The North Korean remote workers infiltration ecosystem has entered a new phase after threat researchers captured the full operation live inside controlled environments. The investigation uncovered how North Korean remote workers impersonate software developers, use job scams to harvest identities, and obtain corporate access through manipulated onboarding processes. By observing the operators in real time inside sandboxed workstations, analysts were finally able to document the procedures, tools, objectives, and behavioral patterns behind a campaign that has quietly expanded for years.
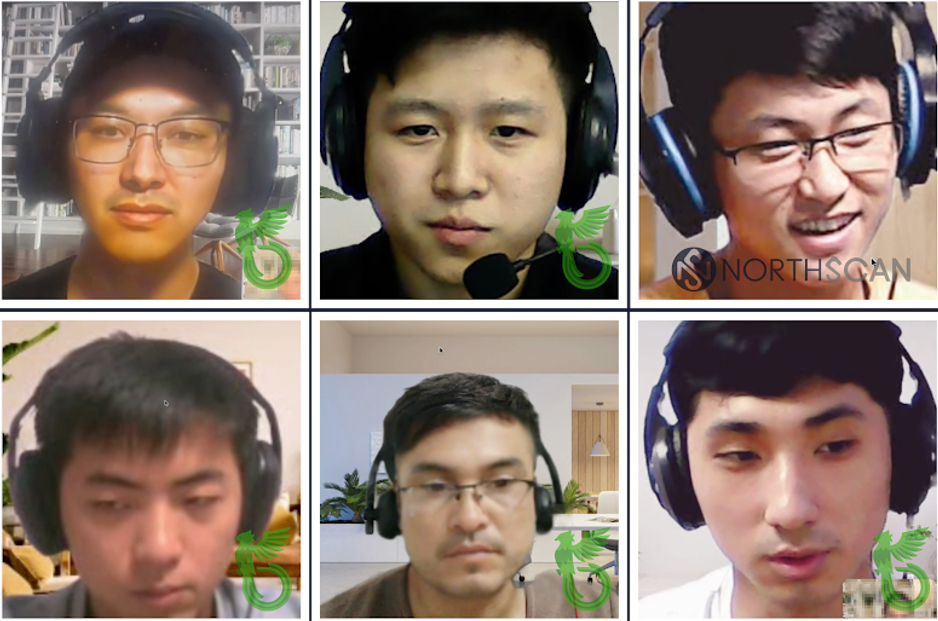
This extended investigation, conducted by BCA LTD in collaboration with NorthScan and ANY.RUN, marks the first time that researchers have watched North Korean remote workers navigate what they believed were genuine developer laptops. Every click, command, and request was recorded inside a safe virtual environment. The result is a detailed view into a threat model that blends espionage with revenue generation and uses freelance platforms as a scalable distribution mechanism.
How the Operation Was Set Into Motion
The chain of events began with a recruiter known as Aaron, also called Blaze, who contacted a United States based software developer with a seemingly legitimate job opportunity. This pattern is well documented. North Korean remote workers frequently pose as hiring agents, recruiters, or technical leads. Their purpose is to locate a candidate who can serve as a front for account verification, access token generation, payroll routing, and system access inside a targeted organization.
Instead of engaging with a real device, the researchers built an elaborate deception. ANY.RUN generated long running virtual workstations that mirrored the behavior of genuine developer laptops. These machines contained a full activity history, installed frameworks, realistic browser sessions, and a United States residential proxy. They appeared legitimate, responsive, and active. This allowed the operators to believe that they had gained control of a real workstation, which caused them to behave naturally rather than cautiously.
Inside the Live Capture: What the Operators Did First
The moment access was confirmed, the North Korean remote workers executed a predictable sequence of actions that aligned with known Lazarus Group workflows. Their initial goal was not malware deployment. It was identity replication, credential gathering, and persistent access through legitimate channels.
The operators synchronized Chrome profiles, recovered stored credentials, and deployed Google Remote Desktop through PowerShell. They established always on remote control so that they could return at any time without asking the victim for additional access. The behavior was systematic. They checked system specifications, validated the environment, installed auxiliary tools, and began configuring the workstation for long term use.
Researchers documented the use of tools that support identity takeover and behavioral camouflage. AI powered job application tools were loaded to help the operators pass interviews, generate professional responses, and apply for positions under the victim’s name. One time password managers were used to bypass multifactor authentication once identification documents were collected. The operators also used reconnaissance commands such as dxdiag, systeminfo, and whoami to confirm system integrity and hardware state.
