What Is Citadel Malware Reveton Ransomware?
Citadel Malware is a group which produces and supplies malware as well as a name for malware distributed by cyber criminals for public use. Reveton is ransomware malware created by Citadel Malware that is designed for the sole purpose of extorting money from unsuspecting online victims using credit schemes.
Reveton ransomware is also known as Trojan:W32/Reveton.
 What makes Citadel Reveton malware and “ransomware” unique is that it locks computer systems and lures victims to a drive by download site appearing like the FBI or Internet Complaint Center (IC3.gov) with a message that alleges the victims IP address was identified by the Computer Crime & Intellectual Property Section (FBI) as visiting child pornography and other illegal content. To unlock their computer, victims are instructed to pay a $100 fine (or more) to the US Department of Justice, using prepaid money card services (Green Dot Moneypak) which are compiled based upon the victims IP geo location. (Meaning the malware will look up which payment platform properly suites the computer, as well as fraudulent authority organizaion) This is where the term “ransomware” derives from, as ransomware is malware which prevents users from accessing their computer unless a penalty fine is paid.
What makes Citadel Reveton malware and “ransomware” unique is that it locks computer systems and lures victims to a drive by download site appearing like the FBI or Internet Complaint Center (IC3.gov) with a message that alleges the victims IP address was identified by the Computer Crime & Intellectual Property Section (FBI) as visiting child pornography and other illegal content. To unlock their computer, victims are instructed to pay a $100 fine (or more) to the US Department of Justice, using prepaid money card services (Green Dot Moneypak) which are compiled based upon the victims IP geo location. (Meaning the malware will look up which payment platform properly suites the computer, as well as fraudulent authority organizaion) This is where the term “ransomware” derives from, as ransomware is malware which prevents users from accessing their computer unless a penalty fine is paid.
That is not the only issue with Reveton Ransomware. Reveon Ransomware also downloads to computer systems and hides, waiting for credit systems to be initiated to steal private credit information and numbers. Reveon Ransomware is used in a lot of credit card schemes to extort money.
Reveton ransomware symptoms
- Desktop and operating system locks up
- Fraudulent authority message appears with a fraudulent claim
- Internet redirects to a fake FBI or Internet Complaint Center (IC3) page and demands a payment to unlock your computer sytem (online complaint bureau depends on user IP location)
How to remove Citadel Malware Reveton Ransomware
There are many ways to remove Citadel ransomware depending on the progression of the parasite. If you can access the internet while infected it is suggested to proceed to option 1 and install the free version of Malwarebytes to scan and remove the ransomware virus from your computer. If you know your way around Window’s OS, it is suggested to chose the manual removal option (option 2). For other issues a solution to remove Reveton is to restore your computer to a date and time before infection (option 3).
For additional removal steps and symptoms please check out the FBI Moneypak removal steps.
1. Malware Removal Sofware
Malwarebytes offers a free and paid version. The free version has been publicly documented to remove Citadel’s malware and the paid version will ensure that ransomware infections will never happen to your system again.
2. Manual Removal Instructions
The hardest of the manual removal process part is finding the appropriate dll file to remove. Citadel’s malware is mass distributed (we all could go acquire it right now online for free if we wanted) and because of this the exact dll. file for Reveton ransomware can be hard to locate.
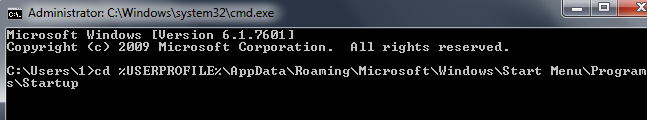
Windows command
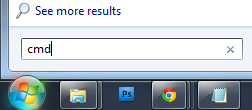
In the command prompt displayed, type in one of the following commands below and press Enter, depending on your operating system:
Windows XP: cd %USERPROFILE%\Start Menu\Programs\Startup
Windows 7: cd %USERPROFILE%\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
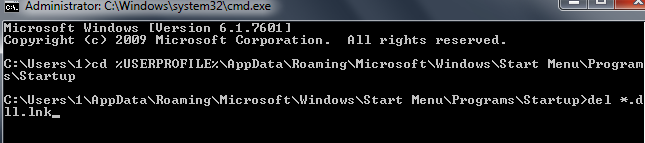
Remove the .dll file
Upon execution, Reveton malware will create the following which must be removed:
Search and remove the .dll file. If you can not find the correct file (which can be tricky) malware removal is strongly suggested.
<reveton_filename> can be a sequence of random letters and numbers.
- On Windows XP
%USERPROFILE%\Start Menu\Programs\Startup\<reveton_filename>.dll.lnk - On Windows 7
%USERPROFILE%\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\<reveton_filename>dll.lnk
Other manual removal options
These following removal steps are taken from the FBI Moneypak virus removal instructions essentially the same virus, just different progressions for geographic locations).
