The VaultCrypt virus (Vault Crypt virus) is ransomware that has been spreading through Russia and is on it’s way to other countries including the United States. The VaultCrypt virus would runs and generates a unique RSA 1024 public and private key pair labeled Cellar using GnuPG in order to encrypt any files that match the .xls, .doc, .pdf, .rtf, .psd, .dwg, .cdr, .cd, .mdb, .1cd, .dbf, .sqlite, .jpg, and .zip file extensions.
The VaultCrypt virus takes control of an infected computer system and encrypts personal files. It restricts access to a computer system and will leave a message on the infected computer’s desktop, open a webpage with a message, or leave a text file demanding the computer owner pay a ransom or purchase VaultCrypt decryption software using Bitcoins or other online credit system.
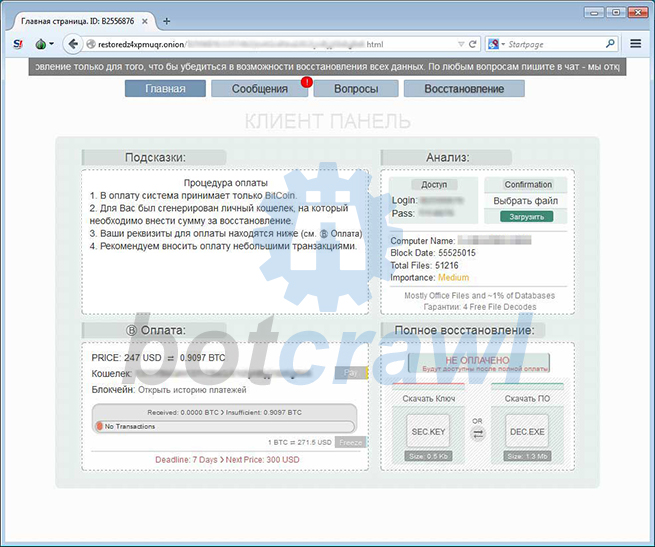
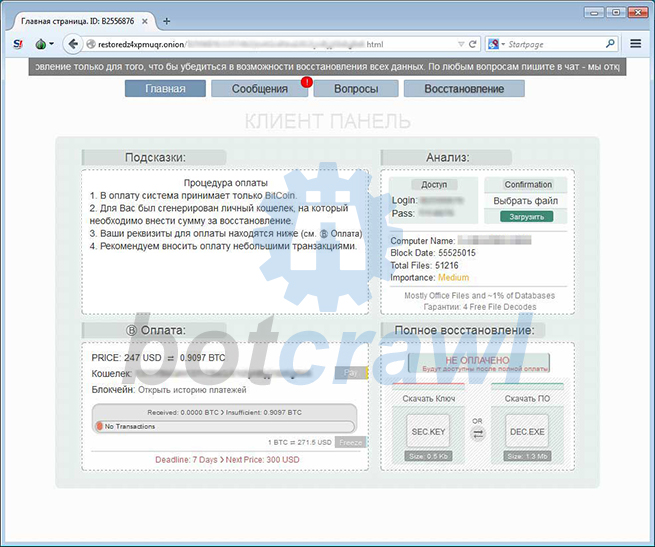
What makes VaultCrypt ransomware stand out is that it modifies Windows registry to include a new .vault extension and that changes an encrypted files icon to a lock. When a Vault file is double clicked, instead of opening the file, an alert will be shown stating that the file was “Stored in Vault” and that you needed to go to restoredz4xpmuqr.onion to get the key.

The alert displayed by VaultCrypt ransomware might say “mshta.exe vbscript:Execute(“msgbox “” STORED IN VAULT:””&vbNewLine&”” %1″”&vbNewLine&vbNewLine&ChrW(10139)&”” Visit for key: http://restoredz4xpmuqr.onion””&vbNewLine&vbNewLine&”” [accessible only via Tor Browser: http://torproject.org]””,16,””VaultCrypt [Permission Error: No Key]””:close”)”
Victims of the virus who pay the fine and follow the instructions on the message might be able to retrieve their personal files and remove the ransomware, but it is not suggested to do so. Instead, malware analysts suggest to first use various procedures and third-party computer security software to remove the VaultCrypt virus and similar ransomware. Paying the ransom may actually cause further issues for some computer users.
- 4 files associated with ValutCrypt ransomware can be found at these paths: 1. %appdata%\CONFIRMATION.KEY, 2. %appdata%\VAULT.hta, 3. %appdata%\VAULT.KEY, and 4. %Desktop%\vault.txt.
- 2 registry entries created: HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\vltnotify “mshta %appdata%\VAULT.hta” and HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\VAULT Notification “mshta %appdata%\VAULT.hta”
How to remove VaultCrypt (Removal Instructions)
1. We strongly recommend writing down the toll free number below in case you run into any issues or problems while following the instructions. Our techs will kindly assist you with any problems.
if you need help give us a call
2. Download and install the free or full version of Malwarebytes Anti-Malware.
3. Open Malwarebytes Anti-Malware.

4. Click the large Scan Now button or visit the “Scan” tab to scan your computer for VaultCrypt malware and malicious files.

5. Once the scan is complete, click the Quarantine All button to remove the files and restart your computer.
User accounts
Ransomware usually infects 1 user account on Windows systems at a time. Here are some tips to remove ransomware by using different user accounts.
- Log into an account not affected by malware (with administrative rights) and perform a scan with reputable software to detect and remove malware.
- You can also delete the infected account.
- Other options include creating a new user account to remove malware if only 1 Window’s user account is present on the computer system.
Internet/network issues
Safe Mode With Networking can be used to access the Internet for updates, drivers, removal software, or other files if internet and network connectivity is compromised.
- Amazon Prime Video Outage Triggers Cyberattack Claims by 313 Team
- CPUID Compromise Served Malware Through Official CPU-Z and HWMonitor Downloads
- FBI and CISA Warn Iran-Affiliated Actors Are Targeting PLCs Across U.S. Critical Infrastructure
- North Korea Hackers Tied to Axios npm Package Supply Chain Attack
- Axios Supply Chain Attack Pushes RAT Malware Through npm Install
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.