The Kurogane Kasei data breach has exposed confidential manufacturing, research, and corporate data following a ransomware attack carried out by the RansomHouse group. The Japanese chemical company, known for its work in organic synthesis and fine chemicals production, was listed on RansomHouse’s leak site with the status “disclosed,” confirming the publication of stolen files. The exposed materials include corporate financial records, chemical formulation data, and research project documentation from Kurogane Kasei Co., Ltd.
Background of the Kurogane Kasei Breach
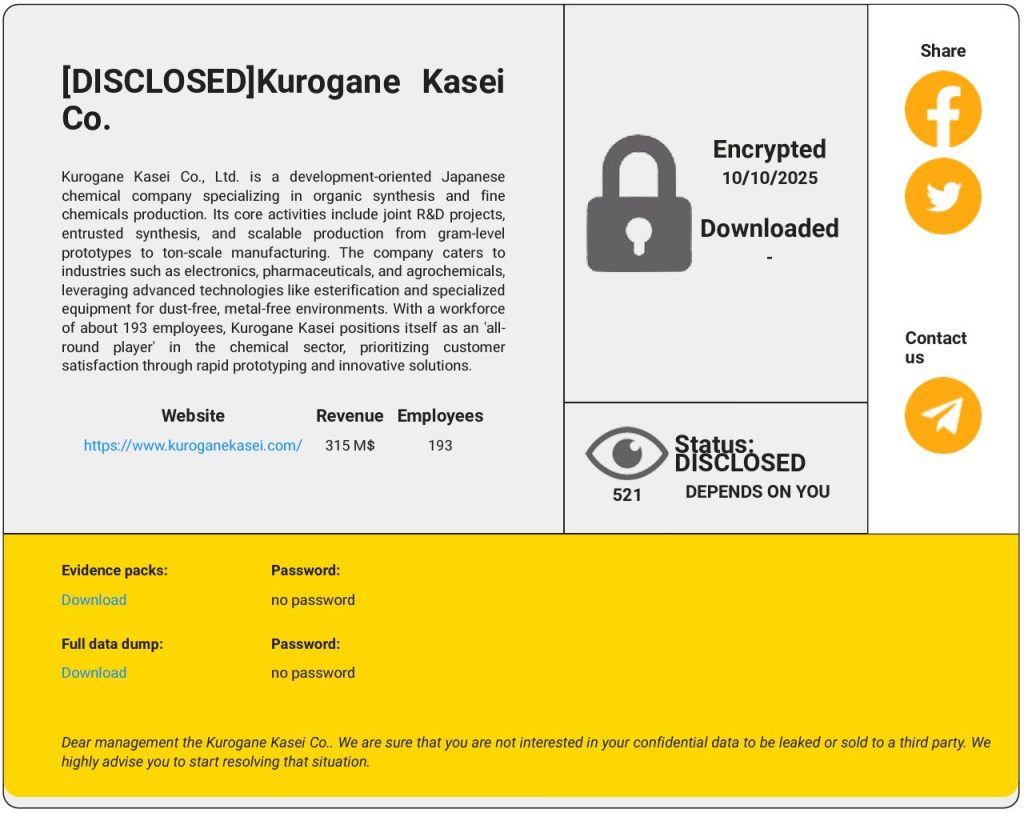
Kurogane Kasei Co., Ltd. is a development-oriented company specializing in chemical synthesis, entrusted R&D projects, and scalable manufacturing for the electronics, pharmaceutical, and agrochemical industries. With approximately 193 employees and reported revenue exceeding $315 million, the company plays a critical role in Japan’s industrial chemistry sector. On October 10, 2025, RansomHouse encrypted company systems, later listing the victim publicly with full data available for download. The data leak became fully disclosed on November 11, 2025.
