The Google lawsuit filed this week aims to dismantle a major Chinese phishing platform known as Lighthouse, a large scale phishing as a service system linked to widespread text scams across the United States and more than 120 countries. According to Google, Lighthouse has powered smishing operations that impersonate the United States Postal Service, DMV, E ZPass toll systems, and well known brands in order to steal personal information, financial data, and credit card numbers from millions of victims. The platform has been tied to attacks that Google estimates may have harvested anywhere from twelve million to more than one hundred million payment cards in the United States alone between 2023 and 2024.
Background of the Lighthouse Phishing Platform
Lighthouse is a commercial phishing as a service product sold to cybercriminals who want to conduct text based phishing campaigns without building their own infrastructure. The system provides its subscribers with ready made templates, hosting services, domain rotation, traffic filtering, data collection panels, and automated tools that help criminals launch high volume smishing operations. Threat actors can choose from templates that impersonate popular services including mail carriers, toll payment systems, major retailers, and technology brands.
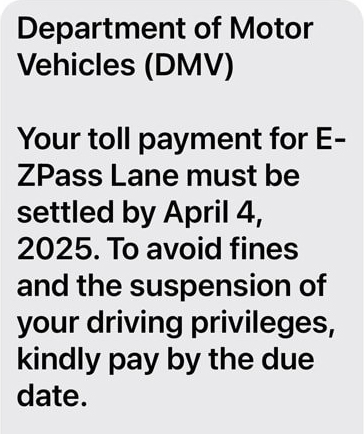
Researchers at Cisco Talos and other cybersecurity firms have identified Lighthouse as a kit developed by a Chinese threat actor known as Wang Duo Yu. This actor has operated Telegram channels that advertise Lighthouse subscriptions, provide technical support to buyers, and share updates about new features. Talos reports that Lighthouse drew attention in late 2024 when waves of toll themed phishing messages spread across the United States, using typosquatted domains that mimicked official E ZPass or regional toll agency billing portals. These messages typically claimed that recipients had unpaid toll charges, prompting them to click a link that redirected to a fake payment page designed to steal personal information and credit card numbers.
In addition to toll scams, Lighthouse supported phishing templates that impersonated USPS package delivery notifications. Victims received text messages claiming that shipments were delayed due to unpaid fees or incorrect delivery information. The links in these messages redirected to fraudulent USPS pages that harvested payment card numbers, home addresses, phone numbers, names, and email credentials. These attacks were especially damaging because the template designs closely resembled real USPS notices and took advantage of increased package deliveries during holiday seasons.
How Lighthouse Operates and Why It Has Been So Effective
Lighthouse is marketed as a turnkey phishing solution. Threat actors can subscribe on a weekly, monthly, or yearly basis, with prices reported by Netcraft ranging from eighty eight dollars per week to more than fifteen hundred dollars per year. Subscriptions grant access to a suite of tools that remove the technical barriers normally associated with phishing. This includes domain registration support, anti detection features, script obfuscation, customized login pages, and automated processing of stolen data.
One of the most significant capabilities offered by Lighthouse is cross platform messaging support. Criminals can send phishing links through iMessage on Apple devices and through Rich Communication Services on Android. These channels often bypass carrier filtering systems and reach victims directly. Many of the Lighthouse templates also mimic two factor authentication screens, allowing the platform to intercept one time verification codes in real time and grant attackers immediate access to compromised accounts.
Google revealed that Lighthouse included at least one hundred and seven website templates illegally using Google branding. Many of these pages replicated familiar sign in screens, allowing attackers to trick victims into entering account credentials and authentication codes. Because the templates used stolen branding assets, they were extremely convincing to the average user and often bypassed basic checks that users rely on to determine website legitimacy.
The Lighthouse system also maintained a large collection of typosquatted domains. Thousands of domains were registered to appear similar to toll payment systems, postal service portals, or financial services. The kit automatically rotated between domains to avoid shutdowns and reduce detection. These domains typically stayed online only long enough to harvest data before being replaced by new ones.
Details of the Google Lawsuit
The Google lawsuit seeks to dismantle Lighthouse by attacking the infrastructure that provides phishing capabilities to threat actors. Google is bringing claims under the Racketeer Influenced and Corrupt Organizations Act, the Lanham Act, and the Computer Fraud and Abuse Act. These statutes allow Google to pursue civil claims on the basis of fraud, trademark abuse, and intentional unauthorized exploitation of Google services.
According to Google, Lighthouse caused financial harm on an international scale. The lawsuit claims that Lighthouse directly impacted more than one million victims across at least one hundred and twenty countries. In the United States, the toll themed smishing campaigns contributed to the theft of millions of credit cards, placing enormous burdens on victims and financial institutions. Google argues that the legal action is necessary to protect consumers, prevent future fraud, and remove critical infrastructure that enables foreign based cybercrime.
Google’s legal approach focuses on removing access to domain registrars, hosting providers, payment processors, and other services that support Lighthouse operations. If successful, the lawsuit would allow Google to seize or disable the domains used in Lighthouse campaigns, block access to the platform’s backend systems, and prevent further distribution of the phishing templates that rely on Google’s branding.
