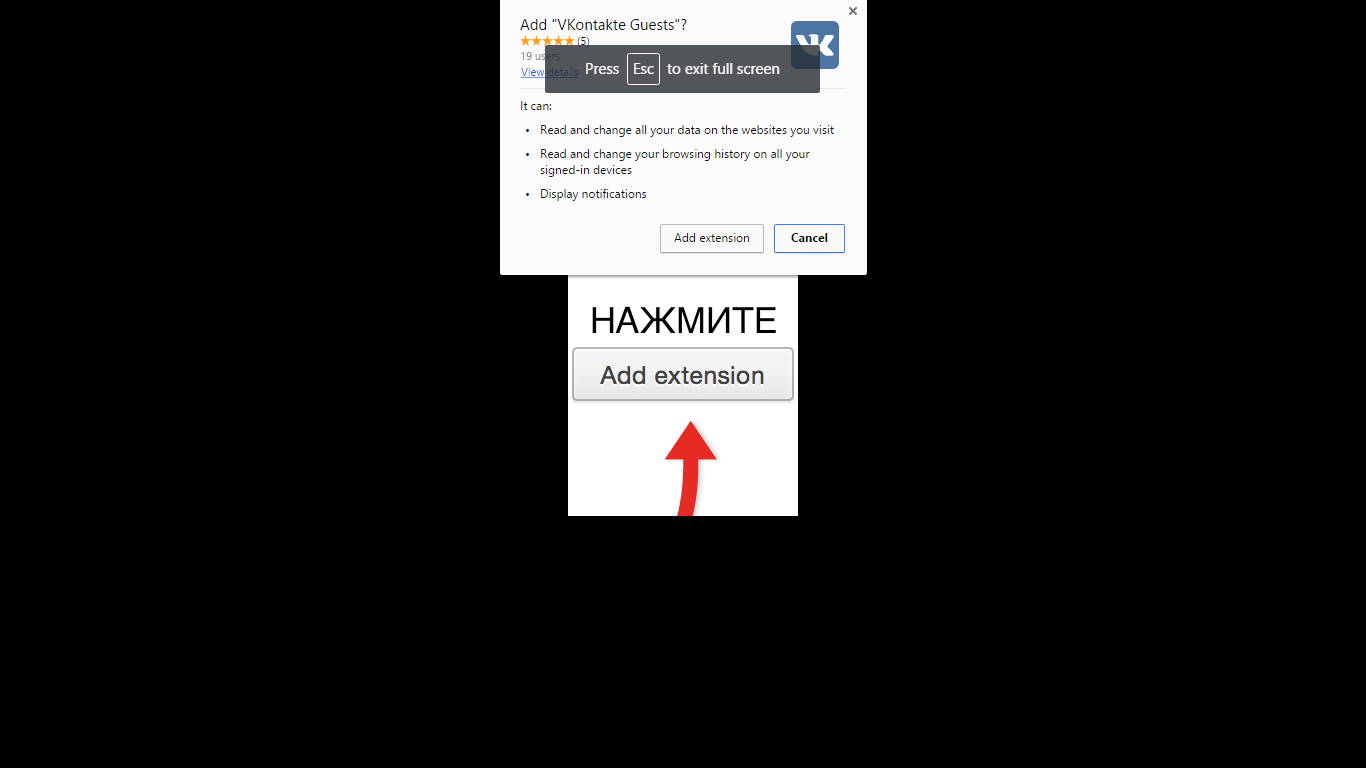
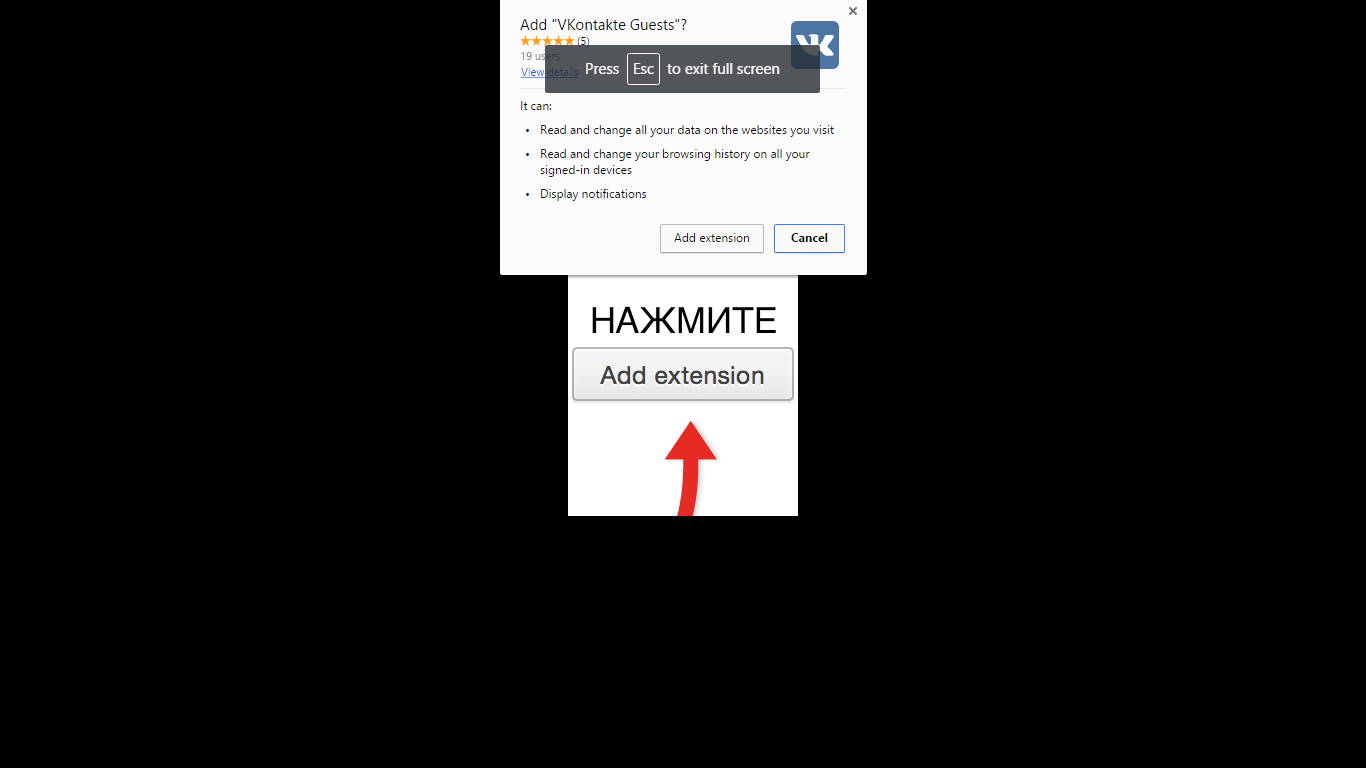
VKontakte Guests is a malicious browser extension that forces victims to install it by using full-page advertisements.
VKontakte Guests is recognized as a malicious and deceptive browser extension that can read and change all your data on the websites you visit, read and change your browsing history on all your signed-in devices, display notifications, and more. The VKontakte Guests extension is also know to utilize unethical marketing practices that technically force users to install the extension against their will. The extension will employ a browser-lock screen that restricts access to everything else on the computer and continuously sends messages forcing the user to install the extension to close the lock-screen.
The VKontakte Guests extension has the capabilities to replace your homepage, new tab page, and search engine with a commercial website in order to hijack your search results and generate revenue from search content and advertisements once it is installed. It will also show an icon in the browser menu that when clicked will redirect users to the same website.
What is VKontakte Guests?
VKontakte Guests is promoted as a free utility for Google Chrome. However, once installed the extension will modify your browser and generate pop-up ads, pop-under ads that take up a new browser window, in-text ads that turn text into hyperlinks, and generic banner-type ads that can additionally cover-up legitimate advertisements on the webpages you visit.
If this extension is installed on your machine you might notice some or all of these symptoms:
- Pop-up ads, pop-under ads, in-text ads, and banner advertisements
- Sponsored search results and new advertisements that appear when you search the web
- Modified homepage, new tab page, and search engine
- Slow and sluggish computer
- Internet browser crash
- Can bundle with malware, PUPs, adware, spyware, and other threats
A major concern with VKontakte Guests is that it bundles along with and is advertised alongside other potentially unwanted programs, malware, and potentially malicious trace files that can remain hidden on your computer system. If you did not install VKontakte Guests but find it installed on your computer it is likely that the threat was part of a package alongside other malicious objects that should be removed as soon as possible.
Removing VKontakte Guests virus and other threats that come along with it immediately from your computer or device is heavily advised. This program has a bad online reputation and may be the sign of a more serious computer infection. To completely remove VKontakte Guests and other threats from your computer use the removal guide below.
How did VKontakte Guests virus get onto my computer?
