With little surprise, Kash Patel, the sitting director of the FBI, is facing one of the most embarrassing personal cybersecurity scandals involving a senior U.S. official in years after Iran-linked hackers reportedly breached his personal Gmail and leaked private files online.

A group known as Handala claimed responsibility for the attack and began sharing material that appeared to come from Patel’s personal Gmail account, including private photos, a resume, and a sample of more than 300 emails, many which were shared on X as it was a trending topic. The FBI said the exposed material was historical in nature and did not include government information.
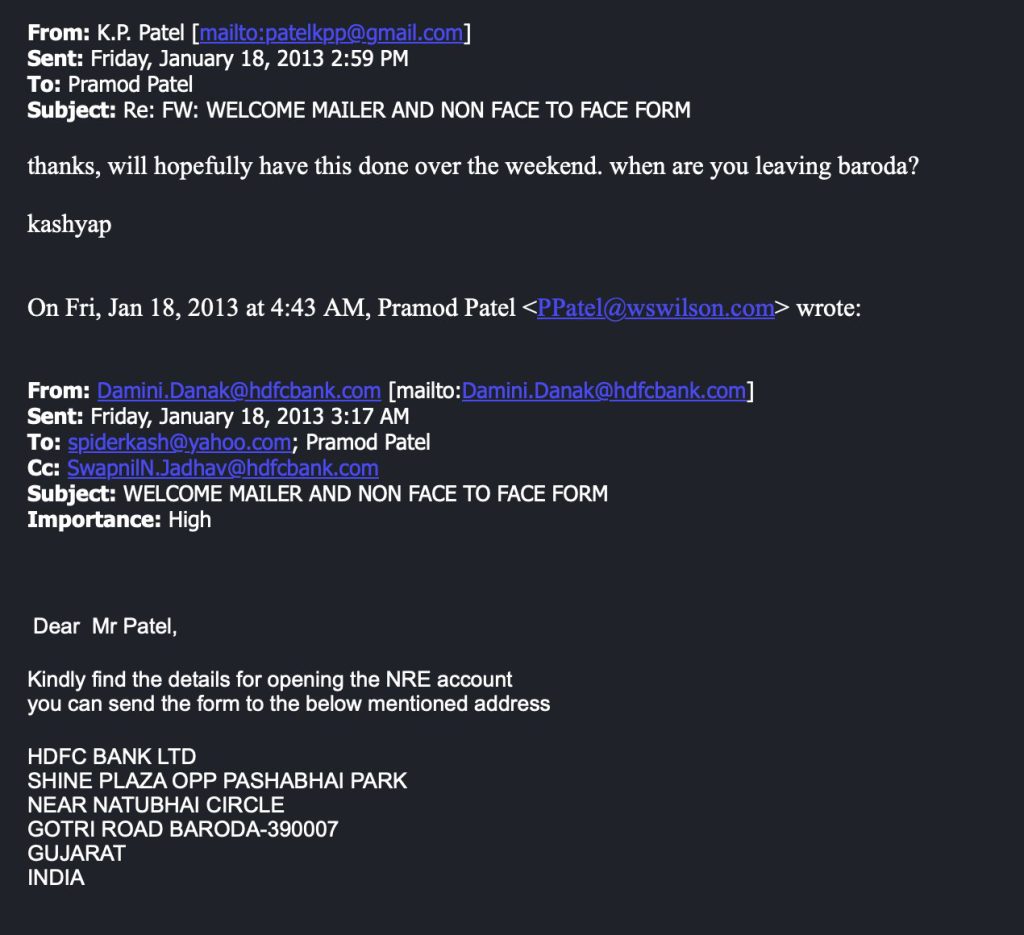
One notable detail from the leaked material is an email chain suggesting Patel had an NRE bank account in India. That is the kind of detail that immediately draws attention once it surfaces online, especially when it involves the sitting director of the FBI. On its own, though, it does not establish wrongdoing. An NRE account is a banking product used by non-resident Indians and people with family or financial ties to India, so its existence may be routine depending on the person’s background and circumstances. What makes it newsworthy here is not that it proves a scandal by itself, but that it adds to the broader picture of how personal and far-reaching the leak appears to be.

The broader issue is that the active director of the FBI had his personal email account hacked and parts of that account exposed in public. For a man whose fitness for the job has already drawn criticism from opponents, this is another strain on his short tenure as director and another bad look for the bureau under his leadership. And now, as the leak spreads, the public is left watching him practically deep-throat cigars and pose for silly mirror selfies.
