CloudExtender
CloudExtender by AltoCloud (also searched for as CloudExtender virus) is a potentially unwanted program that bundles with malware, adware, and other unwanted programs.

The CloudExtender potentially unwanted program is usually introduced to a machine by free programs, deceitful updates, and torrent files. Some free programs do not detail that CloudExtender and other potential threats will download. In fact, a victim may even chose to cancel the installation process; However, CloudExtender and other program will still download and install in the background without user consent or knowledge.
Most victims are unaware that CloudExtender has infected their computers until problems arise from the program and other threats that it bundles with. Once CloudExtender is installed it will run a process named CloudExtender (32 bit) in Windows Task Manager, it will create a new Startup task to run every time Windows starts, and it will display a pop-up advertisement or alert message on the bottom right of Windows taskbar.
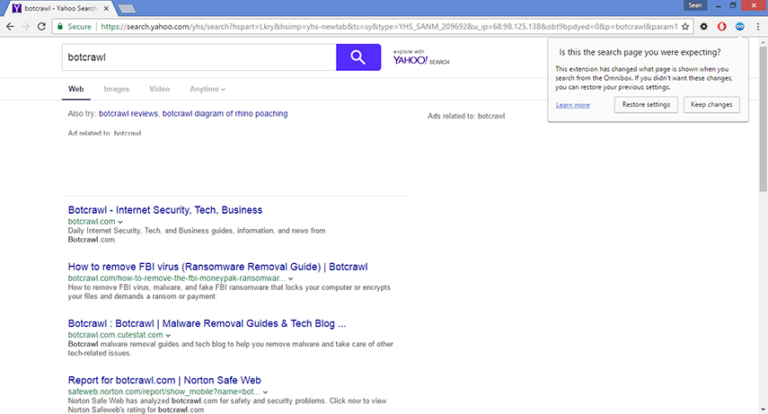
The program will display an alert message on the corner of the screen and the programs that it bundles with will cause other issues. A victim may notice a “Search the web” toolbar at the top of Windows desktop or fall victim to other symptoms associated with adware and spyware.
If a computer becomes infected with adware the computer user will notice pop-up advertisements, pop-under advertisements, and other types of advertisements while logged into the system or browsing the web. An infected internet browser may also continuously launch full-page advertisements and other pop-ups while the user is logged in. This can make the machine difficult to use.
A computer infected with CloudExtender and other threats will most likely be slow and sluggish, internet connectivity may also decrease, and the machine’s total performance may decrease. Most computers will eventually crash which can restrict the amount of time a user is logged in.
Steps to remove CloudExtender and other malware from your computer |
Uninstall CloudExtender
- Open Windows Start Menu and go to the Control Panel (or select Programs and Features).
- Click Uninstall a program (in earlier versions of Windows this is called Add and remove programs) in the Programs section in Windows Control Panel.
- Search for CloudExtender and other unwanted programs in the list of programs installed on your computer. If you cannot find programs installed on your computer it is recommended to remove CloudExtender with Malwarebytes and then perform a second opinion-scan with HitmanPro to remove remaining trace files.
- Double click the program you want to remove to begin the uninstall process.
| You might find these links useful: |
Remove unwanted browser attachments from your browsers
Chrome
- Click the Customize and control Google Chrome icon and go to More tools > Extensions.
- Click the trashcan icon next to the unwanted extension to remove it.
Firefox
- Open the Menu and click Add-ons.
- Click Remove next to the unwanted add-on you to remove it.
Safari
- Go to Safari > Preferences > Extensions.
- Click the Uninstall button next to the unwanted extension you to remove it.
Remove CloudExtender virus with Malwarebytes
- Open your browser window and download Malwarebytes 3.0 Premium or Malwarebytes Anti-Malware Free. <<CLICK HERE TO BUY MALWAREBYTES 3.0>>
- Open the executable file (mb3-setup.exe) to begin installing Malwarebytes.
- Select your language, click Next, then select “I accept the agreement,” click the Next button several times, and then click the Install button to install Malwarebytes. Click Finish once the install process is complete.
- Open Malwarebytes and click the Scan Now button on the Dashboard to begin scanning your computer.
- Click the Quarantine Selected button once the scan is finished.
- If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
Perform a second opinion-scan with HitmanPro
- Open your browser window and download HitmanPro. <<CLICK HERE TO BUY HITMANPRO>>
- Open the executable file (hitmanpro_x64.exe or hitmanpro_x32.exe) to begin installing HitmanPro.
- Click the Next button, check “I accept the terms of the license agreement,” and click the Next button again.
- On the Setup page select “Yes, create a copy of HitmanPro so I can regularly scan this computer (recommended)” and add your email address to the registration fields to begin the free trial.
- Click Next to begin scanning your computer.
- Once the Scan results are displayed click the Next button and click the Next button again on the Removal results page.
Troubleshoot
- How to restore your computer
- How to recover your computer to factory settings
- How to protect your computer against future threats
How to restore your computer
If a restore point has previously been established on your machine you will be able to perform a system restore in order to restore your machine to a date and time before it was infected. You will lose files on your computer that were obtained prior to the restore point.
There are several options to restore your computer. Most computers have their own restore software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default restore program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
How to recover your computer to factory settings
A system recovery (or reset) will recover your computer to factory settings. You will lose the current programs and files on your computer.
There are several options to recover your computer to factory settings. Most computers have their own recovery software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default recovery program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
How to protect your computer against future threats
The key to staying protected against future infections is to take advantage of reputable Antivirus software and Antimalware software with real-time protection.
Security software like Malwarebytes 3.0 Premium and Vipre Antivirus have real-time features that can block malicious files before they spread across your computer. These programs bundled together can establish a wall between your computer and cyber criminals.