This browser hijacker is usually distributed like most common unwanted programs are. The hijacker can be contracted via free downloadable content, including freeware and torrent files. It may also be advertised as something it is not in order to trick victims into installing it and other potentially unwanted programs and malware.
The extension can be advertised across various websites. It is usually advertised on websites that contain prohibited content such as video streaming websites and pornography websites. These websites will also advertise malware and other threats. The advertisements that promote this extension may also promote other threats if clicked.
The browser extension is often bolstered by third-party download managers for freeware programs. The download managers may offer this adware as a custom install and give the user a chance to accept or decline the offer to install this extension and others. If the user does not opt out the program will install in the background. The way that the custom installation is presented may also be inadequate and designed to trick the user into installing programs they did not mean to install. It’s advised to be alert when installing free programs from the internet and keep an eye out for custom installation presentations to avoid any confusion and security risks.
How to remove VKontakte Guests (Removal Guide)
- STEP 1: Scan your computer for malware
- STEP 2: Manually repair your browser settings
- STEP 3: Manually uninstall programs
- TIPS: How to stay protected against future infections
STEP 1: Scan your computer for malware
The best way to remove VKontakte Guests and other threats from your computer is to scan your computer for malware using Malwarebytes Anti-Malware and HitmanPro softawre. Malwarebytes and HitmanPro will locate and eradicate this threat and other malicious files installed on your machine automatically.
1. Download and Install Malwarebytes Anti-Malware software to run a scan and remove malicious files from your computer.
2. Once installed, open Malwarebytes and click the Scan Now button – or go to the Scan tab and click the Start Scan button.
3. When the Malwarebytes scan is complete click the Remove Selected button.
4. To finish the Malwarebytes scan and remove detected malware click the Finish button and reboot your computer if promoted to do so.
5. Download and Install HitmanPro by Surfright to perform a second-opinion scan and remove any remaining malicious trace files.
6. Once installed, open HitmanPro and click Next to start scanning your computer. *If you are using the free version you may chose to create a copy or perform a one-time scan.
7. When the HitmanPro scan is complete click the Next button.
8. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
9. Click the Reboot button.
Your computer should now be free of VKontakte Guests and other threats completely; However, you can still use the manual repair and uninstall instructions below if your browser settings have not been repaired or if you think an unwanted program is still installed on your machine.
STEP 2: Manually repair your browser settings
If your browser settings have been changed use these instructions to manually repair your settings.
- How to change your Google Chrome homepage
- How to change your Google Chrome search engine
- How to remove extensions from Chrome
- How to change your Mozilla Firefox homepage
- How to change your Mozilla Firefox search engine
- How to remove add-ons from Firefox
- How to change your Microsoft Internet Explorer homepage
- How to change your Microsoft Internet Explorer search engine
- How to remove add-ons from Internet Explorer
STEP 3: Manually uninstall programs
If you are infected with adware and other unwanted programs you might be able to manually uninstall programs from your computer. Use these instructions to uninstall unwanted programs that may have installed on your machine. If you do not find a program installed on your machine make sure to scan your computer for malware using the instructions above.
TIPS: How to stay protected against future infections
The key to staying protected against future infections is to follow common online guidelines and take advantage of reputable Antivirus and Anti-Malware security software with real-time protection.
Real-time security software
Security software like Malwarebytes and Norton Security have real-time features that can block malicious files before they spread across your computer. These programs bundled together can establish a wall between your computer and cyber criminals.

Common Online Guidelines
- Backup your computer and personal files to an external drive or online backup service
- Create a restore point on your computer in case you need to restore your computer to a date before infection
- Avoid downloading and installing apps, browser extensions, and programs you are not familiar with
- Avoid downloading and installing apps, browser extensions, and programs from websites you are not familiar with – some websites use their own download manager to bundle additional programs with the initial download
- Avoid visiting fake “spyware removal” blogs and websites that promote “spyware removal software.” These are usually malicious websites designed to phish your personal information, infect your computer with a rogue program and trick you into paying for rogue “spyware removal software.”
- If you plan to download and install freeware, open source software, or shareware make sure to be alert when you install the object and read all the instructions presented by the download manager
- Avoid torrents and P2P clients
- Do not open email messages from senders you do not know
- FBI Seeks Info in Steam Malware Investigation
- GhostPoster Browser Extensions Reached 840,000 Installs Before Removal From Stores
- Kimwolf Android Botnet Exploits Residential Proxies to Breach Internal Networks
- ClickFix Attack Uses Fake Windows BSOD Screens to Deploy Malware
- DroidLock Malware Locks Android Phones and Demands Ransom
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.