Google’s Official Statement and Policy Response
Google published an official response outlining both the lawsuit and a broader strategy for combating international scams. The statement is available on Google’s public policy website at https://blog.google/outreach-initiatives/public-policy/legal-action-and-legislation-fight-scammers/. In this announcement, Google emphasized that Lighthouse represents a sophisticated global scam network that uses text messages about packages and toll charges to deceive victims.
Google explained that its objective is twofold. First, legal action will target the infrastructure behind Lighthouse and disrupt the platform directly. Second, Google is urging United States lawmakers to move forward with new policies that expand the ability of regulators and law enforcement to fight international fraud. Google voiced support for several bipartisan bills including:
- The GUARD Act, which empowers state and local authorities to investigate financial scams targeting retirees.
- The Foreign Robocall Elimination Act, which forms a task force to block overseas robocalls before they reach consumers.
- The SCAM Act, which creates a national strategy for identifying scam compounds and sanctioning criminal groups that operate them.
In addition to legal and policy measures, Google is upgrading its security tools to help detect scam messages and malicious links. Google Messages now uses artificial intelligence to flag potential scam texts and warn users before they click suspicious links. Google is also improving account recovery options through Recovery Contacts to help victims of account compromise regain control more easily. The company says it will continue investing in educational outreach to help users recognize common scam patterns, especially toll payment scams and package delivery scams that rely heavily on text messaging.
Evidence Linking Lighthouse to Chinese Threat Actors
The Lighthouse kit has been repeatedly connected to Chinese cybercriminals through independent research from Cisco Talos, Netcraft, and cybersecurity journalist Brian Krebs. Talos investigators identified that the platform was originally marketed under another name, Smishing Triad, before rebranding as Lighthouse in early 2025. The Smishing Triad group had already developed a reputation for large scale smishing attacks against telecommunications users in Asia and North America.
Talos reports that the main developer, Wang Duo Yu, uses Telegram channels to recruit customers and advertise premium features. Screenshots collected by researchers show that the Lighthouse operator promotes new templates, domain packages, and anti detection tools. Talos also found that Lighthouse uses the same fake shop templates seen in the Lucid phishing platform, suggesting a potential link between Chinese groups that share code, developers, or operational resources.
Netcraft analysis confirms that Lighthouse is part of a growing ecosystem of Chinese phishing as a service operations. These groups produce commercial kits that allow even inexperienced criminals to run large scale campaigns. Many of the related kits, including Darcula and Lucid, have been observed stealing financial information from victims in dozens of countries through SMS lures designed to mimic shipping companies, tax agencies, and toll providers.
Impact of the Lighthouse Scams on Victims
The toll themed smishing attacks associated with Lighthouse caused widespread financial losses. Victims typically received messages claiming that they owed a small toll fee or needed to update their payment information. These messages were crafted to appear urgent. Once the victim clicked the link, the fraudulent site requested personal information and credit card details. Attackers then used the stolen card information to conduct unauthorized purchases, commit identity theft, or sell the data on underground markets.
Many victims reported that the pages looked authentic due to the heavy use of real logos, matching color palettes, and realistic URLs. Some victims also noted that the phishing sites used HTTPS certificates, which gave the appearance of security to unsuspecting users. Because the toll fees were often small, victims did not question the requests and submitted their information quickly.
USPS themed scams were equally destructive. These messages claimed that packages were held due to incomplete shipping information or unpaid fees. With more people ordering goods online, especially during busy seasons, these messages successfully exploited trust in national mail carriers. Victims who paid the fraudulent fees also exposed their names, addresses, and credit card numbers to the attackers.
Why the Google Lawsuit Matters
The Google lawsuit is a significant escalation in efforts to combat phishing as a service networks. While many phishing operations rely on anonymous developers and hidden infrastructure, Lighthouse is notable for its size, organization, and global footprint. The platform industrialized phishing by providing a subscription based service that enabled criminals to operate with minimal expertise. By targeting Lighthouse directly, Google is attempting to disrupt not only the platform itself but also the broader ecosystem that makes large scale smishing viable.
If the lawsuit is successful, it could set a legal precedent for major technology companies to pursue civil actions against foreign based cybercriminal infrastructure. It may also encourage hosting providers, registrars, and payment services to take a more aggressive stance against phishing kits that rely on their systems.
Google’s case also highlights the importance of collaboration between private companies and policymakers. By endorsing new legislation aimed at combating foreign cybercrime, Google is acknowledging that legal action alone cannot address the growing threat of smishing and phishing as a service. A coordinated approach that includes law enforcement, regulators, and technology platforms is necessary to reduce the impact of these attacks on consumers.
For more updates on phishing operations, large scale smishing attacks, and other cybersecurity threats, visit the cybersecurity section on Botcrawl.
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
- METO Systems Named in Insomnia Ransomware Claim
WordPress Bot Protection
Bot Blocker for WordPress
Monitor bot traffic, review live activity, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress dashboard.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







