A researcher known as Impulsive says ClickUp exposed customer emails, internal feature flags, and sensitive configuration data through a public-facing setup anyone could reach from the company’s own website. The claim started with a Split SDK token in ClickUp’s production JavaScript bundle, but the token itself is not the whole story. Client-side SDK keys can exist in browser code. The ugly part is what the researcher says came back from the request: 959 email addresses, 3,165 internal feature flags, customer rollout rules, billing experiments, AI pricing tiers, infrastructure routing, and other internal configuration data.
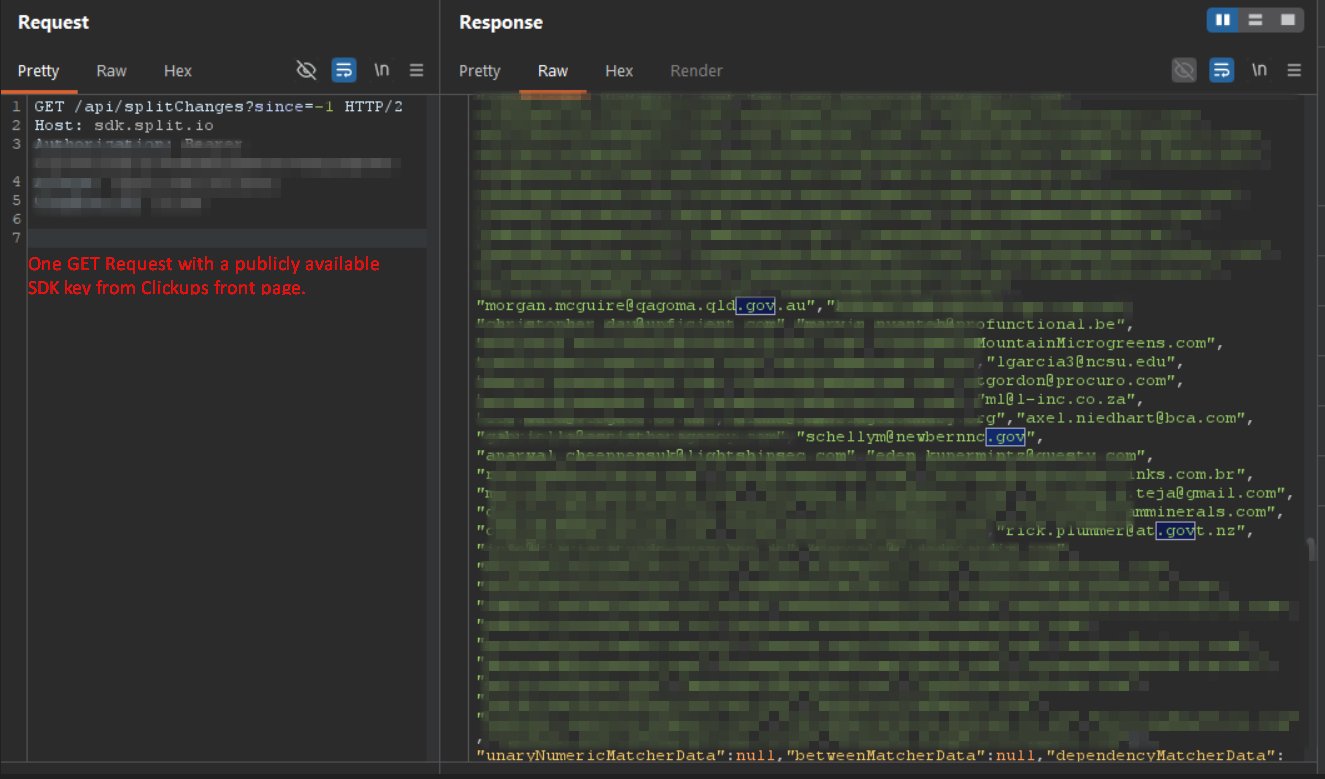
i went to https://t.co/GYtMjd81a6. opened the page source. found a hardcoded API key in the javascript. copied it. sent one GET request.
got back 959 email addresses and 3,165 internal feature flags.
employees from Home Depot. Fortinet. Autodesk. Tenable. Rakuten. Mayo Clinic.… pic.twitter.com/C0ss5T6at1
— impulsive (@weezerOSINT) April 27, 2026
If that is accurate, this is not just another exposed key screenshot. It is another AI-workspace company asking customers for trust while acting like security can be cleaned up later.
