RegUtilities
Learn what RegUtilities is and how to remove it from your computer. Also, remove associated viruses and malware with free our instructions.
What is RegUtilities?
RegUtilities by Tuneup System Software Pvt Ltd. is a potentially unwanted program (PUP) and scareware that is promoted as an optimization and cleaning program for the Windows Operating System. RegUtilities claims to scan your PC for system issues, activex issues, user issues, and third-party issues.

Although RegUtilities might seem like a helpful program, it is misleading and malicious. RegUtilities will scan your computer and show you specific results that it claims will make your PC unhealthy; However, RegUtilities will claim that safe programs will cause harm to your computer.
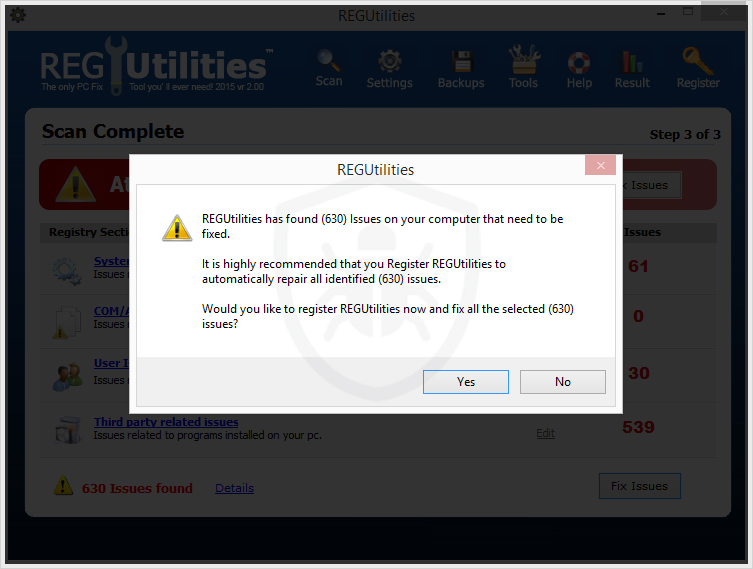
The RegUtilities scan results will claim to have found a very large amount of issues. It will claim that it is highly recommended to register RegUtilities to automatically repair all identified issues. In order to fix the issues you must pay monthly for a subscription. RegUtilities will not fix the issues it finds unless you purcahse a key to register (activate) the program.
To make matters worse, RegUtilities is known to bundle with other unwanted programs, adware, spyware, and malware that can cause additional issues. Cooperating threats that the program bundles with can establish a connection to remote sites in order to track your data, display advertisements while you browse the web or on Windows desktop, and modify your browser and computer settings to show you sponsored search results.
Another concern with RegUtilities is that it is advertised on websites that usually display malicious advertisements and host malware. If you found RegUtilities installed on your computer or notice advertisements for the program while you browse the web it is likely that your computer was introduced to other threats such as SMPlayer. Other threats should be eliminated immediately before they put your personal information and computer functionality at risk.
How is RegUtilities distributed?
RegUtilities utilizes aggressive and deceptive marketing tactics in order to persuade you to install it. Advertisements that promote RegUtilities might claim that the program is necessary to trick you to download and install it.
If you come across an advertisements promoting RegUtilities you can chose to manually and voluntarily download and install RegUtilities. If you download and install RegUtilities via an advertisement it can cause the program to bundle with other unknown programs.
Furthermore, if you download and install other freeware that is not RegUtilities you might be given the option to install RegUtilities during the setup process. Freeware download managers often offer RegUtilities as a custom or advanced installation option and give you a chance to accept or decline to install RegUtilities and other programs. If you do not opt out from installing the program it will begin to install in the background while you install said freeware. The way that the custom installation is presented can also be complex and arranged to trap you into installing programs you chose not to install. It’s advised to be alert when installing free programs from the internet and to keep an eye out for custom installation presentations to avoid any confusion and security risks from reaching your computer.
How to remove RegUtilities
Scan your computer for malware
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, click the file you just downloaded. It can usually be located in the Download folder.
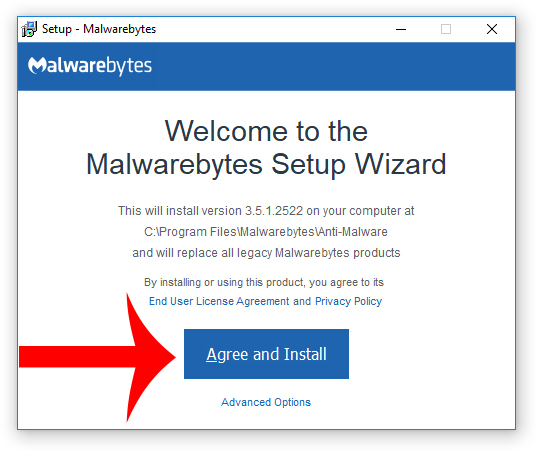
3. A window that says “Welcome to the Malwarebytes Setup Wizard” will appear. Click Agree and Install to begin the installation. Once complete, click Finish.

4. Now the Malwarebytes is installed, open the program and click the Scan Now button – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Next, Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files.
8. Once installed, open HitmanPro and click Next to start scanning your computer. *If you are using the free version you may chose to create a copy or perform a one-time scan.
9. When the HitmanPro scan is complete click the Next button.
10. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
11. Click the Reboot button.
Uninstall RegUtilities from your computer
1. On most versions of the Windows Operating System, right click the start menu (bottom left corner of the task bar) and go to Apps and Features.

2. Find RegUtilities in the list of installed programs, click it with your mouse, and click the Uninstall button that appears to uninstall RegUtilities.
How to stay protected against future infections
 The key to staying protected against future infections is to follow specific guidelines while you use your computer and to take advantage of reputable Antivirus and Anti-Malware security software that have real-time protection.
The key to staying protected against future infections is to follow specific guidelines while you use your computer and to take advantage of reputable Antivirus and Anti-Malware security software that have real-time protection.Real-time protection
Security software like Malwarebytes and Norton Security have real-time potection features that can block malicious files before they get onto your computer. The two programs bundled together can establish a wall between your computer and cyber criminals in real-time; disallowing threats and hackers from getting onto your machine.
Guidelines
The guidelines listed below are a great way to help you maintain a safe environment and ensure that the files on your computer are intact.
- Backup your computer and personal files to an external drive or online backup service
- Create a restore point on your computer in case you need to restore your computer to a date before infection
- Avoid downloading and installing apps, browser extensions, and programs you are not familiar with
- Avoid downloading and installing apps, browser extensions, and programs from websites you are not familiar with – some websites use their own download manager to bundle additional programs with the initial download
- Avoid visiting fake “spyware removal” blogs and websites that promote “spyware removal software.” These are usually malicious websites designed to phish your personal information, infect your computer with a rogue program and trick you into paying for rogue “spyware removal software.”
- If you plan to download and install freeware, open source software, or shareware make sure to be alert when you install the object and read all the instructions presented by the download manager
- Avoid torrents and P2P clients
- Do not open email messages from senders you do not know
What is Reimage? Has it been removed from my computer?
Reimage is a potentially unwanted program (PUP). You can use the free version of Malwarebytes I just replied to you about to remove it.
Is there a legit free malware program?
There is a legit free Antimalware program. I recommend the free version of Malwarebytes (not talking about free trial, actual free version). It does not have real-time protection like the full version which you must purchase but it does have a powerful scanner and will remove the same amount of malware as the full version: https://www.malwarebytes.com/mwb-download/