
Sextortion email scams are not original and new ones appear just about every day. With that in mind, one of the newest sextortion email scams is one that allegedly sends you an email from your own email address that says someone has recorded you satisfying yourself through the camera on your device.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
The subject of the email is ‘High danger. Your account was attacked‘ and the email message appears to be sent to your past or current password (or tyg or yg – since they often produce mistakes) from your own email account; However, the email message was not actually sent from your account. A third-party email spoofing service was just to make it appear this way.
If you are unfamiliar with what email spoofing is, let’s put it this way. You can basically use a service or visit a website to send anyone an email message from any email address without actually having access to the email account you want the message to be sent from. An example of an email spoofing service is Anonymizer, but there are a lot more.
The bad thing about receiving a sextortion email message is that it is usually a sign that your information was leaked somewhere online following a breach that occurred somewhere like Adobe, Myspace, or Yahoo. Your information such as email address, password, and possibly your telephone number obtained after a breach and the email scammer is using your information to scare you into paying them a certain amount of Bitcoin (don’t pay them though, you’re not in danger).
Here’s an example of the email message:
High danger. Your account was attacked.
From: [Your email address]
To: tygHi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your acc: On moment of crack [Your email address] password: tygYou say: this is my, but old password!
Or: I will change my password at any time!Of course! You will be right,
but the fact is that when you change the password, my malicious code every time saved a new one!I’ve been watching you for a few months now.
But the fact is that you were infected with malware through an adult site that you visited.If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.I also have access to all your contacts and all your correspondence from e-mail and messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.If you want to prevent this, transfer the amount of $774 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1KeCBKUgQDyyMpaXhfpRi2qUvyrjcsT44o
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.If I find that you have shared this message with someone else, the video will be immediately distributed.
Bye!
As you can see, the email message might be somewhat frightening. But it’s nothing to fear. It’s just a scam designed to cause you to panic. Even if you have never watched a video, you will still receive the same email message and even if your device does not have a camera or microphone, you’ll still receive it.
Scan your computer for malware
The email message fraudulently claims to have infected your computer with malware even though that’s not true. I still recommend to scan and remove malicious files from your computer to ensure that your device is clean, especially before changing your password.
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
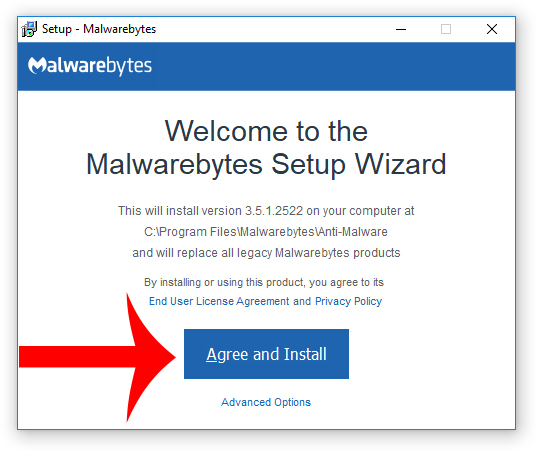
3. Choose if this is for home or work use and click Agree and Install to begin installing Malwarebytes. Once the installation is complete, click Finish.

4. Once Malwarebytes is installed, open the program and click the Scan Now button on the dashboard – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files. A second-opinion scan is important when removing malware and malicious files from your computer.
8. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
9. Once HitmanPro is installed, open the program and click Next to start scanning your computer. *If you are using the free version you may choose to create a copy or perform a one-time scan.
10. When the HitmanPro scan is complete, click the Next button.
11. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
12. Click the Reboot button.
Change your password
As previously mentioned, your email address and password were leaked somewhere online so change the password to your email account and wherever else you reused the password to ensure your privacy and safety. Here are some tips for making a secure new password:
- Do not reuse the same password for multiple accounts. Use unique passwords wherever possible.
- Use strong passwords with numbers, letters, and special characters such as !@$#.
- Use two-factor authentication to add an extra layer of security along with your password.
- Use a reputable password manager if you have trouble remembering multiple passwords.
- Sextortion Scam Spoofs Your Email Address And Demands $800 In Bitcoin
- cPanel Scam Emails Target Website Owners After CVE-2026-41940 Emergency Patches
- Reserve Credit Card Scam Uses Fake Visa Card Offer To Steal Your Money
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.












