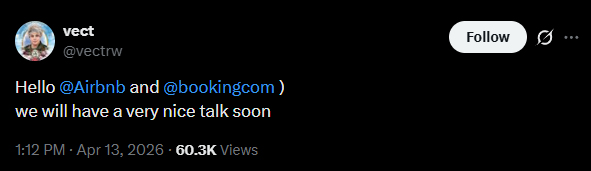
The Airbnb data breach story is still an alleged threat claim, not a confirmed breach disclosure. Airbnb was publicly named by the VECT extortion group in a short post that also referenced Booking.com, while the broader data breach environment in travel is already under pressure after Booking.com confirmed unauthorized access to some customer booking information. As of now, Airbnb has not publicly confirmed that its systems were breached or that Airbnb customer data was exposed.
That is the first point that needs to stay clear. There is no confirmed Airbnb breach at the time of writing. But the claim is not meaningless either. It arrived in the middle of a real travel-sector breach involving Booking.com, and that context matters. Once attackers publicly associate a second major travel platform with an ongoing booking-data incident, the risk expands beyond what either company has formally said. Users become easier to phish, hosts become easier to impersonate, and platform-branded fraud becomes easier to sell.
The Booking.com fallout is also part of why this Airbnb data breach claim is drawing closer scrutiny than an isolated post normally would. Booking.com eventually notified affected customers that unauthorized parties may have accessed booking details, names, email addresses, phone numbers, physical addresses, and information shared with accommodations. Before that public acknowledgment, warning signs and customer-facing concerns had already been circulating, and support exchanges reviewed by Botcrawl appeared to shift blame toward individual hotels rather than accept broader platform responsibility. That sequence does not prove Airbnb was breached, but it does show why silence from a travel platform should not be treated as definitive reassurance.
Background on the Airbnb Data Breach Claim
Airbnb is one of the largest trust-based travel and accommodation platforms in the world. Guests rely on it to book lodging, hosts depend on it to manage reservations and communications, and both sides expect the platform to handle time-sensitive messages, identity signals, and financial workflows in a way that feels safe enough to trust. That kind of platform naturally becomes attractive to extortion groups, fraud operators, and credential thieves because even a limited amount of reservation context can be turned into a very convincing scam.
The current Airbnb data breach concern stems from a public VECT post naming Airbnb alongside Booking.com. Standing alone, a short threat post would not be enough to say much more than that a ransomware or extortion actor is trying to create pressure. The problem is that it did not arrive in isolation. It landed at the same time that Booking.com was already dealing with a confirmed incident involving guest booking information. That makes the Airbnb reference more consequential because it suggests that at least one threat actor wants the market to think a second major travel brand may also be in play.
That still does not mean an Airbnb breach has been proven. It means the claim deserves disciplined attention. A platform can be mentioned falsely, strategically, prematurely, or accurately. Until Airbnb confirms otherwise, the claim should be treated as alleged. Until more facts emerge, it should also be treated as operationally significant.
Why the Booking.com Fallout Matters Here
The Airbnb data breach claim would be a smaller story if the Booking.com incident had been cleanly handled from the start. It was not. Booking.com eventually acknowledged unauthorized access to some customer booking information and said it contained the issue, updated reservation PINs, and informed affected users. But by the time that message reached customers, there had already been mounting signs that something was wrong in the booking ecosystem.
That matters because Booking.com’s public response looked narrower and later than the concern users were already experiencing. Support messaging that appeared to blame individual accommodations instead of recognizing wider platform exposure only made that gap more visible. Then, days later, customers received email notices acknowledging the breach and outlining the kinds of data that may have been accessed.
From an incident-response standpoint, that sequence has consequences. It weakens trust in the platform’s early messaging. It conditions users to believe that initial denials or partial explanations may later be overtaken by fuller disclosures. And it creates a more skeptical environment for any similar platform that is named by a threat actor but has not yet confirmed anything.
