
A sextortion email scam sends you an email from your own account, claims they hacked your mailbox, and attempts to blackmail you for a Bitcoin payment.
A new sextortion email scam is making rounds. An email message might appear to be sent to you from your own email address. It claims that a coder hacked your mailbox and has access to all your accounts, social media networks, email, and browsing history.
The email goes on to say that they took images (or screenshots) of you through the camera on your device while you were visiting “intimate” sites.
The message tries frighten you into thinking that they really did hack your account and did capture you through your camera while you were visiting adult websites even though none of this is true.
The email states that they will send your “files and history of visiting sites” to your contacts if you do not pay them them in Bitcoin within 48 hours.
To be clear, this is a scam. Your email account was not hacked and no one sent an email to you from your own account. A third-party email spoofing service was used to send you the email message and make it appear as if someone else had access to your email. Also, there are no images or videos of you visiting intimate sites.
This is not a new scam, there have been many like it before. Other email scams like this will provide you with the password to your email account and other personal information such as your phone number in order to seem real.
Unfortunately, if you received this email or one like it, it means that your information was leaked online following breaches that occurred on websites like LinkedIn and Adobe. Scammers use information leaked about you (such as your email address, email account password, and telephone number) against you in order to attempt to blackmail you. We recommend that you immediately change your password if you have received this email or one like it.
To locate a breach where your information may have been leaked from check out https://haveibeenpwned.com/. You can input your email address to locate where your information was leaked.
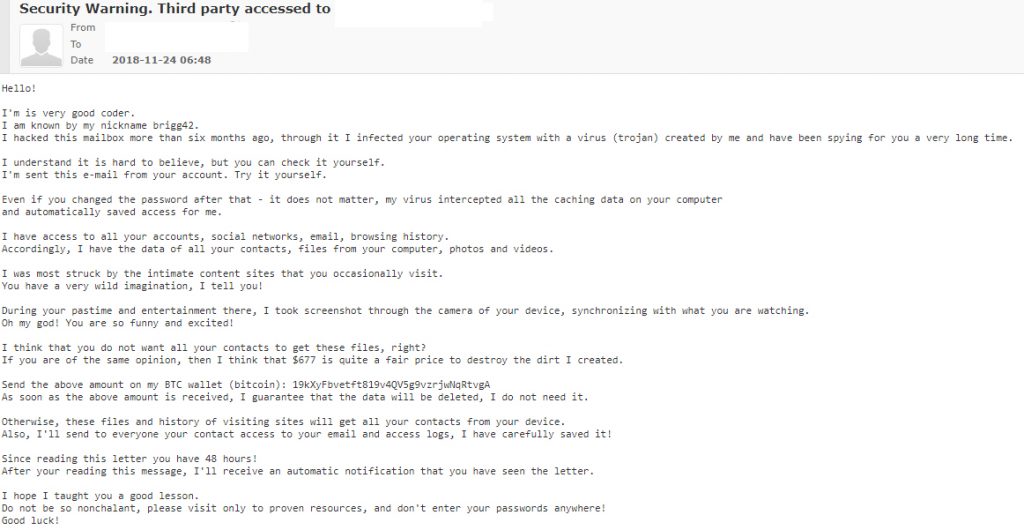
Transcript from email message:
Subject: Security Warning. Third party accessed to [your email address].
From: [your email address]
To: [your email address]Hello!
I’m is very good coder.
I am known by my nickname brigg42.
I hacked this mailbox more than six months ago, through it I infected your operating system with a virus (trojan) created by me and have been spying for you a very long time.I understand it is hard to believe, but you can check it yourself.
I’m sent this e-mail from your account. Try it yourself.Even if you changed the password after that – it does not matter, my virus intercepted all the caching data on your computer
and automatically saved access for me.I have access to all your accounts, social networks, email, browsing history.
Accordingly, I have the data of all your contacts, files from your computer, photos and videos.I was most struck by the intimate content sites that you occasionally visit.
You have a very wild imagination, I tell you!During your pastime and entertainment there, I took screenshot through the camera of your device, synchronizing with what you are watching.
Oh my god! You are so funny and excited!I think that you do not want all your contacts to get these files, right?
If you are of the same opinion, then I think that $677 is quite a fair price to destroy the dirt I created.Send the above amount on my BTC wallet (bitcoin): 19kXyFbvetft819v4QV5g9vzrjwNqRtvgA
As soon as the above amount is received, I guarantee that the data will be deleted, I do not need it.Otherwise, these files and history of visiting sites will get all your contacts from your device.
Also, I’ll send to everyone your contact access to your email and access logs, I have carefully saved it!Since reading this letter you have 48 hours!
After your reading this message, I’ll receive an automatic notification that you have seen the letter.I hope I taught you a good lesson.
Do not be so nonchalant, please visit only to proven resources, and don’t enter your passwords anywhere!
Good luck!
Although this might sound frightening and seem real, it is confirmed to be a scam. Your account was not hacked and no one took pictures of you. The same exact message has been sent to many people and there have been many campaigns like it in the past. For example, a previous email claims that a spyware software developer hacked your account and shows you the past or current password to your email account.
If you have never visited an intimate website, you will still receive the same message. If your device does not have a camera, the message will still claim to have taken pictures of you through your camera.
Since this is a scam and you are not in danger please DO NOT PAY THE SCAMMER. They have not accessed your email account and they have not taken photos or videos of you. The only thing that you need to do is change the password to your email address and other accounts you have to ensure your safety.
The email message does not mean that your computer is infected with malware if you received this email message or one like it; However, if you would like to scan your computer for malware and other potentially malicious files to make sure that your computer is clean we recommended to use Malwarebytes.
Here are some instructions to scan your computer for malware and remove malware if found:
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, click the file you just downloaded. It can usually be located in the Download folder.
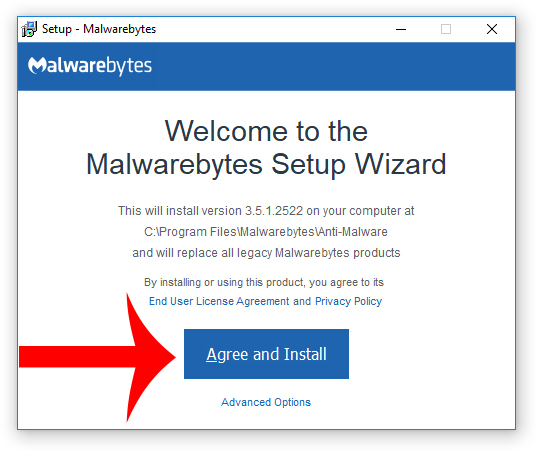
3. A window that says “Welcome to the Malwarebytes Setup Wizard” will appear. Click Agree and Install to begin the installation. Once complete, click Finish.

4. Now the Malwarebytes is installed, open the program and click the Scan Now button – or go to the Scan tab and click the Start Scan button.

3. When the scan is complete click the Quarantine Selected button.
4. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
- OneDrive Email Scam: How It Works, Warning Signs, and How to Stay Protected
- Women and Children Support Foundation Email Scam Promises Fake $1 Million Donation
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.