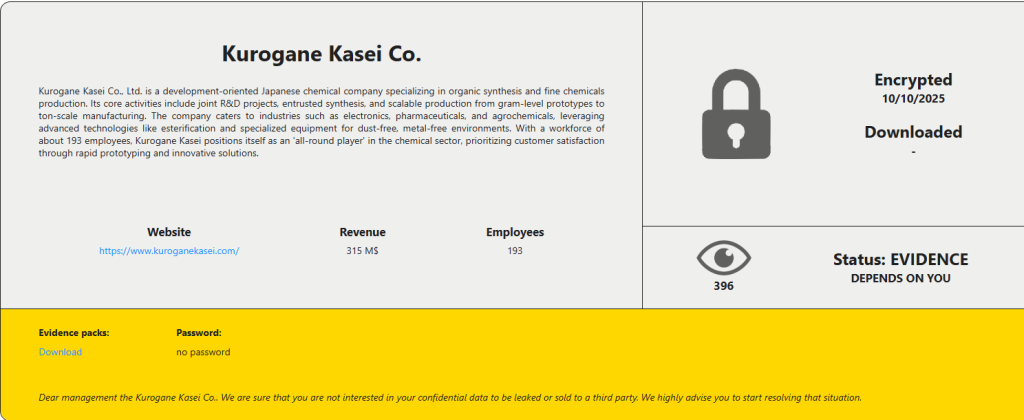
According to information shared on the group’s leak portal, the attack compromised proprietary research materials, employee communications, and internal financial data. The evidence packs and full data dumps were published without password protection, indicating that RansomHouse has released the stolen files openly on the web. This tactic is often used to pressure victims into payment and to publicly demonstrate data exfiltration capabilities.
About the RansomHouse Ransomware Group
RansomHouse is a data extortion group known for targeting industrial and manufacturing companies worldwide. Unlike traditional ransomware operators, RansomHouse often claims to act as a “data broker” rather than a malware distributor, focusing on stealing information and demanding ransom for non-disclosure. The group’s leak portal includes victims across multiple sectors, including healthcare, energy, and finance.
RansomHouse typically gains access through compromised network credentials, unpatched systems, or exposed remote desktop services. Once access is achieved, attackers exfiltrate large amounts of data, leaving behind encryption payloads or ransom notes demanding payment in cryptocurrency. The group’s distinctive practice of publishing entire data sets without encryption, as seen in the Kurogane Kasei case, increases reputational damage and regulatory risks for its victims.
Scope of the Data Breach
Files released from the Kurogane Kasei ransomware incident reportedly include a wide range of sensitive business and technical data. Cybersecurity researchers who reviewed samples found:
- Internal corporate communications and contracts with suppliers
- Research data related to chemical synthesis and esterification processes
- Financial reports and profit statements
- Employee information, including contact details and HR documents
- Technical equipment and production environment schematics
The release of scientific and industrial data poses serious risks to Kurogane Kasei’s intellectual property portfolio. The exposure of chemical formulas, manufacturing methods, and proprietary processes could enable industrial espionage or competitive exploitation. The incident also threatens to undermine client trust in industries such as electronics and pharmaceuticals, where data confidentiality is essential.
Impact on the Manufacturing and Chemical Industry
The Kurogane Kasei breach underscores the vulnerability of chemical manufacturing companies to ransomware and data exfiltration campaigns. Industrial organizations often operate legacy systems and complex production networks that are difficult to secure. Once infiltrated, these environments offer attackers high-value data that can be monetized or weaponized. The exposure of proprietary formulas or production designs can cause long-term financial harm by eroding competitive advantages and damaging client relationships.
This attack also highlights growing targeting of Japan’s advanced manufacturing sector by organized cybercrime groups. Companies involved in high-value R&D and export activities have become attractive targets due to the dual potential for financial ransom and access to industrial knowledge. The breach at Kurogane Kasei follows a pattern of attacks on chemical and materials companies that began escalating in 2024 and continued into 2025.
