
An email message claims that someone has access to your system. The email message says that someone hacked your device, obtained access to all of your accounts (including your email account), and installed a virus on your device through an exploit while you were watching a video.
The message then claims that the alleged hacker was able to gain remote control of your system which gave them access to your microphone and webcam. With access to your webcam, the hacker was able to record you doing inappropriate things while you were watching an online video.
To make matters worse, the email message appears to be sent to you from your own email account which suggests that the hacker does have access to your account.
Furthermore, the email message contains the current or past password you use to access your email account.
However, do not be alarmed because the message is just a scam. No one was able to access your email account (a third-party email spoofing service was used to send you an email message that appears to be sent from your own account), there is not malware on your system (native to the email message), and there is no video of you ‘doing inappropriate things.’
The purpose of this scam is to scare you into making a payment to the scammer in Bitcoin. The email message says that if you do not pay them in 48 hours they will send the video of you to your contacts including your family members, colleagues and more.
Here’s an example of the email message:
Subject: Security Notice. Someone have access to you system.
From: [Your email address]
To: [Your password]I’ll begin with the most important.
I hacked your device and then got access to all your accounts… Including [Your email address].
It is easy to check – I wrote you this email from your account.
Also I have an old password for the hacking day: [Your password]Moreover, I know your intim secret, and I have proof of this.
You do not know me personally, and no one paid me to check you.It is just a coincidence that I discovered your mistake.
In fact, I posted a malicious code (exploit) to an adult site, and you visited this site…While watching a video Trojan virus has been installed on your device through an exploit.
This darknet software working as RDP (remote-controlled desktop), which has a keylogger,
which gave me access to your microphone and webcam.
Soon after, my software received all your contacts from your messenger, social network and email.At that moment I spent much more time than I should have. I studied your love life and created a good video series.
The first part shows the video that you watched,
and the second part shows the video clip taken from your webcam (you are doing inappropriate things).Honestly, I want to forget all the information about you and allow you to continue your daily life.
And I will give you two suitable options. Both are easy to do.
First option: you ignore this email.
The second option: you pay me $700(USD).Let’s look at 2 options in detail.
The first option is to ignore this email.
Let me tell you what happens if you choose this path.
I will send your video to your contacts, including family members, colleagues, etc.
This does not protect you from the humiliation that you and
your family need to know when friends and family members know about your unpleasant details.The second option is to pay me. We will call this “privacy advice.”
Now let me tell you what happens if you choose this path.
Your secret is your secret. I immediately destroy the video.
You continue your life as if none of this has happened.Now you might think: “I’ll call to police!”
Undoubtedly, I have taken steps to ensure that this letter cannot be traced to me,
and it will not remain aloof from the evidence of the destruction of your daily life.
I don’t want to steal all your savings.
I just want to get compensation for my efforts that I put in to investigate you.
Let us hope that you decide to create all this in full and pay me a fee for confidentiality.
You make a Bitcoin payment (if you don’t know how to do it, just enter “how to buy bitcoins” in Google search)Shipping amount: $700(USD).
Getting Bitcoin Addresses: 1FVuyuSN41aa3JN9sn8qkuD2PmaMEMHHnc
(This is sensitive, so copy and paste it carefully)Don’t tell anyone what to use bitcoins for. The procedure for obtaining bitcoins can take several days, so do not wait.
I have a spetial code in Trojan, and now I know that you have read this letter.
You have 48 hours to pay.
If I don’t get BitCoins, I’ll send your video to your contacts, including close relatives, co-workers, and so on.
Start looking for the best excuse for friends and family before they all know.
But if I get paid, I immediately delete the video.This is a one-time offer that is non-negotiable, so do not waste my and your time.
Time is running out.Bye!
Although this email message might appear to be legitimate a be frightening to digest, rest assure that it is a common email scam and there are many like it. If your device does not have a camera on it you will still receive the same email message. If you have never viewed an online video before, you will still receive the message as well.
The downside to receiving such an email message, especially one that may show you your own password is that your information was leaked online following a breach that occurred on a website like Yahoo, Adobe, LinkedIn, and Experian. Sensitive data such as your name, email address, password, and telephone number may be floating around somewhere on the web or someone may have been able to purchase a list that obtained your information.
To see where your information may have been leaked or which breach your information was obtained from go to https://haveibeenpwned.com/ and submit your email address. You will receive a free detailed analysis instantly.
And finally, the most important things you need to do are change your passwords and scan your computer for malware. I recommend to scan your computer for malware first, then change your passwords to ensure no one is spying on you.
Here are instructions to scan and remove malware from your computer and tips to create a secure password:
Scan your computer for malware
1. Download Malwarebytes Anti-Malware software to scan your device and remove malicious files and potentially unwanted programs.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
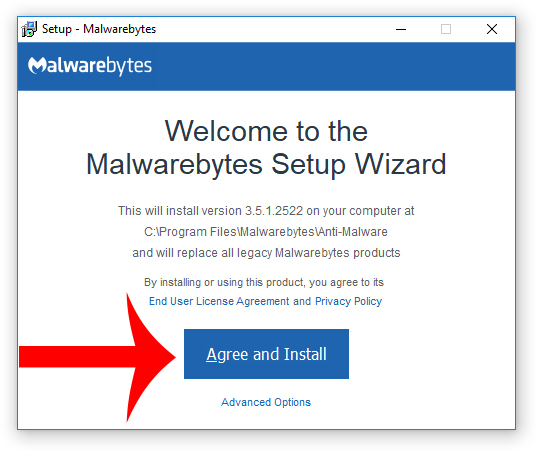
3. Choose if this is for home or work use and click Agree and Install to begin installing Malwarebytes. Once the installation is complete, click Finish.

4. Once Malwarebytes is installed, open the program and click the Scan Now button on the dashboard – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files. A second-opinion scan is important when removing malware and malicious files from your computer.
8. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
9. Once HitmanPro is installed, open the program and click Next to start scanning your device. *If you are using the free version you may choose to create a copy or perform a one-time scan.
10. When the HitmanPro scan is complete, click the Next button.
11. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
12. Click the Reboot button.
Tips to create a secure password
- Do not reuse the same password for multiple accounts. Use unique passwords wherever possible.
- Use strong passwords with numbers, letters, and special characters such as !@$#.
- Use two-factor authentication to add an extra layer of security along with your password.
- Use a reputable password manager if you have trouble remembering multiple passwords.
- cPanel Scam Emails Target Website Owners After CVE-2026-41940 Emergency Patches
- Reserve Credit Card Scam Uses Fake Visa Card Offer To Steal Your Money
- Booking.com Scam Uses Real Reservation Data to Steal Guest Payments
- Fake YouTube Copyright Scam Impersonates City of Grand Forks
- Mothers and Kids Support Forum Email Scam Promises Fake $2 Million Donation
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.