1. Open Windows Start Menu and type %appdata% into the search field, press Enter.
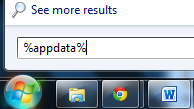
2. Navigate to: Microsoft\Windows\Start Menu\Programs\Startup
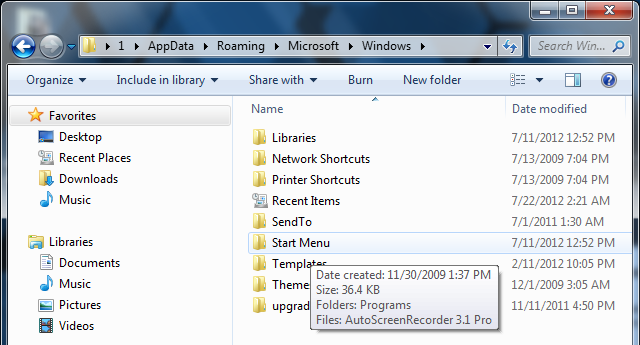
3. Remove ctfmon (ctfmon.lnk if in dos) – this is what’s calling the virus on startup
4. Open Windows Start Menu and type %userprofile% into the search field and press enter.

5. Navigate to: Appdata\Local\Temp
6. Remove rool0_pk.exe
7.Remove [random].mof file
8. Remove V.class
The virus can have names other than “rool0_pk.exe” but it should appear similar, there may also be 2 files, 1 being a .mof. Removing the .exe file will fix FBI Moneypak. The class file uses a java vulnerability to install the virus, removal of V.class is done for safe measure.
All FBI Moneypak files:
The files listed above are what causes FBI Moneypak to function. To ensure FBI Moneypak is completely removed via manually, please delete all given files. Keep in mind, [random] can be any sequence of numbers or letters.
%Documents and Settings%\[UserName]\Desktop\[random].lnk %Program Files%\FBI Moneypak Virus %AppData%\Protector-[rnd].exe %AppData%\Inspector-[rnd].exe %Windows%\system32\[random].exe %appdata%\[random].exe %Documents and Settings%\[UserName]\Application Data\[random].exe %UserProfile%\Desktop\FBI Moneypak Virus.lnk %Documents and Settings%\All Users\Application Data\FBI Moneypak Virus %AppData%\result.db %CommonStartMenu%\Programs\FBI Moneypak Virus.lnkKill ROGUE_NAME processes:
Access Windows Task Manager (Ctrl+Alt+Delete) and kill the rogue process. Please note the infection will have a random name for the process [random] which may contain a sequence of numbers and letters (ie: USYHEY347H372.exe).
[random].exe
Remove Registry Values
To access Window’s Registry Editor type regedit into the Windows Start Menu text field and press Enter.

HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\[random].exe HKEY_LOCAL_MACHINE\SOFTWARE\FBI Moneypak Virus HKEY_CURRENT_USER \Software\Microsoft\Windows\CurrentVersion\Policies\System ‘DisableRegistryTools’ = 0 HKEY_LOCAL_MACHINE \SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system ‘EnableLUA’ = 0 HKEY_CURRENT_USER \Software\Microsoft\Windows\CurrentVersion\Internet Settings ‘WarnOnHTTPSToHTTPRedirect’ = 0 HKEY_CURRENT_USER \Software\Microsoft\Windows\CurrentVersion\Policies\System ‘DisableRegedit’= 0 HKEY_CURRENT_USER\Software\FBI Moneypak Virus HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Inspector’ HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FBI Moneypak Virus HKEY_CURRENT_USER \Software\Microsoft\Windows\CurrentVersion\Policies\System ‘DisableTaskMgr’ = 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\protector.exe HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\Inspector %AppData%\Protector-[rnd].exe HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\WarnOnHTTPSToHTTPRedirect 0 HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings\ID 4 HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings\net [date of installation] HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system\ConsentPromptBehaviorAdmin 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system\ConsentPromptBehaviorUser 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system\EnableLUA 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AAWTray.exe HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AAWTray.exe\Debugger svchost.exe HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AVCare.exe HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AVCare.exe\Debugger svchost.exe HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AVENGINE.EXE HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AVENGINE.EXE\Debugger svchost.exe HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableRegistryTools” = 0 HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableTaskMgr” = 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “ConsentPromptBehaviorAdmin” = 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “ConsentPromptBehaviorUser” = 0 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “EnableLUA” = 0
3. System Restore
Start Menu Restore
 Standard directions to quickly access Window’s System Restore Wizard (rstrui).
Standard directions to quickly access Window’s System Restore Wizard (rstrui).
1. Access windows Start menu and click All Programs.
2. Click and open Accessories, click System Tools, and then click System Restore.
If you are prompted for an administrator password or confirmation, type the password or provide confirmation.
3. Restore your computer to a date and time before infection.
Safe Mode With Command Prompt Restore
If you can not access your operating system, this is the suggested step.
1. Restart/reboot your computer system. Unplug if necessary.
2. Enter your computer in “safe mode with command prompt”. To properly enter safe mode,repeatedly pressF8 upon the opening of the boot menu.
3. Once the Command Prompt appears you only have few seconds to type “explorer” and hit Enter. If you fail to do so within 2-3 seconds, the FBI MoneyPak ransomware virus will not allow you to type anymore.
