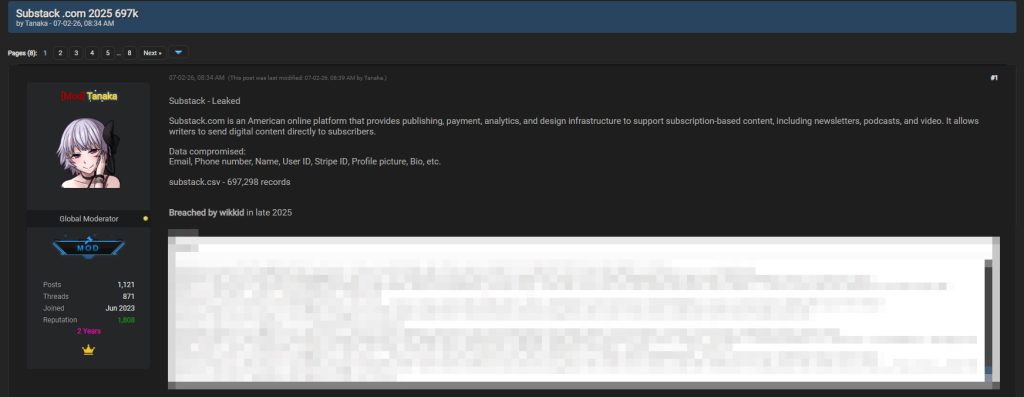
On February 7, 2026, a forum listing titled “Substack .com 2025 697k” appeared online, marking the first known public circulation of what is being described as a Substack leak involving 697,298 user records. The post advertises a CSV file named substack.csv and claims it contains account data originally obtained during a 2025 data breach.
The listing does not present the incident as a new intrusion. Instead, it frames the dataset as material taken in late 2025 and now redistributed in 2026. What makes this development significant is not the breach itself, but the public release and circulation of the alleged database nearly a year later.
What the Forum Listing Claims
According to the post, the exposed dataset contains 697,298 records tied to Substack users. A sample of rows is included directly in the listing, showing structured account information consistent with a backend export.
The fields displayed in the sample include:
- Name
- Email address
- Email confirmation status
- Phone number
- User ID
- Stripe platform customer ID
- Profile photo URL
- Bio
- Account creation and update timestamps
- Handle and previous username
- Session version and moderation flags
Several sample entries show full email addresses and international phone numbers. In some cases, Stripe-related identifiers appear in the stripe_platform_customer_id field, suggesting that payment-linked metadata may be part of the export. There is no indication in the listing that raw payment card numbers are included, but the presence of Stripe customer IDs raises concerns about potential account correlation risks.
Relationship to the 2025 Breach
The post explicitly states that the data was “Breached by wikkid in late 2025.” That phrasing implies the dataset originates from a prior security incident rather than a newly discovered vulnerability. The breach is referenced as having occurred in 2025, while the public distribution of the file took place in February 2026.
This distinction matters. A breach refers to unauthorized access to data. A leak refers to the exposure or redistribution of that data. In this case, the Substack leak appears to represent the second stage: circulation of data allegedly taken during an earlier compromise.
At the time of publication, there has been no public confirmation regarding the authenticity of the 697,298-record file. However, the structured format of the sample rows, along with consistent timestamp formatting and internal identifiers, suggests the dataset was exported from a production system rather than manually assembled.
What the Exposed Fields Reveal
Even without passwords listed in the visible sample, the exposed data carries risk. Email addresses paired with names and phone numbers significantly increase phishing precision. Account creation dates and activity timestamps allow attackers to profile user behavior. Stripe-linked identifiers may enable targeted social engineering attempts aimed at payment disputes or subscription fraud.
Some entries also show bio text and profile image URLs, meaning publicly visible identity information is bundled alongside private contact details. When aggregated in a single CSV file, that data becomes more valuable to threat actors than when stored separately.
For writers and publishers who rely on Substack as a business platform, exposure of Stripe customer identifiers and contact details could increase the risk of impersonation campaigns. Attackers often use breached data to craft convincing emails referencing subscription activity or payment verification issues.
Scale and Potential Impact
The listing claims 697,298 records. If accurate, that figure places the Substack leak among the larger user database exposures in the publishing and newsletter sector. Substack supports independent writers, media professionals, entrepreneurs, and niche community publishers worldwide. A dataset of this size likely spans multiple countries.
The presence of international phone numbers in the sample indicates global user exposure. That broad geographic scope complicates regulatory implications, particularly where data protection laws such as GDPR may apply.
Even if much of the information was partially visible through public profiles, consolidation into a downloadable CSV dramatically changes the risk profile. Data aggregation reduces friction for misuse. Instead of scraping individual pages, an attacker can search, sort, and filter nearly 700,000 accounts instantly.
Authenticity and Verification Questions
The listing includes sample rows but restricts full access behind registration. This is typical for forum-based database postings. While the structure appears consistent, independent verification would require validation against confirmed Substack accounts or internal data schemas.
Until official confirmation is issued, the file should be treated as an alleged dataset. However, historical patterns show that delayed leaks of previously breached databases are common. Data is often held privately before being traded or publicly released months later.
Security Risks for Affected Users
Users whose information appears in the Substack leak face several immediate risks:
- Targeted phishing emails referencing newsletter subscriptions
- SMS phishing attempts using exposed phone numbers
- Account takeover attempts through credential stuffing
- Payment-related impersonation scams involving Stripe-linked identifiers
- Identity correlation across multiple breached datasets
If a user reused a password on Substack and another service, credential stuffing becomes a realistic concern. Even without passwords in the visible sample, attackers frequently combine separate breached datasets to escalate access.
Mitigation Steps
If you have a Substack account, especially one created before late 2025, consider taking the following precautions:
- Change your Substack password immediately.
- Ensure the password is unique and not reused on other platforms.
- Enable two-factor authentication wherever available.
- Monitor your email inbox for phishing attempts referencing subscriptions or payments.
- Review your Stripe account activity for unauthorized changes.
- Scan your device for malware using Malwarebytes to rule out local compromise.
- Remain cautious of SMS messages referencing billing or newsletter verification.
Because the Substack leak includes structured contact data, attackers may attempt highly personalized phishing campaigns. Messages that reference your handle, subscription activity, or partial account details should be treated with suspicion.
Users who operate paid newsletters should also notify subscribers if they suspect exposure, particularly if payment-linked identifiers appear in the dataset.
The appearance of the Substack leak in February 2026 highlights a recurring pattern in breach timelines: compromise in one year, public circulation in the next. Even when the original breach is old, the risk renews the moment the data becomes widely accessible.
- Crunchyroll Data Breach Allegedly Exposes 100GB of Customer Data via Outsourcing Partner
- University of Tokyo Data Breach Confirmed After Attackers Use Stolen Researcher Credentials
- Harley-Davidson Data Breach Claim Targets Nantes Retail Location
- Odido Data Breach Escalates After ShinyHunters Begins Publishing Stolen Data
- Martec Marine Data Breach Claim Involves 67GB Leak by Tengu
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













