Search Defender Prime (Search Defender) is a potentially malicious browser extension self-described as “an upgraded security focused search experience.” When the Search Defender Prime is installed it will change existing browser settings and replace the new tab page, default search provider, and start page with searchdefenderprime.com.

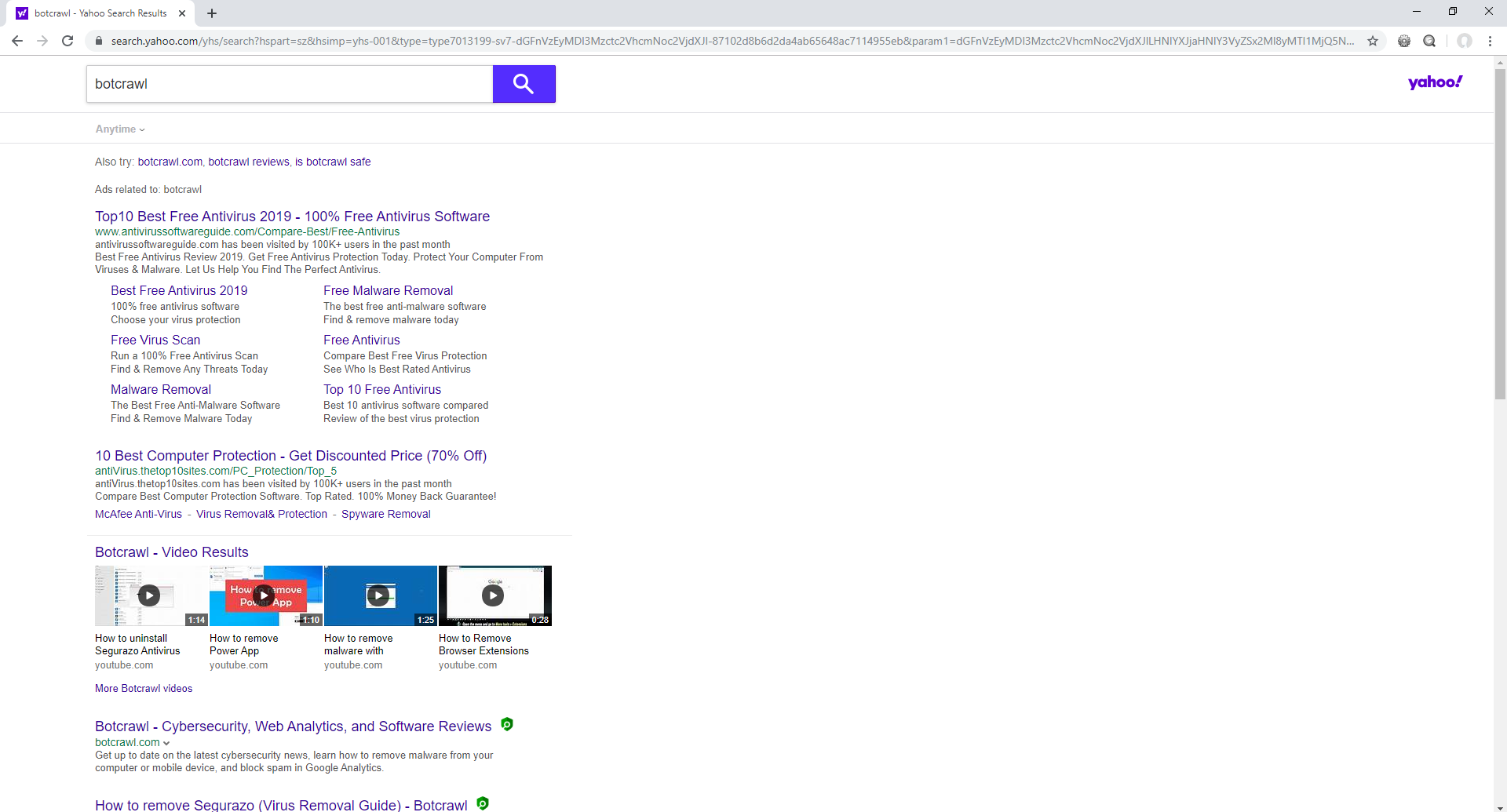
The searchdefenderprime.com website is used to intercept what users search for online and track other browser data with the use of small data files it downloads onto a user’s computing device. Known as an interceptor website, searches performed in the address bar will redirect to searchdefenderprime.com and then to another site such as search.yahoo.com instantaneously. This is done in order to eavesdrop what the user searched for before using yahoo.com to show search results.
In addition, the Search Defender Prime extension may perform tasks that may invade privacy and cause other issues. For example, the Search Defender Prime extension has permission to read your browsing history and change your search settings to searchdefenderprime.com. The extension can even read and collect browsing history while the user is in incognito mode.

