
A sextortion email scam sends you an email from your own account, shows you your password, and claims a spyware developer hacked your account.
There seems to be a new sextortion email scam campaign every week. The latest sextortion email scam campaign sends you an email from your own address, shows you your past or current password, and says that your account was hacked by a spyware software developer.

The email message claims that the hacking was carried out by using “a hardware vulnerability through which you went online (Cisco router, vulnerability CVE-2018-0296).”
The email claims that the hacker went around the security system in the router and installed an exploit there. When you went online the exploit downloaded a malicious code (rootkit) to your device.
Furthermore, the email claims that the hacker has been following you and can see absolutely everything that you do. The hacker claims that they can view and download your files and all of your data and have saved all your messages and history of the sites you visit.
The alleged hacker also claims to have access to the camera on your device. The email says that they take photos and videos of you.
The scammer sent the email to you in order to scare you into paying them in Bitcoin. The email says that they have “harvested solid dirt on you” and they have taken photos and videos of your “most passionate fun with adult content.”
The email further states that if you do not pay them in 48 hours they will send photos, videos, and all your data to all of your contacts.
Don’t be alarmed though. This is just another sextortion email scam that has been in circulation. Do not pay the scammer because they have not accessed your email account, they have not taken photos and videos of you, they do not have your data, and there is no real threat.
The email can be frightening because it shows the past or current password to your email account and the message appears to be sent to you from your own account; However, the email was not sent from your own account. A third-party email spoofing service was used and this can be proven by the IP address used to send the email.
Email message campaigns like this are becoming popular following breaches that occurred on websites like LinkedIn and Adobe. They use information leaked about you against you in order to attempt to blackmail you. To see where your email information may have been leaked from check out https://haveibeenpwned.com/. You can input your email address to locate where your information was leaked.
Here’s what is written in the email message:
Subject: Hacking Alert! You account was hacked (your password:[password])
From [email]
To [password]Dear user of [email server]!
I am a spyware software developer.
Your account has been hacked by me in the summer of 2018.I understand that it is hard to believe, but here is my evidence:
– I sent you this email from your account.
– Password from account [email]: [password] (on moment of hack).The hacking was carried out using a hardware vulnerability through which you went online (Cisco router, vulnerability CVE-2018-0296).
I went around the security system in the router, installed an exploit there.
When you went online, my exploit downloaded my malicious code (rootkit) to your device.
This is driver software, I constantly updated it, so your antivirus is silent all time.Since then I have been following you (I can connect to your device via the VNC protocol).
That is, I can see absolutely everything that you do, view and download your files and any data to yourself.
I also have access to the camera on your device, and I periodically take photos and videos with you.At the moment, I have harvested a solid dirt… on you…
I saved all your email and chats from your messangers. I also saved the entire history of the sites you visit.I note that it is useless to change the passwords. My malware update passwords from your accounts every times.
I know what you like hard funs (adult sites).
Oh, yes .. I’m know your secret life, which you are hiding from everyone.
Oh my God, what are your like… I saw THIS … Oh, you dirty naughty person … 🙂I took photos and videos of your most passionate funs with adult content, and synchronized them in real time with the image of your camera.
Believe it turned out very high quality!So, to the business!
I’m sure you don’t want to show these files and visiting history to all your contacts.Transfer $871 to my Bitcoin cryptocurrency wallet: 1Bt4psBJmjfVTcW6eYiJZ6HEbpFgKkBSX4
Just copy and paste the wallet number when transferring.
If you do not know how to do this – ask Google.My system automatically recognizes the translation.
As soon as the specified amount is received, all your data will be destroyed from my server, and the rootkit will be automatically removed from your system.
Do not worry, I really will delete everything, since I am “working” with many people who have fallen into your position.
You will only have to inform your provider about the vulnerabilities in the router so that other hackers will not use it.Since opening this letter you have 48 hours.
If funds not will be received, after the specified time has elapsed, the disk of your device will be formatted,
and from my server will automatically send email and sms to all your contacts with compromising material.I advise you to remain prudent and not engage in nonsense (all files on my server).
Good luck!
As you can see, the email can appear legitimate to many people. But, the same exact message has been sent around the internet to many people and there have been many campaigns like it in the past. For example, a previous email claims that a hacker cracked your email account. If you have never visited an adult website, you will still receive the same message. If your device does not have a camera, they will still claim to have recorded you through your camera.
In conclusion, do not pay BTC to the scammer and do not reply to the fraudulent email message. The only thing you need to do is change the password to your email address and other accounts you have for safe measure.