4. Once Windows Explorer shows up browse to:
- Win XP: C:\windows\system32\restore\rstrui.exe and press Enter
- Win Vista/Seven: C:\windows\system32\rstrui.exe and press Enter
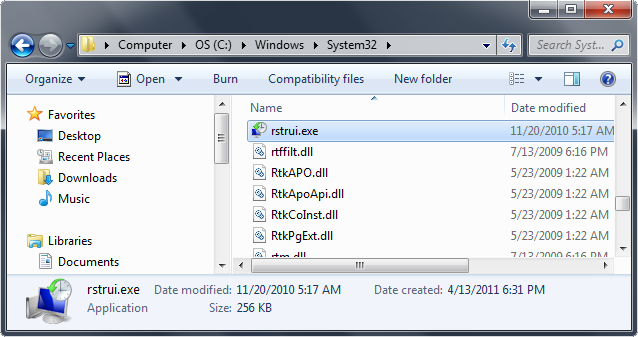
5. Follow all steps to restore or recover your computer system to an earlier time and date, before infection to complete.
More information on Window’s system restore: http://botcrawl.com/how-to-restore-microsoft-windows-vista-microsoft-windows-xp-and-microsoft-windows-7/
http://windows.microsoft.com/en-US/windows-vista/System-Restore-frequently-asked-questions
Multiple ransomware attacks .gif
Here is an example of what multiple ransomware attacks look like in different countries.
- Cloudflare Says Anthropic Mythos Can Chain Bugs Into Working Exploits
- DigiCert Revokes 60 Code Signing Certificates After Support Malware Incident
- ClickUp Data Leak Shows $4B Came Before Customer Security for Over a Year
- Fast16 Malware Targeted Microsoft Windows Engineering Software Before Stuxnet
- eBay DDoS Claim Follows Marketplace Outage Reported by Users
Sean Doyle
Sean is a tech author and security researcher with more than 20 years of experience in cybersecurity, privacy, malware analysis, analytics, and online marketing. He focuses on clear reporting, deep technical investigation, and practical guidance that helps readers stay safe in a fast-moving digital landscape. His work continues to appear in respected publications, including articles written for Private Internet Access. Through Botcrawl and his ongoing cybersecurity coverage, Sean provides trusted insights on data breaches, malware threats, and online safety for individuals and businesses worldwide.
















14 Comments
at the part were you tell me to type in del *.dll.lnk and press enter this pops up the file name was incorrect
So once i do that free scan and after its done scanning and i click the button where it says remove the stuff then after i restart like it says, am I in the clear??
You should be fine, I can not tell you this with 100% certainty though.
If you would like to try a free “second opinion scanner” I suggest performing a scan with HitmanPro by Surfright (You can also purchase HitmanPro here).
If you still feel any uncertainty you could also perform a system recovery or reset (depending on your version of Windows), as well as change your user account credentials and settings… or delete the ‘infected’ Windows user account entirely.
If you wish to prevent these types of infections in the future you can purchase Malwarebytes Pro with real-time protection, opposed to the scan-only free version.
Did the restore it worked ran the malware, I do I know that it is completely off the computer
How do I know??
A suggestion to ensure removal is complete is to install the free version of Malwarebytes, perform a scan, and search through the results (since Malwarebytes does detect and remove FBI related malware). Once you are satisfied with your results you may remove the free version of Malwarebytes or continue to use it for scans in the future.
The free version of AVG has been documented to detect and remove the infection as well.
The virus took control of our server and blocked the screen with the message demanding money. The server runs Windows Business Server 2003. I can’t access the server using remote desktop connection. Also, DOS program on workstations won’t open. Is that because the server is blocked? I hope someone can help.
Thanks, Harry
restore system worked. thanks Tim
Glad to hear you got rid of it, I was just about to reply to your previous comment with the information below.
1. Open Windows Start Menu and type %appdata% into the search field, press Enter.
2. Navigate to: Microsoft\Windows\Start Menu\Programs\Startup
3. Remove ctfmon (ctfmon.lnk if in dos) – this is what’s calling the virus on startup
4. Open Windows Start Menu and type %userprofile% into the search field and press enter.
5. Navigate to: Appdata\Local\Temp
6. Remove rool0_pk.exe
7.Remove [random].mof file
8. Remove V.class
The virus can have names other than “rool0_pk.exe” but it should appear similar, there may also be 2 files, 1 being a .mof. Removing the .exe file will fix the virus. The class file uses a java vulnerability to install the virus, removal of V.class is done for safe measure.
Source: http://botcrawl.com/how-to-remove-the-fbi-moneypak-ransomware-virus-fake-fbi-malware-removal/
I am running Malware bytes and it finds the Citadel malware and quarantines it, however the file when quarantined or deleted, keeps reproducing it’s self. File is ctfmon.lnk. How do I stop it? Thanks Tim
How To Remove Citadel Malware Reveton Ransomware (Fake IC3, FBI Malware) http://t.co/cNfXaaAp cc @iamugendi @dungdungu
None of these methods have worked for me. As soon as I go back to explorer the FBI screen is back.
If you performed a restore via Safe Mode With Command Prompt you will have no issue.
It’s the last option under 3. System Restore. I suggest you try it out.
Whoever created this – THANKS! Did the restore and it worked perfectly!