The Moment Their Intent Became Unmistakable
During the session, one operator opened a plain Notepad window and typed a request to upload full identification documents, banking credentials, and Social Security information. This was the moment that clarified the scope and ambition of the operation. These actors were not looking to hire a contractor. They were building a complete identity container that could be used to impersonate a real developer inside companies, on payroll systems, on cloud platforms, and inside communication environments.
This reinforces a key insight. North Korean remote workers thrive when they can operate under a trusted identity. Once they obtain access to a contractor or employee’s environment, they can interact with sensitive systems without triggering typical intrusion detection alerts. Their activity is often viewed as the normal behavior of an authenticated user, which allows them to move quietly and accumulate high value intelligence.
Why Remote Work Has Become the Perfect Entry Point
Remote hiring has created a blind spot across many industries. Contractors often onboard without in person verification. Hiring teams rely heavily on digital documents and simple liveness checks. Remote workers join distributed teams without fully supervised device validation. These conditions allow North Korean remote workers to blend into legitimate workflows and operate for long periods before discovery.
The business models of many companies require constant onboarding of developers, QA engineers, designers, and IT staff. Each new contractor creates a potential opening. Once inside, the operator gains access to repositories, cloud dashboards, shared folders, ticketing systems, internal documentation, and other sensitive business functions. Most companies lack behavioral monitoring strong enough to distinguish real employees from actors operating through remote access tools.
The Broader Operational Ecosystem Behind the Scenes
The investigation also revealed a second layer of the threat model. North Korean remote workers are not simply individuals seeking positions. Many act as recruiters who build networks of collaborators through freelancing platforms. These collaborators may be aware of their role or completely unaware that they are part of a hostile operation.
The recruitment pipeline follows a documented lifecycle. An actor reaches out on platforms like Upwork, Freelancer, GitHub, or Discord. They present a work opportunity, ask the target to move to encrypted messaging, provide scripted instructions, and guide them through creating verified accounts. The collaborator then shares screenshots, identification documents, login credentials, and remote access codes. Once control is established, the operator uses the collaborator’s identity to perform work and manage financial transfers.
Extensive documentation from recovered folders shows a large number of identity records belonging to individuals across the United States, Europe, the Philippines, Malaysia, and especially Ukraine. These records include passports, driver’s licenses, tax documents, selfies used for verification, and personal data tied to freelance accounts.
The Use of Forged Documents and Synthetic Identities
One of the most concerning discoveries involved the use of fraudulent identity tools, including templates and assets sourced from the illicit marketplace VerifTools. This service, recently disrupted by authorities, provided a large library of forged documents tailored to pass automated onboarding checks. Operators used these materials to bypass KYC systems and to create high trust profiles that appeared genuine during platform reviews.
However, the investigation revealed that forged documents are only one part of the model. The operators often prefer legitimate documents harvested from their collaborators. These documents carry real risk for the victims because they allow the actors to create accounts under genuine identities with high credibility. Through video calls, remote access, and guided verification steps, the operators can complete full identity checks on multiple platforms before the victim even understands the scope of what they have enabled.
The Financial Architecture of the Operation
The revenue model behind North Korean remote workers is built on a simple formula. Eighty percent of the earnings generated through freelance work or contract labor flows back to the operator. The collaborator retains twenty percent. This arrangement incentivizes the collaborator to remain compliant, even when the activity becomes suspicious. Payments are usually routed through cryptocurrency wallets but have also been observed moving through PayPal, bank transfers, and intermediary accounts held by facilitators in Europe, Asia, and the United States.
The operators complete freelance projects such as mobile development, API integrations, software updates, architecture drawings, CAD revisions, and data entry tasks. Many of these projects involve access to sensitive systems, proprietary code, or internal company frameworks. Companies that outsource work through freelance platforms rarely understand that the person performing the work may be a North Korean remote worker operating behind a stolen identity.
The Shift From Freelance Work to Coordinated Corporate Access Operations
The captured behavior supports a long suspected theory. North Korean remote workers are shifting from simple job fraud into a structured operational model that blends recruitment, credential hijacking, remote access infrastructure, and identity laundering. This ecosystem allows actors to expand their reach far beyond what a single operator could accomplish. It also creates redundancy. If one account is banned, another can take its place. If one collaborator becomes uncooperative, a new one can be onboarded using the same scripts and documents.
The consistency of the workflows suggests that operators are trained, standardized, and supported by internal playbooks. Documents recovered from cloud drives included step by step instructions for account creation, credential sharing, communication guidelines, and troubleshooting advice. These materials read like internal documentation for a coordinated operation rather than scattered notes from independent freelancers.