That point limits the national security scope of the incident, but it does not make the story any less damaging. Patel is not a former aide, campaign staffer, or lower-level official whose old inbox suddenly resurfaced online. He is the current director of the FBI. Once personal images, emails, and documents tied to him began circulating in public, the breach became a serious embarrassment for the man now leading the bureau.
The material appears to have been chosen for exactly that effect. Reuters reported that the leaked photos showed Patel smoking cigars, riding in an antique convertible, and posing in a mirror with a large bottle of rum. AP reported that the files also included a resume and older records tied to travel and business matters. None of that amounts to a policy scandal on its own, but that was never the real point of the leak. The point was exposure.
That is why the story spread so quickly. The breach was personal, visual, and easy for people to understand. It did not require a reader to work through technical jargon or classified-sounding claims. Private material from the FBI director’s personal Gmail was posted online, and some of it was embarrassing enough to take on a life of its own almost immediately.
The reaction was predictable. Critics of Patel seized on the breach as a humiliation story first and a cyber story second. Supporters and allies tried to narrow the scope by pointing to the FBI’s statement that no government information was involved. That split reaction is part of what made the incident travel so fast. People who already disliked Patel saw it as another sign that he is unfit for the role, while others framed it as an attack meant to damage a sitting U.S. official rather than expose a deeper official scandal.
The email cache appears to be years old. Reuters reported that the sample of leaked emails dated from roughly 2010 to 2019. AP said many of the documents related to Patel’s past travel and business dealings. That timeline lines up with the FBI’s statement that the exposed material was historical and did not involve government information.
Even so, the fact that the files were old did not protect Patel from the fallout. In some ways, it made the leak easier to turn into a spectacle. The material was personal enough to feel invasive, but familiar enough to be recognizable and believable. For a public audience, that is often more than enough.
There is also reason to believe at least part of the leak is authentic. Reuters reported that a Justice Department official said the material appeared to be real. TechCrunch said it verified some of the leaked emails by examining message headers. Reuters also reported that the Gmail address claimed by Handala matched an address tied to Patel in older breach data preserved by District 4 Labs. That does not prove that every file circulating online is genuine, but it does make the core breach claim much harder to dismiss.
What remains unclear is how the account was compromised in the first place. Public reporting has not established whether Patel was hit by phishing, password reuse, credential stuffing, or some older compromise that later turned into a public leak. There is also no public evidence so far that FBI systems were breached or that classified bureau material was stolen.
That distinction matters. The public facts currently point to a compromise of Patel’s personal Gmail, not a confirmed break-in to FBI infrastructure. But for the head of the FBI, even that narrower version of the story is damaging enough. A personal account breach would be bad for any senior official. For the director of the bureau, it becomes a major public and institutional embarrassment.
The timing only added to the impact. On March 19, the Justice Department announced the seizure of four domains it said were tied to Iranian cyber-enabled psychological operations. DOJ said that Handala-linked infrastructure had been used to claim hacks, publish stolen data, and threaten targets. Days later, material from Patel’s personal Gmail was circulating online. That sequence does not by itself prove motive, but it places the breach inside a wider public fight over Iranian cyber activity.
AP also reported that Patel had been informed before becoming FBI director that he had been targeted in an Iranian cyberattack dating back to late 2024. If that timeline is accurate, the public leak may not mark the beginning of the compromise. It may simply be the moment the breach became public enough to inflict maximum damage.
That wider context matters because Handala has not been treated by U.S. officials and researchers as some random internet nuisance. Reuters and Axios both noted that the group has been viewed by analysts and officials as part of a broader Iran-linked cyber pressure campaign. In that light, Patel’s personal Gmail was not just a convenient target. It was a high-value symbolic target. The sitting FBI director being turned into the subject of a public leak is the kind of outcome meant to embarrass both the individual and the institution he leads.
That is what makes this incident stand out. The most important question is not whether the leaked photos were personally awkward or politically useful on their own. It is that the current FBI director appears to have been turned into the target of a public hack-and-leak campaign built around his private Gmail account.
For now, the known facts are straightforward. Kash Patel’s personal Gmail was reportedly breached by a group described in public reporting as Iran-linked or pro-Iranian. Personal photos, emails, and other files were leaked online. The FBI says the material was old and non-governmental. Some of the emails appear to be authentic. The method of intrusion is still unclear.
That leaves a story that is narrower than the wildest claims online, but still serious on its own terms. The head of the FBI had personal material taken from a private account and dumped into public view. Classified files were not required. A confirmed breach of FBI systems was not required. The private leak was enough to create a very public humiliation.
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
- METO Systems Named in Insomnia Ransomware Claim
- SANS Took Nearly $500K From ICE for Cyber Training
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.