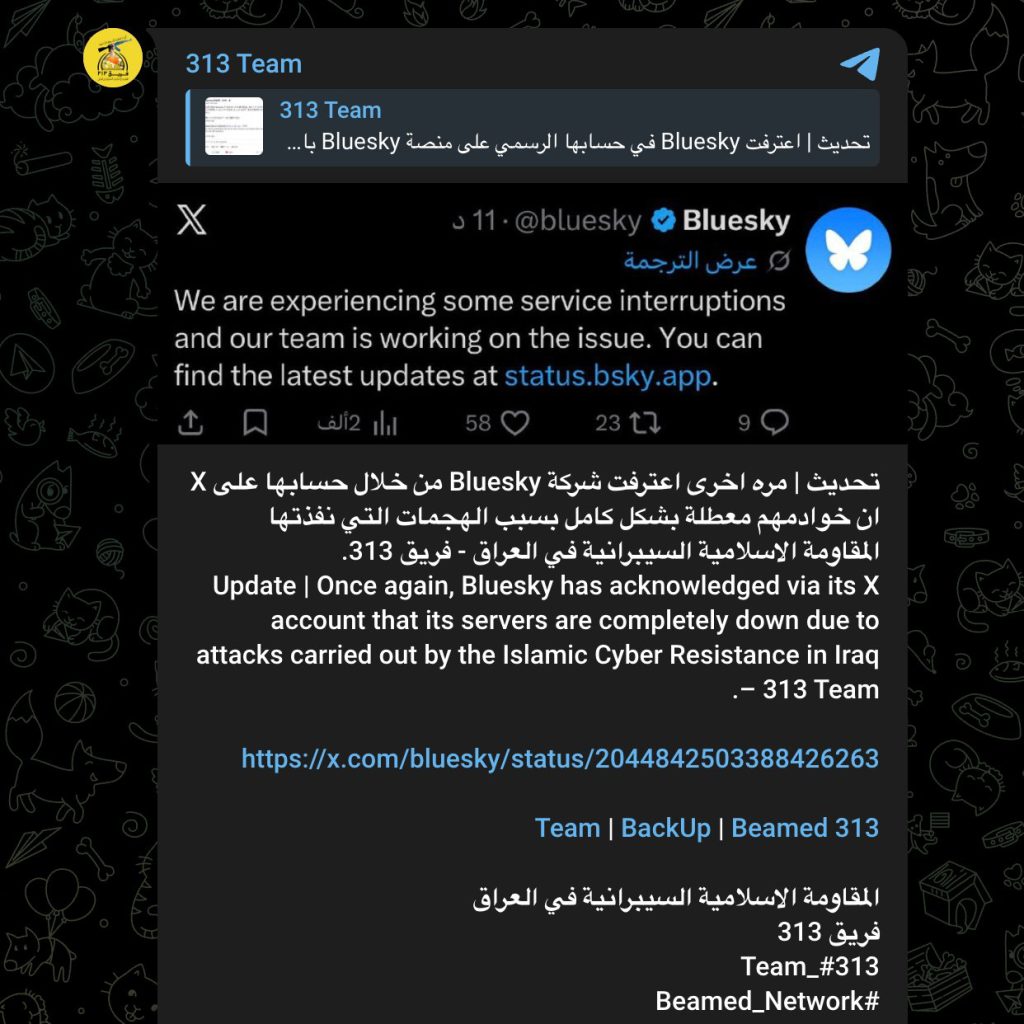
Bluesky, the social media app that started under Twitter founder Jack Dorsey, was allegedly attacked today by 313 Team. Bluesky first confirmed service interruptions, then later said it had been dealing with a sophisticated Distributed Denial-of-Service attack that started late on April 15 and intensified throughout the next day. The company has not publicly said 313 Team was behind it, but the group took responsibility quickly, and in situations like this threat actors are often more direct than the companies being hit.
I decided to look into this and, to be honest, I had never used Bluesky before or even been to their website. So I put myself on a side quest and made a new account for Botcrawl at botcrawl.bsky.social. After actually going through the process and using it for the first time, my first impression was simple. It is basically just a minimalistic Twitter.