The email message does not mean that your computer is infected with malware; However, if you would like to scan your computer for malware and other potentially malicious files from your computer we recommended to use Malwarebytes. Here are some instructions to do so:
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, click the file you just downloaded. It can usually be located in the Download folder.
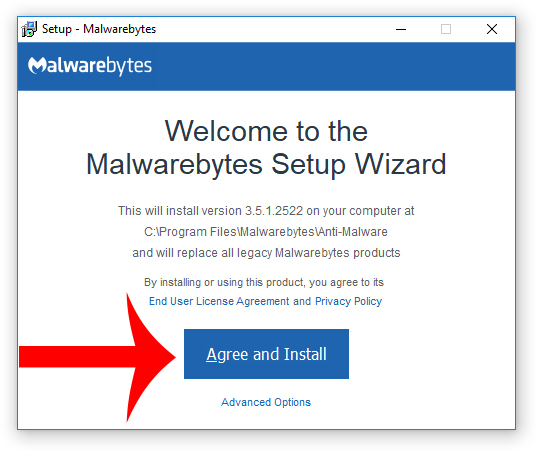
3. A window that says “Welcome to the Malwarebytes Setup Wizard” will appear. Click Agree and Install to begin the installation. Once complete, click Finish.

4. Now the Malwarebytes is installed, open the program and click the Scan Now button – or go to the Scan tab and click the Start Scan button.

3. When the scan is complete click the Quarantine Selected button.
4. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
- OneDrive Email Scam: How It Works, Warning Signs, and How to Stay Protected
- Women and Children Support Foundation Email Scam Promises Fake $1 Million Donation
WordPress Bot Protection
Bot Blocker for WordPress
Monitor bot traffic, review live activity, and control AI crawlers, scrapers, scanners, spam bots, and fake trusted bots from one clean WordPress dashboard.
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.








21 Comments
This is fraud / scam persons…Do not send BITCOIN this idiot peoples…
In fact, they do not hack your computer.
This is caused by you use cheap hosting.
This hackers offer cheap hosting, when you generate email / password on hosting panel, as administrator this fraud / scam peoples can see all.
Because such kind emais you receive only to an email adres related with a domain ( example : xxxx@mysitecom ).
You have also emails from YAHOO, GMAIL, HOTMAIL etc, you never receive those stories into inbox of those free email accounts…
This is indicating that your computer is not hacked by a malware while you watch porno.
If you someone never watch porno, you can just laugh and do not send money ( BITCOIN ),
But you must urgently change your hosting of your web page(s),
– Change password of your email account(s), use different password for each email if you have several.
– Never use same password for loggin CPANEL, email account, GOOGLE webmaster accounts etc…
– Since my email password and WEBMASTER account password was same, they logged into webmaster account…Luckly GOOGLE blocked them…I unblocked with SMS code verification…
– Use always different password for each platform ( Youtube, Gmail, Twitter, Facebook etc )
– Host your hosting on big hosting companies ( GODADDY, BLUE HOST, etc ) where staff can never log into your CPANEL / admin area. Those cheap scam hosting owners uses ” RESELLER HOSTING ” therefore they can log into your CPANEL, too as administrator.
I immediately filed a complaint at the FBI website. They ask for a copy of the email message, including headers. I may have over reacted and perhaps the FBI is having a good laugh at me for taking this so seriously, but maybe my information will help them track this scum down, for the sake of those poor fools who actually paid.
Just like to say thanks for all comments – for an oldie like me was nearly fooled for the this one – too many things were nearly there ! – now if he’d asked for £20 I may have fallen for it – but bite coins what are those and how to pay?? But password changed and run a full cheque thu the system.
Much appreciated, getting an email from myself with a mention of a previous password,threw me off balance.On reflection,why would I end up in the spam folder? Once again,thank you 🙂
Had this email yesterday, i suffer from anxiety so i had a pretty rough time when i first read it, even gave actionfraud a call, they told me more or less the same as what you’ve said here. This has been sent to many, many people and its nothing to worry about. Just scare tactics
Freaked me out a little because it was a password that I actually have used in the past. Did a little investigation and found I still was using on some current accounts including PayPal!! Email would not have matched but if someone knew the email address I use for PayPal and used that password they would have had a heyday! Thank goodness I have LastPass.
Dear
I have received the same email on today at 17:05 but I saw that the date of sent mail is tomorrow 16th.
Am I in dangerous more than others?
