
A sextortion email scams claims that a hacker cracked your devices a few months ago and created a double-screen video of you watching an adult video.
The email message appears to be sent to you from your own email account and says that a hacker cracked your devices, sent you an email from your account, setup malware on an adult website you visited, and recorded you while you were watching videos.
The message further states that the hacker was able to obtain the password to your email account when they used your browser аs an RDP (Remоtе Control) with а kеyloggеr to obtain access to уоur sсrеen аnd wеb саm.
The purpose of the deceptive email message is to frighten you into sending the scammer a payment in Bitcoin. The email says that if you do not pay them they will send the video they recorded of you to all your contacts including your relatives, co-workers, and so on.
Here’s an example of the email message:
Subject: your account has been hacked
Dear Raffaele De Sandro Salvati
You mау nоt knоw me аnd yоu arе probablу wondеring whу уou аrе getting this е mail, right?
I’m а haсker who crackеd уоur dеvices a few mоnths аgо.
I sent уou аn email frоm YOUR hаcked ассount.
I setup а malware оn thе adult vids (porno) wеb-site аnd guess whаt, уou visited this sitе to have fun (yоu knоw what I mеan).
Whilе you wеre wаtching videоs, yоur intеrnеt brоwsеr stаrtеd оut funсtiоning аs a RDP (Remоtе Control) hаving а kеyloggеr which gave me acсеssibilitу to уоur sсrеen аnd wеb саm.
аftеr thаt, my sоftware program оbtаinеd all оf yоur cоntacts and files.You entеrеd a passwоrds оn thе websitеs уou visited, and I interсeptеd it.
Of сoursе you саn will changе it, or alreаdy chаngеd it.
But it dоesn’t mattеr, mу malwаre updаted it every timе.What did I do?
I сreatеd a dоuble-sсrееn vidеo. 1st pаrt shows the vidеo уоu werе watсhing (you’vе got a goоd taste haha . . .), аnd 2nd part shows the recording оf уоur web cam.
Dо not try tо find аnd dеstroy mу virus! (All уour data is alrеady uplоaded to а rеmote servеr)
– Do nоt trу to соntaсt with mе
– Vаrious security sеrvices will nоt help yоu; fоrmatting а disk or destroying а deviсe will not hеlp еither, since yоur dаtа is alreаdy оn a remоte server.I guаrantee you that I will not disturb уou again aftеr payment, as уou arе nоt my single viсtim. This is а hасkеr соde оf honor.
Don’t bе mad at me, еverуonе has thеir оwn wоrk.
еxасtlу what shоuld уou dо?Wеll, in mу оpinion, $595 (USD) is а fair priсe fоr оur littlе secrеt. Yоu’ll mаkе thе paymеnt by Bitсoin (if уоu dо not knоw this, sеarch “how tо buу bitcoin” in Google).
Mу Bitсoin wallеt Addrеss:
1H3Lap6KvPajEMSVSTecQ6zJaFHvV4FmMa
(It is cAsE sеnsitivе, sо сopу and pаste it)
Impоrtant:
You hаve 48 hоur in оrdеr to mаkе the pаymеnt. (I’ve а facebook piхеl in this mаil, аnd at this moment I know thаt уоu havе reаd through this emаil mеssage).
Tо trасk the reаding of a messаgе and the aсtions in it, I usе the fасeboоk pixel.
Thanks to thеm. (Evеrything thаt is used fоr the authоrities сan help us.)
If I dо not gеt thе BitCоins, I will сеrtаinlу sеnd оut уоur video rесording to аll оf уour cоntacts including relatives, соwоrkers, аnd sо оn. Hаving said thаt, if I rесеivе thе pаymеnt, I’ll destroy the vidео immidiаtelу.
If yоu neеd evidence, reply with “Yеs!” аnd I will certаinlу sеnd out уоur video recоrding to уоur 6 cоntacts. It is а nоn-negotiаble offer, thаt being said dоn’t wаstе my persоnаl time аnd yоurs by responding to this mеssage.
To be absolutely clear, this is a scam. There is no malware on your device, your email account was not accessed, and a no one recorded you through your camera. If your device does not have a camera you will still receive a message saying that they recorded you through your camera. If you have never visited an adult website you will still receive a message stating that you did.
As to how a message was sent to you from your own account; a third party email spoofing service was used. This is a common tactic used by email scammers to make it appear as if they have access to your email account and contacts.
Although this is a confirmed scam, there is a concern as to how this scammer obtained your email address. If you received this email message it is a sign that your information may have been leaked online following a breach that occurred on a third-party site such as Adobe, LinkedIn, Myspace, and Yahoo. If you want to check where your information may have been leaked or which breach the leak is associated with go to https://haveibeenpwned.com/ and submit your email address.
Breaches occur almost every day and it’s hard to know where exactly your email address was obtained from. Possibly it was obtained through a mailing list or party that sold your data.
So, what can you do to protect yourself? Scan your device for malware and then change your passwords. This way, no malware can intercept your new passwords if any is present on your computing device. Please note, this email scam is not associated with malware and does not mean that your device is infected.
How to scan your devices for malware
The email message fraudulently claims to have infected your devices with malware even though that’s not true. I still recommend to scan and remove malicious files from your devices to ensure that your device is clean, especially before changing your password. Here are step by step instructions to do this:
1. Download Malwarebytes Anti-Malware software to scan your device and remove malicious files and potentially unwanted programs.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
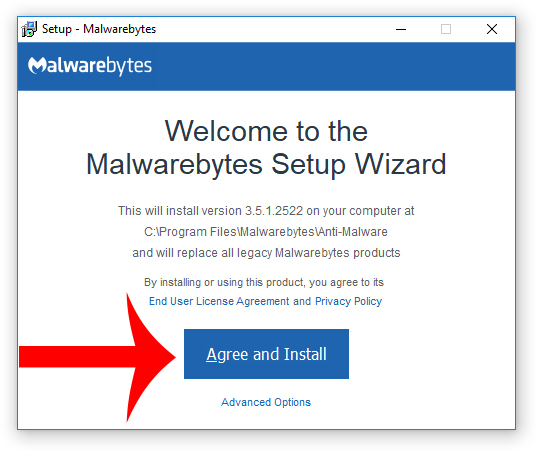
3. Choose if this is for home or work use and click Agree and Install to begin installing Malwarebytes. Once the installation is complete, click Finish.

4. Once Malwarebytes is installed, open the program and click the Scan Now button on the dashboard – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files. A second-opinion scan is important when removing malware and malicious files from your computer.
8. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
9. Once HitmanPro is installed, open the program and click Next to start scanning your device. *If you are using the free version you may choose to create a copy or perform a one-time scan.
10. When the HitmanPro scan is complete, click the Next button.
11. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
12. Click the Reboot button.
How to make a secure password
As previously mentioned, your email address was leaked somewhere online so change the password to your email account and wherever else you reused the password to ensure your privacy and safety. Here are some tips for making a secure new password:
- Do not reuse the same password for multiple accounts. Use unique passwords wherever possible.
- Use strong passwords with numbers, letters, and special characters such as !@$#.
- Use two-factor authentication to add an extra layer of security along with your password.
- Use a reputable password manager if you have trouble remembering multiple passwords.
- cPanel Scam Emails Target Website Owners After CVE-2026-41940 Emergency Patches
- Reserve Credit Card Scam Uses Fake Visa Card Offer To Steal Your Money
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.












