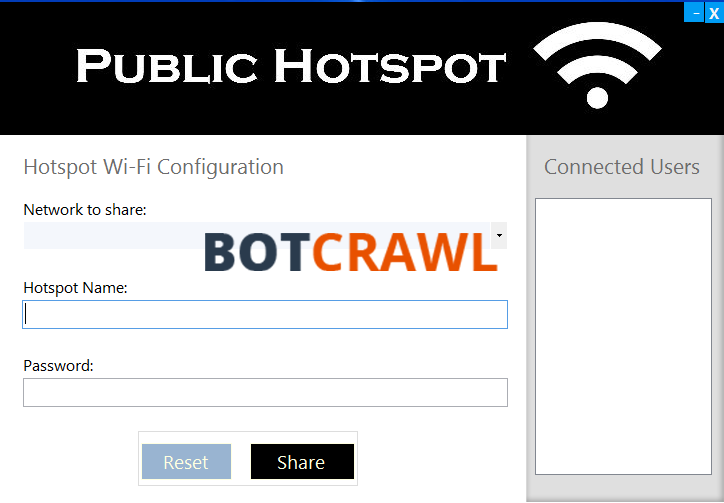
Public Hotspot (also referred to as Public Hotspot virus or PubHotspot) is a potentially unwanted program (PUP) that can cause issues for computer users once it has been installed. When Public Hotspot is first installed it will run a process named Public Hotspot (32bit), schedule a new task to run every time Windows starts, and display an icon on Windows Desktop. The program is also known to bundle with malware, adware, spyware, and other malicious threats. Public Hotspot and the programs that it usually bundles with will generate pop-up ads across multiple web browsers, change existing internet browser settings, and cause other very serious issues. Public Hotspot and other programs that it bundles with can also collect information from the computer that can be used to generate targeted advertisements that single out specific users.
Public Hotspot is primarily distributed by other free online programs that utilize deceptive marketing tactics in order to infiltrate computer systems. These programs will also bundle the adware with other threats that can be more serious and require immediate removal.
How to remove Public Hotspot virus, malware, and other threats |
Uninstall Public Hotspot
- Open Windows Start Menu and go to the Control Panel (or select Programs and Features).
- Click Uninstall a program (in earlier versions of Windows this is called Add and remove programs) in the Programs section in Windows Control Panel.
- Search for Public Hotspot and other unwanted programs in the list of programs installed on your computer. If you cannot find programs installed on your computer it is recommended to remove Public Hotspot with Malwarebytes and then perform a second opinion-scan with HitmanPro to remove remaining trace files.
- Double click the program you want to remove to begin the uninstall process.
| You might find these links useful: |
Remove unwanted browser attachments from your browsers
Chrome
- Click the Customize and control Google Chrome icon and go to More tools > Extensions.
- Click the trashcan icon next to the unwanted extension to remove it.
Firefox
- Open the Menu and click Add-ons.
- Click Remove next to the unwanted add-on you to remove it.
Safari
- Go to Safari > Preferences > Extensions.
- Click the Uninstall button next to the unwanted extension you to remove it.
Remove Public Hotspot virus with Malwarebytes
- Open your browser window and download Malwarebytes 3.0 Premium or Malwarebytes Anti-Malware Free. <<CLICK HERE TO BUY MALWAREBYTES 3.0>>
- Open the executable file (mb3-setup.exe) to begin installing Malwarebytes.
- Select your language, click Next, then select “I accept the agreement,” click the Next button several times, and then click the Install button to install Malwarebytes. Click Finish once the install process is complete.
- Open Malwarebytes and click the Scan Now button on the Dashboard to begin scanning your computer.
- Click the Quarantine Selected button once the scan is finished.
- If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
Perform a second opinion-scan with HitmanPro
- Open your browser window and download HitmanPro. <<CLICK HERE TO BUY HITMANPRO>>
- Open the executable file (hitmanpro_x64.exe or hitmanpro_x32.exe) to begin installing HitmanPro.
- Click the Next button, check “I accept the terms of the license agreement,” and click the Next button again.
- On the Setup page select “Yes, create a copy of HitmanPro so I can regularly scan this computer (recommended)” and add your email address to the registration fields to begin the free trial.
- Click Next to begin scanning your computer.
- Once the Scan results are displayed click the Next button and click the Next button again on the Removal results page.
Troubleshoot
- How to restore your computer
- How to recover your computer to factory settings
- How to protect your computer against future threats
How to restore your computer
If a restore point has previously been established on your machine you will be able to perform a system restore in order to restore your machine to a date and time before it was infected. You will lose files on your computer that were obtained prior to the restore point.
There are several options to restore your computer. Most computers have their own restore software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default restore program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
How to recover your computer to factory settings
A system recovery (or reset) will recover your computer to factory settings. You will lose the current programs and files on your computer.
There are several options to recover your computer to factory settings. Most computers have their own recovery software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default recovery program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
How to protect your computer against future threats
The key to staying protected against future infections is to take advantage of reputable Antivirus software and Antimalware software with real-time protection.
Security software like Malwarebytes 3.0 Premium and Vipre Antivirus have real-time features that can block malicious files before they spread across your computer. These programs bundled together can establish a wall between your computer and cyber criminals.
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
- METO Systems Named in Insomnia Ransomware Claim
- SANS Took Nearly $500K From ICE for Cyber Training
WordPress Bot Protection
Bot Blocker for WordPress
Detect bot traffic, monitor live activity, apply bot-aware rules, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress admin interface.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.