That is why the current Airbnb data breach story cannot be reduced to a simple yes-or-no question about whether Airbnb has made a statement. In travel-platform incidents, official silence or delay does not necessarily settle the matter. It may simply mean the company is still assessing the claim, limiting public exposure, or following the same cautious route another platform already took.
What Is Actually Known Right Now
The known facts are limited but still meaningful.
Airbnb has been publicly named by VECT. Booking.com, which was named in the same threat post, has separately confirmed unauthorized access to some customer booking information. Airbnb has not publicly confirmed a breach, a ransomware incident, or customer data exposure.
That means the Airbnb data breach narrative remains an alleged claim. There is no verified record count, no confirmed data inventory, and no public victim notice from Airbnb at this stage. There is also no responsible basis to claim that Airbnb payment data, guest messages, host accounts, identity records, or support systems were definitely exposed.
At the same time, it is not far-fetched to consider the possibility that Airbnb may have been affected and has not yet disclosed it. That is not a statement of fact. It is a reasonable threat assessment based on the surrounding circumstances. A known travel-platform breach is already active. A second major travel platform has now been publicly named by the same extortion actor. And the Booking.com example showed that a platform can move from narrow or disputed early messaging into broader customer notification later.
The line between analysis and assertion matters here. It is fair to say the threat is credible enough to watch closely. It is not fair to say Airbnb has definitely been breached unless and until that is confirmed.
Scope and Composition of the Potentially Exposed Data
Because Airbnb has not confirmed a breach, there is no verified list of exposed Airbnb data. Any precise claim about the exposed dataset would be speculation.
What can be assessed is the type of data that would matter most if an Airbnb intrusion did occur. In a platform like Airbnb, the sensitive categories would likely include names, email addresses, phone numbers, booking details, stay dates, listing information, internal messages between guests and hosts, support interactions, and profile-linked trust information used to validate accounts and transactions. None of those categories have been confirmed as exposed in connection with Airbnb. They matter because they show why a public threat claim involving a travel platform immediately raises fraud concerns.
Travel data is more dangerous than it looks on paper. It is not just personal information. It is situational information. It tells an attacker when someone is traveling, where they are going, what property they expect to access, how they have been communicating, and what kind of issue would sound believable enough to trigger an urgent response. A scam built around a real or realistic booking context can be far more effective than a generic phishing email.
That is one reason the Airbnb data breach claim matters even before confirmation. The likely abuse value of travel-platform data is high enough that a public threat alone can start the second wave of risk.
Risks to Guests, Hosts, and the Public
For guests, the most immediate risk is targeted phishing. A fake message about a payment verification, last-minute reservation issue, refund problem, arrival confirmation, or host communication can look routine in the context of a real trip. The attacker does not need to prove anything if the message feels plausible enough to act on.
For hosts, the risk includes guest impersonation, spoofed support interactions, fake payout or verification requests, and manipulation attempts tied to reservation disputes or urgent booking changes. Hosts often have to make decisions quickly, especially when a guest is arriving soon or claiming a time-sensitive problem. That speed works in the attacker’s favor.
For the public, the deeper issue is that trust in travel communications starts to degrade. Once people believe that booking platforms may be compromised, even legitimate messages become harder to trust. That creates friction for real support operations and opens more room for criminals to exploit uncertainty. Travel incidents are not just about the initial breach. They are also about what happens after customers begin questioning every message tied to a reservation.
Why It Is Not Unreasonable to Suspect More Than Has Been Said
The current Airbnb data breach claim does not justify certainty, but it does justify suspicion. That is a narrower and more defensible point.
Travel platforms have strong incentives to investigate quietly before making public statements. They may need to validate access, scope affected environments, coordinate internal response, review legal obligations, or avoid saying too much too early. None of that is unusual. But the Booking.com example showed how that process can look from the outside when users are already dealing with the consequences. If early messaging blames isolated partners or appears narrower than the underlying problem, trust erodes very quickly.
