What is DoubleLocker?
DoubleLocker is dangerous ransomware that infects Android smartphones. DoubleLocker ransomware locks your phone’s data, encrypt files, appends the .cryeye file extension to the end of files, changes the PIN to access the phone, and shows a screen-locker that says “Your personal files are encrypted!”

Once the DoubleLocker virus has encrypted files and appended the .cryeye extension it will show the ransom note. The virus uses the ransom note to explain to victims what happened and how to pay the ransom. It gives the victim 24 hours to pay 0.0130 Bitcoin (about $73.38 at this time) to decrypt their data. If the ransom is not paid, the data will remain encrypted and will not be deleted from device.
Here’s an example of the ransom note shown on the DoubleLocker lock-screen:
Current state information
Your personal documents and files on this device have just been crypted. The original files have been deleted and will only be recovered by following the steps described below. The encryption was done with a unique generated encryption key (using AES-256).
Your personal files are encrypted!
To decrypt files you need to obtain the private key. This means the encrypted files are of no use until the get decrypted using a private key stored on a server.
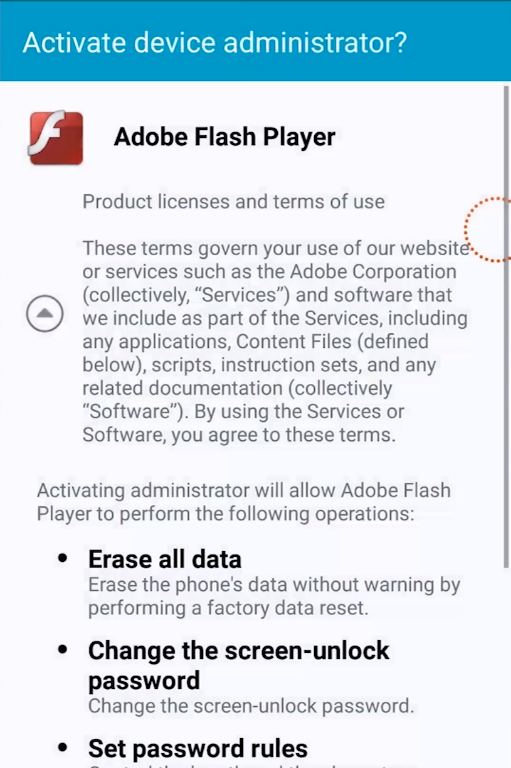
DoubleLocker ransomware is typically spread by rogue apps in Google’s Play Store. In the most recent campaign, the ransomware was spread via a fake Adobe Flash Player app bolstered by a third-party website. The app has since been removed by Google. It is important to avoid installing rogue apps or Adobe Flash Player apps of any kind (legitimate or not – you don’t need them).
This page explains how to remove DoubleLocker ransomware that appends the .cryeye extension to files and changes your phone’s PIN number.
How to remove DoubleLocker
The only realistic way to remove DoubleLocker from your Android phone is to perform a factory reset.
There is a method to get past the PIN lock without a factory reset for rooted devices. However, for the method to work, the device needed to be in the debugging mode before the ransomware got activated.
To avoid future infections it is recommended to install Malwarebytes for Mobile to protect your phone from malware, adware, and ransomware automatically.
