The Louvre password story sounds like something out of a parody. Investigators have confirmed that one of the most famous museums in the world protected its internal video surveillance system with the password “LOUVRE.” No special characters, no security measures, just the museum’s own name. This astonishing discovery came to light after a €90 million jewel heist at the museum, exposing years of ignored warnings and severe cybersecurity negligence.
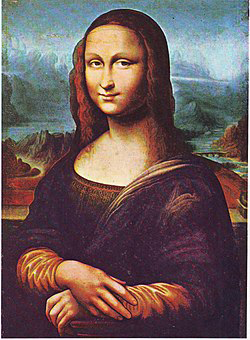
While the revelation sparked laughter online, it has also become a symbol of institutional failure. A place that guards some of humanity’s greatest treasures, including the Mona Lisa, failed to secure its digital doors. What unfolded was not just a story about a bad password but about how complacency, bureaucracy, and underestimation of risk created a perfect storm for disaster.
The Heist That Shook Paris
On October 19, 2025, Paris woke up to news of a spectacular robbery at the Louvre Museum. Thieves entered the Apollo Gallery in broad daylight using a freight elevator, smashed glass cases, and escaped on motorcycles with royal jewels worth around €90 million. The entire operation took just minutes. The robbery seemed like something out of a movie, and it immediately raised questions about how such a high-profile institution could be breached so easily.
Weeks later, French newspaper Libération obtained documents revealing that one of the museum’s surveillance servers had been protected by the password “LOUVRE.” An internal audit from the National Cybersecurity Agency of France, known as ANSSI, had flagged this weakness as early as 2014. The report explicitly warned that anyone with access to the museum’s network could “facilitate the theft of artworks.” No action was taken.
In hindsight, this single word ‘LOUVRE’ may be one of the most ironic and costly passwords ever used in history.
A Password That Should Never Have Existed
The Louvre password was as weak as it gets. Cybersecurity experts classify such credentials as “dictionary passwords,” meaning they are easy to guess and easy to crack. It is the equivalent of locking a safe and writing the combination on the door. According to the leaked reports, the museum’s network contained other default or easily guessed credentials like “THALES,” referring to one of its technology partners.
These passwords were never changed, even after multiple warnings. It is believed that bureaucratic inertia and lack of cybersecurity expertise led to a culture where no one felt responsible for fixing the problem. The museum had top-tier art conservators and security guards but no comprehensive digital security policy. The digital gatekeepers of France’s cultural crown jewel had effectively left the door wide open.
How Weak Passwords Enable Real-World Crime
Weak passwords are not just a technical issue; they are a direct path to real-world consequences. In the case of the Louvre, the risk was obvious. Anyone who managed to log in could have watched camera feeds, studied staff movements, or learned where alarms and motion sensors were located. Even if the thieves never directly exploited the password, it represented a dangerous vulnerability that could have made the robbery far easier to plan.
Experts often say that cybersecurity begins with the basics, and passwords are the most basic of all. Using predictable passwords is one of the leading causes of data breaches worldwide. Reports from major security firms have consistently shown that more than 80 percent of cyber incidents involve stolen or weak credentials. The Louvre case is a perfect example of how even prestigious institutions can fall victim to their own complacency.
Warnings That Were Ignored for Years
The Louvre’s digital security issues date back more than a decade. In 2014, ANSSI issued a detailed audit warning that the museum’s surveillance systems were outdated, poorly configured, and protected by weak passwords. The report even stated that “whoever controls the Louvre’s network can facilitate the theft of artworks.” Despite this clear message, nothing meaningful was done. Administrators continued to rely on outdated technology, and passwords remained unchanged.
By the early 2020s, the museum’s systems were running on old hardware with minimal intrusion detection. Network segmentation was poor, meaning a single breach could expose multiple systems. The museum’s IT department reportedly lacked both funding and authority to enforce proper security practices. The focus remained on physical security—locks, guards, and alarms—while digital risks were largely ignored.
This mindset is common in older institutions that view cybersecurity as an administrative chore rather than a core responsibility. In this case, that mindset turned into an international embarrassment.