ClickUp is not some tiny weekend startup. It raised hundreds of millions of dollars, reached a $4 billion valuation, and sells itself as the place where serious companies can manage work, documents, projects, automations, and now AI-powered workflows. That matters because the more a company wants to become the center of someone’s work, the less room it has to be careless with the data sitting around that work.
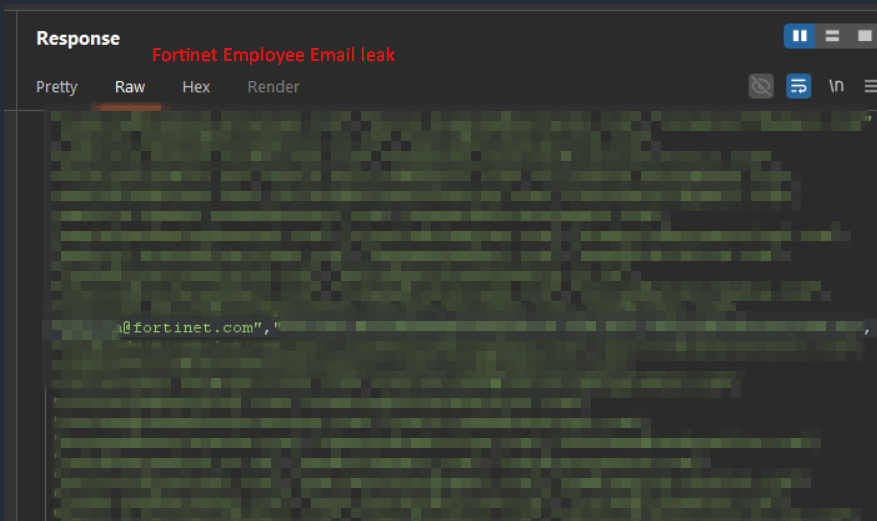
The screenshots attached to the researcher’s post appear to show blurred response data with visible customer domains, including Fortinet and Home Depot, and the thread claims the exposed emails included employees from companies such as Autodesk, Tenable, Rakuten, Mayo Clinic, government offices, and ClickUp itself. The same researcher claims one feature flag previously contained a live ClickUp API token tied to Fairfax County Public Schools, though that specific token was reportedly removed after disclosure. ClickUp still needs to answer the larger question: why was customer-identifying data and internal rollout logic sitting in a response reachable through public frontend code?
Feature flags are supposed to help companies ship carefully. They are not supposed to become a public window into customer targeting, AI pricing tests, churn prevention offers, internal experiments, rate limiter whitelists, or security-related notes. If a company stores sensitive business logic or customer emails inside client-readable flag rules, the feature flag system becomes part of the exposure.
The second claim is even more serious if it checks out. The researcher says ClickUp’s webhook API allowed server-side request forgery through a free account, meaning a user could configure a webhook in a way that made ClickUp’s own systems request internal resources. ClickUp’s developer docs describe webhooks as event subscriptions that send requests to a destination URL, which is exactly the kind of feature that needs strict URL validation and internal network protections. A webhook product with weak SSRF protection is not a small paper cut. It can become a map of the company’s internal infrastructure.