That is not automatically a bad thing. In some ways it looks cleaner than X. It feels lighter, less noisy, and easier on the eyes. But it also feels much thinner. It still comes across more like a stripped-down Twitter skeleton than a platform that has fully grown into its own weight. X, for all the things people like to complain about, is still more complete, more battle-tested, and more poised for success today.
Upon further investigation, this may not be the most important thing in the world, but I also noticed that part of Bluesky’s support appears to be powered by Zendesk. Now, to be fair, that is still better support than platforms like YouTube, which will literally make people publicly post at them on X in front of everybody just to maybe get some kind of robotic response that never actually helps. But Zendesk still leaves a weird taste in my mouth. The company seems completely obsessed with AI agents and removing human interaction from support, and that direction usually makes support worse, not better.
None of that may be the central issue here, but to me it says a lot about where Bluesky still is as a product. The platform has been around since 2019, and I, a tech author who writes about internet and cybersecurity issues all the time, had never even been to the site until now. Maybe for some people that is part of the appeal. Less noise. Less baggage. Maybe even more privacy. But it also says Bluesky still has a long way to go if it wants to become the kind of product people naturally think to use.
But none of that stops threat actors from attacking it.
Bluesky’s own messaging gives a pretty clear sequence of what happened. First, the company told users it was experiencing service interruptions and pointed them to its status page. Later, it got much more specific and said its team had received reports of intermittent app outages at about 11:40 p.m. PDT on April 15 and worked through the night to mitigate what it described as a sophisticated DDoS attack that intensified throughout the day. Bluesky also said the disruption was affecting feeds, notifications, threads, and search. That lines up with what users were seeing while the platform was struggling.
The company also said it had not seen any evidence of unauthorized access to private user data. That part matters because it helps separate this from the kind of incident people usually imagine when they hear the word attack. So far, this looks like an availability hit, not a public data theft story. In other words, the platform was being hit hard enough to cause real service problems, but not, at least based on what Bluesky itself has said, a deeper compromise involving private user data.
Some people like to act as if DDoS is not serious because it is “just downtime,” but that is easy to say when it is not your platform getting knocked around in public. Reliability is part of the product. If users cannot refresh their feed, cannot load notifications, cannot use search, and start seeing weird errors or forbidden messages, that becomes the user experience. For a platform still trying to establish itself as a serious alternative to X, that matters a lot.
The 313 Team part of the story is also pretty straightforward. Bluesky confirmed the outage. Bluesky later confirmed the DDoS attack. 313 Team then took responsibility for it. So the clean reading is not that Bluesky officially named the group, because it did not. The clean reading is that Bluesky confirmed the incident and 313 Team publicly claimed credit for it. That is still meaningful, especially when the group moved fast and clearly wanted everyone to know it was them.
I also think the target choice is interesting. On first glance, Bluesky does not feel like the biggest or most obvious social platform in the world to go after. It still feels smaller, cleaner, and much more bare than X. But threat actors do not always pick targets based on what outside observers think makes perfect sense. Sometimes the target is chosen because it is visible enough, vulnerable enough, or simply useful enough for the kind of attention they want. Sometimes being a rising platform is enough.
After checking Bluesky for myself, creating botcrawl.bsky.social, and seeing how the platform actually feels firsthand, my impression is pretty simple. Bluesky looks better than a lot of people probably expect, but it still feels much thinner than X, and today did not help that impression. The outage was real. Bluesky confirmed a DDoS attack. 313 Team claimed responsibility. The platform later returned to operational status, but this is still the kind of incident that exposes how much work a platform has left if it wants to be seen as more than a cleaner, lighter Twitter alternative.
That may sound harsh, but I do not think it is unfair. If Bluesky wants people to treat it like a serious destination and not just a side road away from X, then it has to feel complete, it has to feel stable, and it has to be able to take a hit without falling apart in front of everybody. Today was a reminder that even a platform that looks cleaner, smaller, and more privacy-friendly on the surface still has to survive the same hostile internet as everyone else.
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
- METO Systems Named in Insomnia Ransomware Claim
WordPress Bot Protection
Bot Blocker for WordPress
Monitor bot traffic, review live activity, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress dashboard.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