Technical Analysis and Attack Vector
RansomHouse is believed to have gained access to Kurogane Kasei’s network through weak credentials or exploitation of unpatched services exposed to the internet. Once access was obtained, attackers likely moved laterally across the company’s network, exfiltrating data before deploying encryption tools. The presence of open evidence and data dumps suggests that the group completed the exfiltration phase successfully and chose to publish the data rather than negotiate.
The group’s dark web listing included indicators such as full public download links, encrypted system notices, and a message directed at company management urging them to “start resolving the situation.” This type of communication is consistent with RansomHouse’s extortion strategy, which relies on public exposure and reputational damage to force compliance.
Relation to Other Global Attacks
The Kurogane Kasei ransomware breach aligns with a series of attacks observed across global manufacturing and industrial sectors in 2025. Groups such as RansomHouse, CL0P, and BlackSuit have increasingly targeted firms involved in supply chain production and R&D. Like the Knownsec data breach, this incident highlights the growing convergence between cybercrime and industrial espionage. The theft and publication of sensitive data from scientific and engineering firms have become a critical concern for both private enterprises and national security agencies.
Mitigation Strategies and Immediate Actions
For Kurogane Kasei and Manufacturing Firms
- Immediately isolate compromised systems to prevent further data leakage or unauthorized access.
- Engage digital forensics specialists to determine the entry point, exfiltration timeline, and affected data scope.
- Revoke and reset all employee credentials, VPN tokens, and administrative keys used in the compromised systems.
- Audit cloud services, backup systems, and supplier connections for potential secondary compromise.
- Inform affected partners and clients and comply with national reporting requirements under Japan’s cybersecurity and data protection laws.
- Rebuild compromised systems using clean backups and ensure that encryption or backdoor payloads are fully removed.
For Employees and Industry Partners
- Change passwords associated with corporate or project-related accounts.
- Be cautious of phishing attempts referencing leaked Kurogane Kasei information.
- Monitor financial transactions and company communications for signs of impersonation or social engineering attacks.
- Run a full malware and spyware scan using reliable software such as Malwarebytes to detect unauthorized monitoring or infection attempts.
Preventive Security Recommendations for the Chemical Sector
The Kurogane Kasei ransomware incident demonstrates the need for chemical and manufacturing firms to adopt stronger cybersecurity measures. Regular patching of industrial control systems, enforcing network segmentation, and implementing endpoint detection tools can significantly reduce attack surfaces. Organizations should also deploy intrusion detection systems that monitor traffic between corporate and production environments to identify lateral movement early.
Proactive employee education and mandatory two-factor authentication are essential defenses against credential theft, one of the leading causes of ransomware intrusions. Companies handling sensitive industrial or R&D data should conduct annual security audits and establish strict access control frameworks to ensure that confidential research is accessible only to authorized personnel.
Data Breach Summary
- Company: Kurogane Kasei Co., Ltd.
- Industry: Manufacturing and Chemical Production
- Location: Japan
- Threat Actor: RansomHouse
- Attack Type: Ransomware and data exfiltration
- Data Exposed: Financial data, research materials, employee records, and production documents
- Status: Data disclosed publicly on RansomHouse leak portal
The Kurogane Kasei data breach marks a major escalation in ransomware operations targeting Japan’s industrial and chemical sectors. The exposure of proprietary research and corporate data poses serious economic and security risks, emphasizing the need for reinforced digital protection measures and rapid incident response capabilities across the industry.
For verified coverage of major data breaches and the latest cybersecurity threats, visit Botcrawl for ongoing updates and expert analysis on global digital security events.
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Rheem Manufacturing Data Breach Claim Follows Reported INC Ransom Listing
- Polycorp Data Breach Exposes 400GB of Internal Manufacturing Data
- Uniview Technologies Data Breach Claimed by The Gentlemen Ransomware Group
- Archdiocese of St. John’s Data Breach Claim Follows Reported Qilin Listing
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