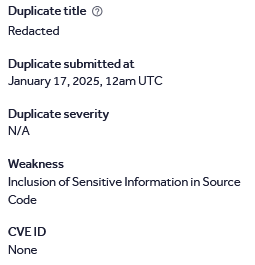
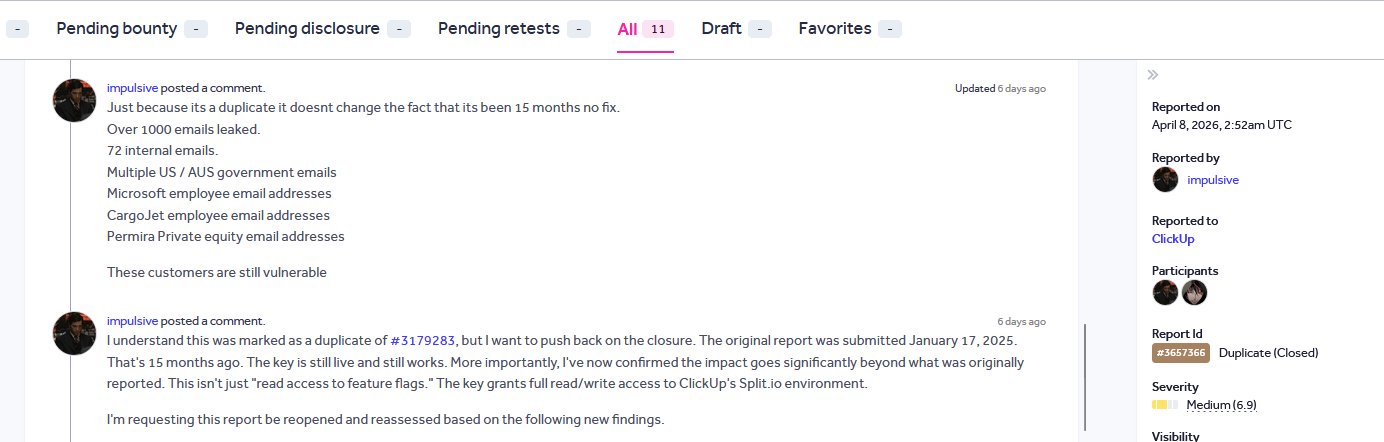
The timeline makes it worse. The researcher says the Split-related issue was first reported through HackerOne in January 2025, marked as a duplicate, and still remained exposed in April 2026. They also claim the webhook SSRF report sat unanswered for 19 days. ClickUp’s own feedback page says its bug bounty program is no longer active, which only makes the whole setup look more hollow. A vulnerability intake form is not a security program if confirmed issues can sit for more than a year while customer data remains exposed.
This is the same pattern that keeps showing up around AI tool companies. Lovable wanted users to trust it with source code, prompts, database credentials, customer records, and live project data, then tried to shrink a security mess into a wording problem after screenshots started spreading. ClickUp wants to be the AI workspace where companies pour projects, docs, automations, customers, workflows, and internal operations into one place. The ask is massive. The care has to match it.
Too many of these companies are built around capital first and consequences later. They talk like enterprise platforms, raise money like enterprise platforms, and sell trust like enterprise platforms, but when security researchers point to exposed data or broken controls, the response often looks slow, legalistic, or nonexistent. That is not how serious companies behave. That is how growth machines behave when security is treated as a cost center instead of the product’s foundation.
ClickUp needs to explain what was exposed, when it first knew, whether the key was rotated, whether any customer data was accessed by anyone outside the researcher’s report, whether a live API token was ever present in feature flag data, and whether the claimed webhook SSRF issue was reproduced or fixed. If the researcher is wrong, ClickUp should say so with specifics. If the researcher is right, this belongs in the same bucket as every other AI-workspace trust failure people are getting tired of seeing.
Companies like this want to be the operating system for work. They want the docs, the tasks, the automations, the customer data, the internal plans, the AI prompts, and the business logic. Fine. Then they do not get to behave like safety is a cleanup step after someone posts screenshots.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