The Search Defender Prime extension and other extensions similar to it including Heyweb, Genius APP, and Power App utilize unethical, deceptive, and aggressive advertising methods, including malicious advertising networks, in order to get onto a browser. Webpages and advertisements promoting the extension will attempt to force users to install them, or at least make it confusing, by continuously showing error messages.
The use of malicious advertising networks by the extension also means that it may bundle with or be advertised alongside third-party malware, adware, browser hijackers, spyware, ransomware, potentially unwanted programs, and other threats. Third-party threats provide even greater security and privacy risks. It is recommended to scan your computer immediately to remove such threats.
These are symptoms you may experience when the Search Defender Prime extension is installed:
- Pop-up advertisements
- Pop-up notifications
- Hijacked homepage
- Hijacked search engine
- Hijacked new tab page
- Constant browser redirects
- Other suspicious browser extensions installed
- Other suspicious software installed
- Slower browser performance
- Slow and sluggish PC
How to remove Search Defender Prime
Like most browser extensions, the Search Defender Prime browser extension can be manually removed through browser settings. However, removing the browser extension through browser settings will not remove malware, adware, spyware, viruses, and other threats from an infected computer. To remove malware and other threats from an infected computer, we recommend scanning a computer with reputable security software that is known to detect and remove malware and other threats. Follow the guide below to completely remove Search Defender Prime and malware from any computer.
How to remove the Search Defender Prime extension
How to remove tracking files and repair Windows registry
How to remove the Search Defender Prime extension
Google Chrome
1. Open the menu and go to More tools > Extensions
2. Click the Remove button
Mozilla Firefox
1. Open the menu and go to Add-ons
2. Click the Remove button
How to remove malware
1. Download and install Malwarebytes.

2. Once Malwarebytes is installed, click the Scan Now button to begin scanning the computer.

3. When the scan is complete, click the Quarantine Selected button to remove all threats detected by Malwarebytes.
4. Reboot the computer.
5. Once the computer is rebooted, download and install HitmanPro or HitmanPro.Alert to perform a second-opinion scan and remove the remaining malware (if applicable). To download the executable file, fill out the information on their website (name and email address) and click submit.
6. Once HitmanPro is installed, click the Next button to begin scanning the computer.
7. When the scan is complete, click the Next button to remove all threats detected by HitmanPro.
How to remove tracking files and repair Windows registry
1. Download and install CCleaner Free or CCleaner Professional.
2. Once CCleaner is installed, go to the Easy Clean tab.

3. Click the Analyze button to find trackers and junk files that CCleaner can remove.

4. When the analysis is complete, click the Clean All button.

5. Next, go to the Registry tab and click the Scan for Issues button.

6. When the scan is complete, click the Fix selected Issues… button.

7. As a precaution, click Yes to back up the registry before making changes to it and save the Reg File (.reg) file to your computer.

8. Click the Fix All Selected Issues button and then click Close once all problems have been removed.
- Shai-Hulud Malware Clone Powers New Npm Infostealer and DDoS Campaign
- FBI Seeks Info in Steam Malware Investigation
- GhostPoster Browser Extensions Reached 840,000 Installs Before Removal From Stores
- Kimwolf Android Botnet Exploits Residential Proxies to Breach Internal Networks
- ClickFix Attack Uses Fake Windows BSOD Screens to Deploy Malware
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.