I am sorry. But I am so worried
Rest assured,read the article fully.Mine expires today.Seeing what Sean has stated is reassuring enough. Like me,you’ll be just fine xx
Thank you so much
I have been getting this email. The first time I laughed out loud. The password was just a random number bearing no resemblance to any password I have ever used. The Nigerian prince’s grasp of English grammar and ability to spell was far superior. This is south an amateur job only a fool would be suckered by it.
Here’s how to handle it: delete the email when it comes in.
Our company has received this email, however the email has been sent from our own info@ email address. And any replies to the email come to our mailbox. Should I be more concerned?
Nothing to be concerned about. This was sent to my elderly disabled mother who doesn’t have any sort of webcam and certainly does not visit any porn sites. Just fishing for cash
No.
recu à l’instant …
Dear user of orange.fr!
I am a spyware software developer.
Your account has been hacked by me in the summer of 2018.
I understand that it is hard to believe, but here is my evidence:
– I sent you this email from your account.
– Password from account corinne.eck@orange.fr: nh77jk (on moment of hack).
The hacking was carried out using a hardware vulnerability through which you went online (Cisco router, vulnerability CVE-2018-0296).
I went around the security system in the router, installed an exploit there.
When you went online, my exploit downloaded my malicious code (rootkit) to your device.
This is driver software, I constantly updated it, so your antivirus is silent all time.
Since then I have been following you (I can connect to your device via the VNC protocol).
That is, I can see absolutely everything that you do, view and download your files and any data to yourself.
I also have access to the camera on your device, and I periodically take photos and videos with you.
At the moment, I have harvested a solid dirt… on you…
I saved all your email and chats from your messangers. I also saved the entire history of the sites you visit.
I note that it is useless to change the passwords. My malware update passwords from your accounts every times.
I know what you like hard funs (adult sites).
Oh, yes .. I’m know your secret life, which you are hiding from everyone.
Oh my God, what are your like… I saw THIS … Oh, you dirty naughty person … 🙂
I took photos and videos of your most passionate funs with adult content, and synchronized them in real time with the image of your camera.
Believe it turned out very high quality!
So, to the business!
I’m sure you don’t want to show these files and visiting history to all your contacts.
Transfer $867 to my Bitcoin cryptocurrency wallet: 1ARbihuSkEAojNHgxsgFVKjTJDHXuimB8
Just copy and paste the wallet number when transferring.
If you do not know how to do this – ask Google.
My system automatically recognizes the translation.
As soon as the specified amount is received, all your data will be destroyed from my server, and the rootkit will be automatically removed from your system.
Do not worry, I really will delete everything, since I am ‘working’ with many people who have fallen into your position.
You will only have to inform your provider about the vulnerabilities in the router so that other hackers will not use it.
Since opening this letter you have 48 hours.
If funds not will be received, after the specified time has elapsed, the disk of your device will be formatted,
and from my server will automatically send email and sms to all your contacts with compromising material.
I advise you to remain prudent and not engage in nonsense (all files on my server).
Good luck!
I’ve got this E-mail too, thanks for all the information! Went to the website and got this message:
Good news — no pwnage found!
No breached accounts and no pastes (subscribe to search sensitive breaches)
That looks nice, but I do not know where this mail come from or how I can make the password leak stop, do you have more ideas besides chanign my passwords (that I will do!)
Thanks for all the work!
Ah, yes, like you say, there’s no reason to be alarmed.
BUT how come they know and can give some old password you’ve used??
They must’ve harvested this from somewhere that you’ve logged into using this (somewhere, where they save your password in ascii format!)
As mentioned, the information was obtained after a breach of a third-party site or service such as LinkedIn or Adobe. You can enter your email here: https://haveibeenpwned.com/ to see where the information may have been compromised.
Hi I have received this email and my email passwords have been changed, I don’t think they have hacked my computer but I am sure they have hacked my hosting account.
No one has hacked you. If you want to find out where your email account information was breached or leaked go here: https://haveibeenpwned.com/
Thanks for your article. I believe there may be a second level to the scam and that aspect has not yet been recognized. All these scam emails request payment in Bitcoin. The email has an ID for a Bitcoin wallet and each email has a different ID. If you Google that ID, it comes up with quite a few sites that claim the ID is the name of a virus and they can remove it for you. I do not check any of these sites as I believe they are fake and are intended to infect a PC with their own virus. I have not seen anybody write about this, so many people may have been caught
I recognize those sites. They’re scam sites that usually copy from other peoples sites (like this one) but change things a bit. They claim the wallet ID is a virus in order to trick people into downloading rogue security software that won’t actually help. The malicious security software will only scan the computer then insist that the user purchase a subscription to remove threats.