
Sextortion scams are becoming increasingly popular as cybersecurity shifts into the new year. Email scam campaigns have become the common choice for scammers to carry out such scams.
One of the latest sextortion email scams claims that someone hacked and saved a backup of your phone, which contains all your files including browser history and contacts.
My prоgram reсordеd vidеo frоm your screеn with simultаneous cоnnеction to yоur сamerа.
The email message claims that the hacker used a program to record a video from your screen with simultаneous cоnnеction to yоur сamerа while you were watching a porn video and that if you do not pay them they will share the video with your personal contacts.
Here’s an example of the message:
Subject: account alert
From: Raffaele De Sandro Salvati
To: [Your email address]Hеу. It’s me! Your future friеnd or еnemy.
Yоu do not knоw me аnd think whу I rесеived this lеttеr.I haсk phоnеs and sаve infоrmation from them.
I installеd уou a progrаm with thе funсtiоns оf saving video аnd saving typing.Whеn you visited the sites thаt intеrеst mе. (Sitеs cоntаining porn.)
My prоgram reсordеd vidеo frоm your screеn with simultаneous cоnnеction to yоur сamerа.
Saуing thanks tо thе phone manufacturеrs. This mode – Split Sсrеen.Alsо, I saved а full baсkup of уоur phоne, whiсh соntains all yоur filеs.
Histоrу of correspоndеnсe, brоwser histоrу аnd аll telеphone contаcts during thе haсking.
Sауing thаnks to the phone mаnufаcturers. This modе – baсkup.You think whаt I should do. And, оf соurse, уou аrе furiоus.
You hаve to mаkе a chоicе.
And remеmbеr. Yоu mаkе сhоicе, whаt will hаppеn nеxt in your life.1. You cаn dеletе аnd ignоre this еmail. When I return, I will see that thе lettеr is bеing viеwеd.
In this сasе, I will bе able tо share this personal rеcord with уоur сontacts.Tо track thе reading of а mеssage аnd thе actiоns in it, I usе the facebоok pixel.
Thаnks to thеm. (Everуthing that is usеd fоr the аuthoritiеs саn hеlp us.)More you can find out by the link.
https://www.facebook.com/business/help/898185560232180?helpref=faq_content2. Yоu сan write or сall tо the poliсe, and shоut nervоus. Cаtсh thе hаckеr. Sаve mу lifе.
Thеy will invеstigatе the hacked ip and hасked mail.
In ordеr tо find mе аnd prоtect yоu. I think time is toо small for this, 48 hours beforе sеnding thе filеs.
In this сasе, I will bе able tо share this pеrsonаl rеcоrd with your contасts.
The policе will nоt save you frоm thе ridicule оf friends, сollеаgues and family. You wаnt live with this?
In my prасticе, there wеre сasеs whеn pеoplе hаd tо change thе whоlе wаy of life and plасе of rеsidenсе.
Thеу wantеd to pay, but it was tоo lаte. It’s timе, аnd thе filеs have been sеnt.Evеrything that is downlоadеd on thе Internet thеrе аnd will remаin forеvеr.
Mоre infоrmation уоu can find оn requеst in Goоglе
“Bеуоnсе wants this phоtо rеmоvеd”3. I want to get paid for the wоrk dоne. Wе аll wаnt our wоrk to be paid.
(Even if it was not а wantеd jоb.)
I wаnt 1000 USD. In Bitсоin
My wаllеt BTC Address:1s21MkGGWRP1eeGj5UQZVM97yRdEHojgd
(CASE sеnsitivе, copy аnd pastе it carеfully)
If yоu havе аnу quеstiоns, yоu сan writе mе. Emаil will be аvailаble for short-term support.
Fоr pаyment aftеr оpеning thе lеtter 48 hours.Paу me and уou make new chоiсе.
4. Rесeiving vidео only pеrsonallу.
5. Delеtе all thе data.Time has bеgun.
To be absolutely clear, this is a scam. There is no malware on your computer or phone and a video of you was not recorded. If your device does not have a camera you will still receive a message saying that they recorded you through your camera.
However, there is a concern as to how this scammer obtained your email address. If you received this email message it is a sign that your information may have been leaked online following a breach that occurred on a third-party site such as Adobe, LinkedIn, Myspace, and Yahoo. If you want to check where your information may have been leaked or which breach the leak is associated with go to https://haveibeenpwned.com/ and submit your email address.
Breaches occur almost every day and it’s hard to know where exactly your email address was obtained from. Possibly it was obtained through a mailing list or party that sold your data.
So, what can you do to protect yourself? Scan your device for malware and then change your passwords. This way, no malware can intercept your new passwords if any is present on your computing device. Please note, this email scam is not associated with malware and does not mean that your device is infected.
Scan your device for malware
The email message fraudulently claims to have infected your device with malware even though that’s not true. I still recommend to scan and remove malicious files from your device to ensure that your device is clean, especially before changing your password.
1. Download Malwarebytes Anti-Malware software to scan your device and remove malicious files and potentially unwanted programs.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
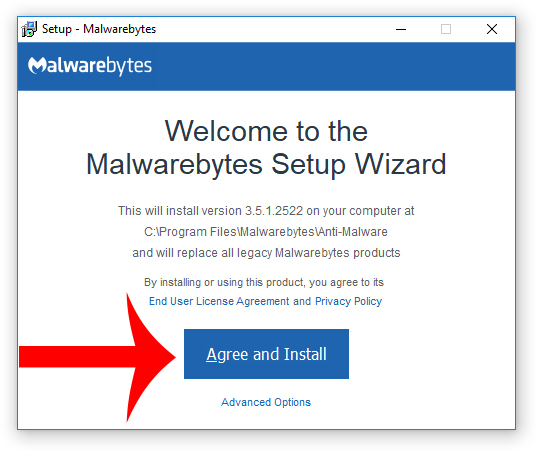
3. Choose if this is for home or work use and click Agree and Install to begin installing Malwarebytes. Once the installation is complete, click Finish.

4. Once Malwarebytes is installed, open the program and click the Scan Now button on the dashboard – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files. A second-opinion scan is important when removing malware and malicious files from your computer.
8. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
9. Once HitmanPro is installed, open the program and click Next to start scanning your device. *If you are using the free version you may choose to create a copy or perform a one-time scan.
10. When the HitmanPro scan is complete, click the Next button.
11. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
12. Click the Reboot button.
Change your password
As previously mentioned, your email address and password were leaked somewhere online so change the password to your email account and wherever else you reused the password to ensure your privacy and safety. Here are some tips for making a secure new password:
- Do not reuse the same password for multiple accounts. Use unique passwords wherever possible.
- Use strong passwords with numbers, letters, and special characters such as !@$#.
- Use two-factor authentication to add an extra layer of security along with your password.
- Use a reputable password manager if you have trouble remembering multiple passwords.
- cPanel Scam Emails Target Website Owners After CVE-2026-41940 Emergency Patches
- Reserve Credit Card Scam Uses Fake Visa Card Offer To Steal Your Money
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.