The Global Reaction
When the story broke, it became an instant headline around the world. People could hardly believe that the most visited museum on the planet had used its own name as a password. Social media exploded with jokes, memes, and disbelief. Yet for cybersecurity experts, the news was less funny and more frustrating. It was a textbook example of what happens when critical warnings are ignored.
French Culture Minister Rachida Dati called it “a chronic and structural underestimation of risk.” Prosecutor Laure Beccuau, who led the investigation, said that the suspects were not criminal masterminds but opportunists who simply took advantage of glaring weaknesses. Even President Emmanuel Macron reportedly requested a review of the country’s national museum security systems after the scandal.
Inside the Investigation
As the cybersecurity scandal unfolded, police continued to hunt for those responsible for the robbery. Four people were taken into custody, including a couple in their thirties who lived in the Paris suburbs. DNA evidence linked them to the freight elevator used during the heist. Another suspect was arrested at Roissy Airport while attempting to flee to Algeria. Investigators said the suspects had previous convictions for theft and violence but were not considered sophisticated criminals.
Authorities now believe that the thieves may have received information from inside the museum or taken advantage of digital blind spots caused by weak cybersecurity. Although there is no public evidence that the password “LOUVRE” was used during the heist, it perfectly illustrates the kind of environment that allowed such an operation to succeed. In other words, the museum’s weak internal systems made it an easy target for anyone willing to test its limits.
Why Passwords Still Matter
The Louvre password revelation is not just an embarrassing story, it is a serious reminder of how fragile modern security can be. In an age where organizations talk about artificial intelligence and advanced encryption, many still fail to manage the simplest form of digital protection. Strong passwords remain the first and most effective defense against intrusion, yet they are often treated as an afterthought.
Cybersecurity researchers point out that weak credentials are like termites in a wooden structure. You may not see the damage right away, but over time they weaken everything around them. Once inside, attackers can escalate their privileges, disable alarms, or plant malware. In the Louvre’s case, even if the heist was primarily physical, the digital vulnerability was symbolic of the same carelessness that allowed the theft to happen.
The Fallout and Reforms
The French government has since ordered a nationwide review of cybersecurity standards across all cultural institutions. The Ministry of Culture announced plans to enforce mandatory password rotation, two-factor authentication, and network audits at least twice per year. The Louvre itself has begun modernizing its surveillance and access systems, replacing outdated equipment and hiring new cybersecurity personnel.
Rachida Dati stated that digital security would now be treated as equal in importance to physical security. The museum has also introduced new employee training programs designed to improve awareness of digital hygiene. These reforms are not just about preventing another heist; they are about restoring public confidence in France’s ability to protect its cultural heritage.
A Lesson for the World
The Louvre password incident is more than a French embarrassment. It is a lesson for every organization that thinks reputation or size protects it from human error. Whether it is a museum, a hospital, or a corporation, security depends on discipline and awareness. Technology can only go so far if the people using it fail to take it seriously.
For cybersecurity professionals, the story has become a shorthand for preventable failure. It shows how decades of progress in technology can be undone by one lazy decision. It also highlights the growing intersection between digital and physical security. In modern institutions, those two worlds are inseparable. The Louvre case proves that one weak password can become the missing piece in a much larger puzzle of failure.
From Ridicule to Reform
While the world laughed at the absurdity of the Louvre password, France responded with action. The incident has already prompted major reviews in other European museums and government buildings. It may also push institutions worldwide to audit their own systems and policies before they find themselves in similar headlines.
In the end, the story of the Louvre password will likely be remembered as both tragic and ridiculous. Tragic because it revealed how easily human negligence can undermine centuries of cultural preservation, and ridiculous because a world-class museum guarding priceless art trusted its name as its key to security. It is the perfect example of how in cybersecurity, the smallest details can create the biggest disasters.
For continued updates on cybersecurity news, global data breaches, and digital security analysis, visit the Cybersecurity section on Botcrawl.
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
- METO Systems Named in Insomnia Ransomware Claim
- SANS Took Nearly $500K From ICE for Cyber Training
WordPress Bot Protection
Bot Blocker for WordPress
Detect bot traffic, monitor live activity, apply bot-aware rules, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress admin interface.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.







