
Arasak.com is a new browser hijacker we recently discovered that takes over the homepage (or startup page) of your internet browser. When malware has infected your computer it will change your homepage to arasak.com so that when you launch a new browser window you will open on the website.
The arasak.com website is deceptive and attempts to appear like Google; It’s basically a blank web page with a Google search feature, advertisement, and links to YouTube, Gmail, Translate, and Maps.
What might be mind-boggling to some and troublesome for most is that when arasak.com hijacks Google Chrome it does not physically set a specific page or set of pages to open on startup. Removing arasak.com from your home page cannot be done by accessing Google Chrome’s settings. However, you may be able to uninstall and reinstall Google Chrome although this won’t actually remove the malware from your computer.

The arasak.com redirect virus compromises a computer by deceiving their victims. The infection will initially trick their victims into downloading a malicious file that may be promoted as something it is not, such as a game, Google Chrome itself, flash player, or something else.

Once the malicious file is on the computer random processes will begin to run in Windows Task Manager such as game.exe or search.exe. Ending the random processes and deleting the malicious file will not remove arasak.com from your home page, but it is a good idea to do this anyway.
There are several solutions to remove arasak.com from your startup page and malware that hijacked your browser. I’ve listed instructions to remove arasak.com and malicious files from your computer using reputable Antivirus software below. If you find that these instructions were not helpful please let us know in the comments below.
Step 1: Scan your computer with Malwarebytes
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
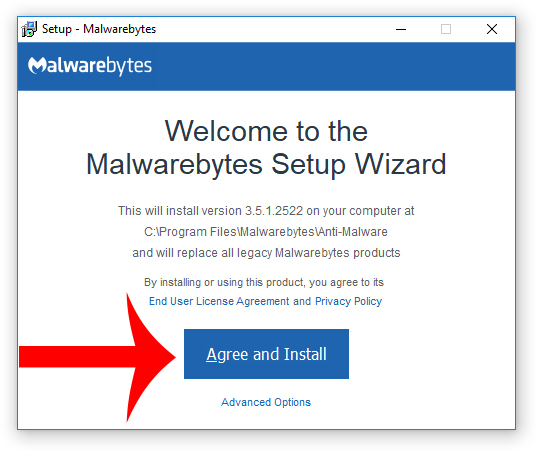
3. Choose if this is for home or work use and click Agree and Install to begin installing Malwarebytes. Once the installation is complete, click Finish.

4. Once Malwarebytes is installed, open the program and click the Scan Now button on the dashboard – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
Step 2: Scan your computer with HitmanPro
1. Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files. A second-opinion scan is important when removing malware and malicious files from your computer.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
3. Once HitmanPro is installed, open the program and click Next to start scanning your computer. *If you are using the free version you may choose to create a copy or perform a one-time scan.
4. When the HitmanPro scan is complete, click the Next button.
5. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
6. Click the Reboot button.
Step 3: Uninstall and reinstall your browser
1. Right-click the Start Menu and go to Apps and Features.
2. Find your browser such as Google Chrome in the list of installed programs, click the program with your mouse, and click the Uninstall button.
3. Reinstall your internet browser from the developer’s webpage.
Step 4: Take steps to secure your computer
Consider these best practices to ensure that your computer is secure from cyber threats like this in the future.
Use Antivirus with real-time protection
Using an Antivirus program with real-time protection can stop emerging threats and hackers from gaining access to your computer or mobile device. Antivirus programs can remove malicious files that are already on your computer, prevent your programs from being used against you, protect you from malicious websites, and stop known and unknown ransomware attacks.
Recommendations:
- Malwarebytes (Malwarebytes is an Antimalware program that can be used alongside Antivirus programs)
- Norton Security Deluxe
- AVG Internet Security Unlimited
Use a VPN
Using a VPN creates a private tunnel to keep the eyes of eavesdroppers and hackers away from your private data while you browse the web. With a VPN, you become anonymous and no one can determine who you are. Your data is encrypted and your web activity cannot be tracked.
Recommendations:
Ignore email messages from people you don’t recognize
Ignore email messages from people you do not recognize or are not expecting a message from to avoid malware from spreading onto your computer or mobile device. Email messages often contain malicious links and attachments that can be harmful to your computer. In fact, email spam is one of the most common ways that malware is spread.
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.