In that context, Airbnb’s silence does not end the story. It simply means the company has not confirmed anything yet. If Airbnb is following a similar path to Booking.com, it is possible that a fuller picture could emerge later. That possibility should be discussed carefully, not sensationally. It is a reasonable scenario, not a proven conclusion.
The strongest version of the point is this: given the VECT post, the live Booking.com breach, the known value of travel-platform data, and the way Booking.com’s response unfolded, it is not irrational to suspect that Airbnb may know more than has been publicly said. That remains an inference. It becomes a fact only if Airbnb confirms it or hard evidence emerges.
Possible Initial Access Vectors
Without a confirmed Airbnb incident, any technical explanation has to remain general. Travel and hospitality platforms are commonly pressured through stolen credentials, phishing, session theft, partner-side compromise, exposed administrative tools, support workflow abuse, or third-party access paths that expose too much booking context. These are not claims about Airbnb specifically. They are the types of access routes that repeatedly appear in platform intrusions and fraud operations tied to travel data.
The practical lesson is that a travel ecosystem often has more trust boundaries than users realize. The weak point may be a support system, a partner workflow, a reused credential, a linked service, or a message-routing function rather than a dramatic direct compromise of the main consumer-facing platform. That is why even limited exposure in the travel sector can have outsized consequences.
Mitigation Steps for Airbnb
If Airbnb is assessing the claim internally, the most useful immediate steps would include validating whether any unauthorized access occurred, reviewing booking and communication systems for unusual access patterns, auditing internal and third-party workflows that can reach reservation context, and monitoring for phishing or impersonation campaigns that exploit Airbnb branding or booking language.
The company should also be prepared to communicate clearly if more facts emerge. Travel-platform users need specificity. A narrow or overly careful statement may reduce legal exposure in the short term, but it can also increase downstream fraud risk if users are left unsure what kinds of messages or requests are safe. In this category of incident, clear user guidance is part of containment.
Recommended Actions for Hosts and Guests
Anyone using Airbnb right now should treat the situation as a reason for extra caution, not as proof that their data was breached.
Useful steps include:
- Be cautious with emails, texts, or messages that reference bookings, refunds, account verification, or urgent reservation problems
- Do not trust payment requests or account warnings just because they sound travel-related
- Verify reservation issues through the official Airbnb app or website instead of following links in messages
- Hosts should be careful with payout, identity, and booking-change requests that create urgency
- Guests should watch for fake host messages, fake support alerts, or fraudulent cancellation notices
- Change reused passwords and strengthen account security where possible
- If a device may have been exposed to malicious follow-up content, scan it with a trusted security tool such as Malwarebytes
The biggest danger may not be a direct platform compromise that has already been disclosed. It may be the wave of scams that follows the public claim, using Airbnb branding and travel urgency to pressure people into making mistakes.
The Airbnb data breach story is still unresolved. What is confirmed is that Booking.com suffered unauthorized access to customer booking information and that VECT has publicly named Airbnb alongside it. What is not confirmed is whether Airbnb itself was breached. Between those two points sits the real reason this story matters. Travel users are now operating in a threat environment where a major platform has already been hit, another has been named, and recent history shows that platform messaging may lag behind what users are experiencing. That does not prove Airbnb was compromised, but it is enough to justify scrutiny, caution, and the possibility that more may still come out.
For ongoing coverage of major data breaches and wider cybersecurity threats, the broader lesson is simple. In travel-platform breaches, context is often as dangerous as the data itself.
- Vodafone Data Breach Claim Follows LAPSUS$ Data Leak
- Udemy Data Breach Resurfaces as 1.4M Records Circulate on Forum
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Rheem Manufacturing Data Breach Claim Follows Reported INC Ransom Listing
- Polycorp Data Breach Exposes 400GB of Internal Manufacturing Data
WordPress Bot Protection
Bot Blocker for WordPress
Monitor bot traffic, review live activity, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress dashboard.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







