The most popular email scams these days are sextortion scams where a scammer claims to have recorded you through their webcam while you were visiting adult websites. The purpose of sextortion scams is to trick you into believing that a mischievous video of you will be sent to your contacts, friends, family members, and colleagues unless you send a Bitcoin payment to have the video deleted.
One of the most recent sextortion scams making rounds claims to have recorded you through your webcam while you were visiting adult websites. The email says that they created a double video where one side shows the adult video you were viewing and the other side shows you while you were watching the video.
What I’ve done?
I made a double screen video.
The first part shows the video you watched (you have good taste, yes … but strange for me and other normal people),
and the second part shows the recording of your webcam.
To make the email seem legitimate, the email message appears to be sent from your own email account and the email accounts previous or current password will be who the email is addressed to. Your password is also mentioned in the body of the email message and the message says that their malware will intercept your password every time you change it.
However, this email is just a confirmed scam so there’s nothing to be worried about. An email spoofing service like Anonymailer was used to send the email message and a trojan was not downloaded onto your computer or device. There are no videos of you visiting adult websites, your computer was not infected by this scammer’s malware, and no one has accessed your email account. You will still receive the message if you have never visited an adult website or if your device does not have a camera.
Now that you’re aware that it’s a scam, there is some bad news. Unfortunately, if you received this email message it is a possible sign that your information was leaked somewhere following a breach that occurred on websites like Adobe, LinkedIn, or Yahoo. Scammers use information leaked about you (such as your email address, email account password, and telephone number) against you in order to scare you and attempt to extort money from you.
To find out where your information may have been leaked online or which breach may have been at fault for leaking your information go to https://haveibeenpwned.com/ and submit your email address.
Transcript from the email message:
Subject: Caution! Attack hackers to your account! From: [Your email address] To: [Your password] Hi, stranger! I know the [Your password], this is your password, and I sent you this message from your account. If you have already changed your password, my malware will be intercepts it every time. You may not know me, and you are most likely wondering why you are receiving this email, right? In fact, I posted a malicious program on adults (pornography) of some websites, and you know that you visited these websites to enjoy (you know what I mean). While you were watching video clips, my trojan started working as a RDP (remote desktop) with a keylogger that gave me access to your screen as well as a webcam. Immediately after this, my program gathered all your contacts from messenger, social networks, and also by e-mail. What I've done? I made a double screen video. The first part shows the video you watched (you have good taste, yes ... but strange for me and other normal people), and the second part shows the recording of your webcam. What should you do? Well, I think $666 (USD dollars) is a fair price for our little secret. You will make a bitcoin payment (if you don't know, look for "how to buy bitcoins" on Google). BTC Address: 19rvCcYfSwPUSvJJKNyTyRFi5vxt6zaqJC (This is CASE sensitive, please copy and paste it) Remarks: You have 2 days (48 hours) to pay. (I have a special code, and at the moment I know that you have read this email). If I don't get bitcoins, I will send your video to all your contacts, including family members, colleagues, etc. However, if I am paid, I will immediately destroy the video, and my trojan will be destruct someself. If you want to get proof, answer "Yes!" and resend this letter to youself. And I will definitely send your video to your any 12 contacts. This is a non-negotiable offer, so please do not waste my personal and other people's time by replying to this email. Bye!
What can/should you do?
Change the password to your email account and wherever else you reused the password to ensure your privacy and safety. Here are some tips for making a secure new password:
- Do not reuse the same password for multiple accounts. Use unique passwords wherever possible.
- Use strong passwords with numbers, letters, and special characters such as !@$#.
- Use two-factor authentication to add an extra layer of security along with your password.
- Use a reputable password manager if you have trouble remembering multiple passwords.
Last, but not least, the email message claims to have infected your computer with malware, but that’s not true; However, this is a cybersecurity blog and if you would like to scan your computer for malware and other potentially malicious files follow these instructions:
1. Download Malwarebytes Anti-Malware software to scan your computer and remove malicious files and potentially unwanted programs.
2. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
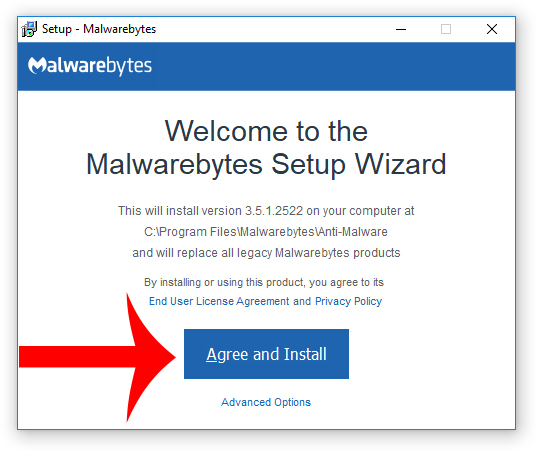
3. Choose if this is for home or work use and click Agree and Install to begin installing Malwarebytes. Once the installation is complete, click Finish.

4. Once Malwarebytes is installed, open the program and click the Scan Now button on the dashboard – or go to the Scan tab and click the Start Scan button.

5. When the scan is complete click the Quarantine Selected button.
6. If Malwarebytes says “All selected items have been removed successfully. A log file has been saved to the logs folder. Your computer needs to be restarted to complete the removal process. Would you like to restart now?” click the Yes button to restart your computer.
7. Download HitmanPro to perform a second-opinion scan and remove any remaining malicious trace files. A second-opinion scan is important when removing malware and malicious files from your computer.
8. To install the program, locate and double-click the executable file you just downloaded. The file can usually be found in the Download folder.
9. Once HitmanPro is installed, open the program and click Next to start scanning your computer. *If you are using the free version you may choose to create a copy or perform a one-time scan.
10. When the HitmanPro scan is complete, click the Next button.
11. To activate the free version of HitmanPro: enter your email address twice and click the Activate button.
12. Click the Reboot button.
- Direct Card Scam Uses Fake Visa Offer to Steal Upfront Fees
- Manus AI Has a Refund Problem, Not Just a Product Problem
- Sextortion Scam Spoofs Your Email Address And Demands $800 In Bitcoin
- cPanel Scam Emails Target Website Owners After CVE-2026-41940 Emergency Patches
- Reserve Credit Card Scam Uses Fake Visa Card Offer To Steal Your Money
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.