The Global Impact and Strategic Significance
The implications of this activity extend beyond individual companies. The infiltration of corporate environments through remote worker pipelines presents a national security concern because it allows state linked actors to gather sensitive data, financial records, source code, and authentication tokens. The Lazarus Group and its associated units have long been connected to financially motivated intrusions, cryptocurrency theft, destructive attacks, and espionage campaigns targeting defense contractors, infrastructure operators, and technology firms.
The remote worker model provides persistent access to many organizations without requiring sophisticated exploits. The access is granted voluntarily during onboarding. The operators simply maintain presence through legitimate tools and appear as normal users. This makes detection difficult and remediation slow. Once the operators establish familiarity with a company’s internal systems, the potential for lateral movement, credential theft, and privilege escalation grows significantly.
A Model Designed to Evade Detection
The most dangerous element of this operation is its reliance on legitimate technology. Remote access tools like Google Remote Desktop and AnyDesk are widely used in business environments. AI powered application helpers are common. OTP services are often used during identity migration. The operators do not need malware because the access they obtain allows them to perform all of their objectives using trusted applications and pre installed software.
This creates major challenges for security teams. Traditional detection tools often rely on signatures, malicious binaries, unusual network patterns, or privilege misuse. None of these behaviors appear when a North Korean remote worker logs into a system using credentials voluntarily provided by a victim. Instead, defenders must rely on behavioral analytics such as impossible travel alerts, unusual session lengths, sudden access pattern shifts, and changes to payout accounts or authentication methods.
Why This Operation Is Growing Faster Than Expected
The remote work model scales naturally. North Korean remote workers do not rely on high cost infrastructure or rare exploits. They rely on people. Every collaborator they recruit becomes an entry point to multiple platforms. Each new identity unlocks another set of accounts, which unlocks additional earning potential and additional corporate access. This model can expand indefinitely as long as there are individuals willing to collaborate or too vulnerable to identify the risks.
The shift toward recruitment driven activity indicates that the operation is evolving. Operators now spend as much time onboarding collaborators as they do applying for jobs. This suggests an internal directive to scale the operation across many jurisdictions. The presence of dozens of identities inside a single actor’s cloud folder demonstrates the breadth of this expansion.
What Companies Must Do Now
The live capture of these activities provides organizations with clear lessons. Remote hiring must include stronger verification procedures. Identity checks must move beyond static documents. Companies must review for abnormal use of remote access tools, unexpected device fingerprints, and new contractor accounts that immediately begin high risk actions.
Development environments should enforce device posture validation, certificate based authentication, and behavioral anomaly detection. Freelance platform access should be limited to restricted environments. Contractors with elevated access should undergo regular credential audits and activity reviews. Most importantly. Any contractor who asks to shift communications to private channels during onboarding should be treated as a potential risk.
Why This Matters for Individuals and Freelancers
Freelancers are increasingly targeted because their identities unlock a wide range of platforms. A single Upwork account can be used to apply to jobs that grant access to sensitive environments. A single GitHub account can be used to interact with private repositories. A single set of KYC documents can be reused to pass verification for dozens of services.
Victims often do not realize the long term consequences. Their identity may be used to perform sanctioned work, route money, or access controlled environments. This exposes them to account bans, financial losses, and potential legal consequences. More importantly, it allows operators to impersonate them indefinitely across a wide array of digital ecosystems.
A Final Look at the Threat Landscape
The live capture of North Korean remote workers marks one of the most significant intelligence findings related to the Lazarus Group in recent years. It proves that their remote infiltration capabilities are mature, organized, and increasingly aggressive. These operations are capable of scaling through recruitment pipelines that blend social engineering, identity theft, and remote administration with operational discipline and a clear strategic objective.
The world of remote work has created new opportunities for global collaboration. It has also created an environment where threat actors can obtain privileged access simply by asking for it in the right way. The captured activity provides a detailed map of the North Korean remote workers ecosystem. It also highlights the urgency for companies, freelancers, and platforms to understand that a single identity compromise can serve as the foundation for a much larger intrusion.
This investigation makes one fact impossible to ignore. The North Korean remote workers model is not an isolated scam. It is a structured infiltration program that continues to grow. Without strong verification controls and awareness across every layer of the hiring ecosystem, these operations will continue to expand into more industries, more companies, and more regions, often without detection until the damage is already done.
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
- METO Systems Named in Insomnia Ransomware Claim
- SANS Took Nearly $500K From ICE for Cyber Training
WordPress Bot Protection
Bot Blocker for WordPress
Detect bot traffic, monitor live activity, apply bot-aware rules, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress admin interface.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







