
A sextortion email scam sends you an email from your own account, claims your email is hacked and to change your password, then tries to blackmail you for a Bitcoin payment.
A new sextortion email campaign appears out of the blue just about every day. One of the latest email scams claims that your email account is hacked and to change your password.

The way it works is that you will receive an email that looks like it was sent to you from your own account; However, the email was not sent to you from your own account. No one accessed your account to send you the message. A third-party email spoofing service was used to make it look like someone sent you a email message from your own email address.
The email message says that a hacker attacked your operating system and gained full access to your email account.
It claims that the hacker attacked your router and put a malicious code on it. It also says that a Trojan is on your device’s operating system.
The purpose of this email scam is to scare you and fraudulently blackmail you into paying them. The way they do this is by claiming to have taken images and videos of you through your device’s camera while you visited adult websites.
The email says that if you do not pay them within a certain amount of time they will send the images and videos to your relatives, friends, and colleagues.
To be clear, this is a scam and your email account was not hacked. There are no images or videos of you visiting adult sites.
This is not a new scam, there have been many like it in the past. Other email scams like this will provide you with sensitive information such as your account’s password or phone number.
Unfortunately, if you received this email or one like it, it means that your information was compromised and leaked online following a breach that occurred on websites like LinkedIn or Adobe. Scammers use information leaked about you (such as your email address, email account password, and telephone number) against you in order to attempt to blackmail you.

To locate a breach where your information may have been leaked from check out https://haveibeenpwned.com/. You can input your email address to locate where your information was leaked.
We recommend that you immediately change your password if you have received this email or one like it.
Transcript from email message:
Subject: [Your Email Address] is hacked! Change your password now!
From: [Your Email Address]
To: [Your Email Address]
Date Today 08:27
I greet you!I have a bad news.
22/08/2018 – On this day, I attacked your operating system and fully accessed your account at [Your Email Address].That’s it.
There is a vulnerability in the software of the router you are connecting to that day.
I first attacked this router and put malicious code on it.
When you type over the Internet, my Trojan is installed on your device’s operating system.After that, I completed your disk dump (I have all your address books, view the history of the site, all files, phone numbers and addresses of all contacts).
A month ago, I wanted to lock your device and ask for a small amount of money to unlock it.
But I looked at the websites you visit frequently. I am shocked by your favorite resources.
I am talking about adult websites.I want to say – you are a big pervert. You have a dazzling fantasy!
After that, I thought of an idea.
I made a screenshot of your favorite adult website (you know what I mean, is it?).
After that, I took photos of you and your entertainment while browsing this website (I used your device’s camera).
The result is great! Do not hesitate!I am convinced that you do not want to show these photos to your relatives, friends or colleagues.
I think the $373 for my silence is small.
In addition, I spent a lot of time on you!I accept money in Bitcoin.
My BTC wallet: 1P7bLeCJywaaDRQpT7iwb4qzUHa4CpRFyPYou don’t know how to add bitcoin wallet?
Write “How to add a btc wallet” in any search engine.
this is very simple.For payment, you have a little more than two days (just 50 hours).
Don’t worry, the timer will start when you open this letter. Yes, yes.. it has already started!After the payment, my virus and your compromise are automatically destroyed.
If I don’t receive the amount you specify, your device will be blocked and all your contacts will receive your entertainment photos.Be cautious!
– Don’t try to find and destroy my virus! (All your data has been uploaded to the remote server)
– Do not try to contact me (this is not possible, I sent you this email through your account)
– Various security services are not helpful to you; format the disk Or destroying the device doesn’t help, because your data is already on the remote server.PS: I promise that I will not bother you after payment, because you are not my only customer.
This is a honour criterion for hackers.From now on, I recommend that you use good anti-virus software and update it regularly (a few times a day)!
Don’t be angry with me, everyone has their own work.
Goodbye.
Although this might sound frightening and seem like a real threat, but it’s not. It is a confirmed scam and you have nothing to worry about. The same exact message has been sent to many people and there have been many campaigns like it in the past. For example, a previous email claimed that a spyware software developer hacked your account and shows you the past or current password to your email account.
If you have never visited an adult website, you will still receive the message. If your device does not have a camera on it, the message will still claim to have taken pictures and videos of you through your camera.
Since this is a scam and you are not in danger please DO NOT PAY THE SCAMMER. They have not accessed your email account and they have not taken photos or videos of you. The only thing that you need to do is change the password to your email address and other accounts you have to ensure your safety.
The email message does not mean that your computer is infected with malware if you received this email message or one like it; However, if you would like to scan your computer for malware and other potentially malicious files to make sure that your computer is clean we recommended to use Malwarebytes.
Here are some instructions to scan your computer for malware and remove malware if found:
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, click the file you just downloaded. It can usually be located in the Download folder.
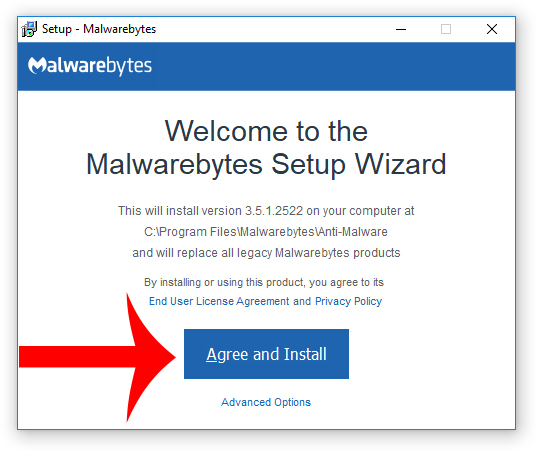
3. A window that says “Welcome to the Malwarebytes Setup Wizard” will appear. Click Agree and Install to begin the installation. Once complete, click Finish.

4. Now the Malwarebytes is installed, open the program and click the Scan Now button – or go to the Scan tab and click the Start Scan button.

3. When the scan is complete click the Quarantine Selected button.
4. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
- OneDrive Email Scam: How It Works, Warning Signs, and How to Stay Protected
- Women and Children Support Foundation Email Scam Promises Fake $1 Million Donation
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.














1 Comment
Thanks for the article. I got a very similar email and got confused as the password was wrong. The text in the mail is mostly identical, with a few differences. But this article greatly calmed me down.