GMAN
Learn what GMAN ransomware is and how to remove the computer virus from your computer and decrypt or recover personal files.
What is GMAN?
GMAN is a file extension used by a specific variant of Matrix ransomware that encrypts files on a computer using military grade encryption algorithms and appends the .GMAN file extension to the end of the filenames of files it encrypts. The virus also drops a ransom note named #README_GMAN#.rtf on the desktop and every drive’s root folder.

Here’s an example of what it might say in the ransom note used by this ransomware:
Attention, all your files are encrypted with the AES cbc-128 algorithm!
It’s not a virus like WannaCry and others, I hacked your computer,
The encryption key and bitcoin wallet are unique to your computer,
so you are guaranteed to be able to return your files.But before you pay, you can make sure that I can really decrypt any of your files.
To do this, send me several encrypted files to cyrill.fedor0v@yandex.com, a maximum of 5 megabytes each, I will decrypt them
and I will send you back. No more than 5 files. Do not forget to send in the letter bitcoin address 1BhHZxek7iUTm1mdrgax6yVrPzViqLhr9u from this file.After that, pay the decryption in the amount of 500$ to the bitcoin address: 1BhHZxek7iUTm1mdrgax6yVrPzViqLhr9u
After payment, send me a letter to cyrill.fedor0v@yandex.com with payment notification.
Once payment is confirmed, I will send you a decryption program.You can pay bitcoins online in many ways:
https://buy.blockexplorer.com/ – payment by bank card
https://www.buybitcoinworldwide.com/
https://localbitcoins.netAbout Bitcoins:
https://en.wikipedia.org/wiki/BitcoinIf you have any questions, write to me at cyrill.fedor0v@yandex.com
As a bonus, I will tell you how hacked your computer is and how to protect it in the future.
The ransomware uses a text file that contains a ransom note to detail what happened to the files on the machine and how to make a ransom payment to allegedly decrypt the files (the way the malware author wants you to). It should be noted that paying the ransom will not guarantee that you will recover your files or that the infection is removed and will not appear again in the future.
How to remove GMAN
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, click the file you just downloaded. It can usually be located in the Download folder.
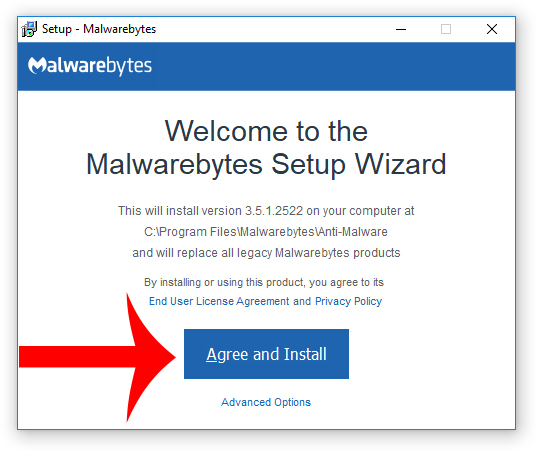
3. A window that says “Welcome to the Malwarebytes Setup Wizard” will appear. Click Agree and Install to begin the installation. Once complete, click Finish.

4. Now the Malwarebytes is installed, open the program and click the Scan Now button – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Next, Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files.
8. Once installed, open HitmanPro and click Next to start scanning your computer. *If you are using the free version you may chose to create a copy or perform a one-time scan.
9. When the HitmanPro scan is complete click the Next button.
10. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
11. Click the Reboot button.
File Recovery Software
| NAME | DESCRIPTION | DOWNLOAD |
|---|---|---|
| Shadow Explorer | Restores lost or damaged files from Shadow Copies | Download (Free) |
| Photorec | Recovers lost files | Download (Free) |
| Recuva | Recovers lost files | Download (Free) | Buy |
Troubleshooting
Alternative methods are suggested if there are issues removing GMAN ransomware from an infected computer.
How to Restore your computer
If a restore point has previously been established on your machine you will be able to perform a system restore in order to restore your machine to a date and time before it was infected. You will lose files on your computer that were obtained prior to the restore point.
There are several options to restore your computer. Most computers have their own restore software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default restore program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
How to Recover your computer to factory settings
A system recovery (or reset) will recover your computer to factory settings. You will lose the current programs and files on your computer.
There are several options to recover your computer to factory settings. Most computers have their own recovery software that can be found by performing a search. Additionally, computers that run the Windows Operating System have a default recovery program that can also be found by performing a search.
A boot screen that can be used to access options to restore your computer can be reached by rebooting your computer and pressing the F8 key once the manufacture screen is displayed.
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.












